1. Introduction
Along with the popularization of mobile Internet and Internet of Things, a large quantity of ordinary users and sensor nodes have become involved in the perception and collection activities around the state of the environment. Hence, brand-new crowd sensing data emerge as the times require, and researchers are beginning to be concerned about the influence of such data on human life [
1,
2,
3,
4,
5], including medical treatment, social networks, environmental monitoring, transportation, etc. The sensor data may contain private user details, especially for sensors that can collect location coordinates for Location Based Service (LBS). The cloud party has brought vast amounts of sensitive data together after data owners outsource their databases to the cloud server provider. Therefore, the inappropriate use of crowd sensing data, which not only contain user locations but also personality habits, health condition, social status and other sensitive information, brings great challenges to data confidentiality and user privacy [
6,
7,
8].
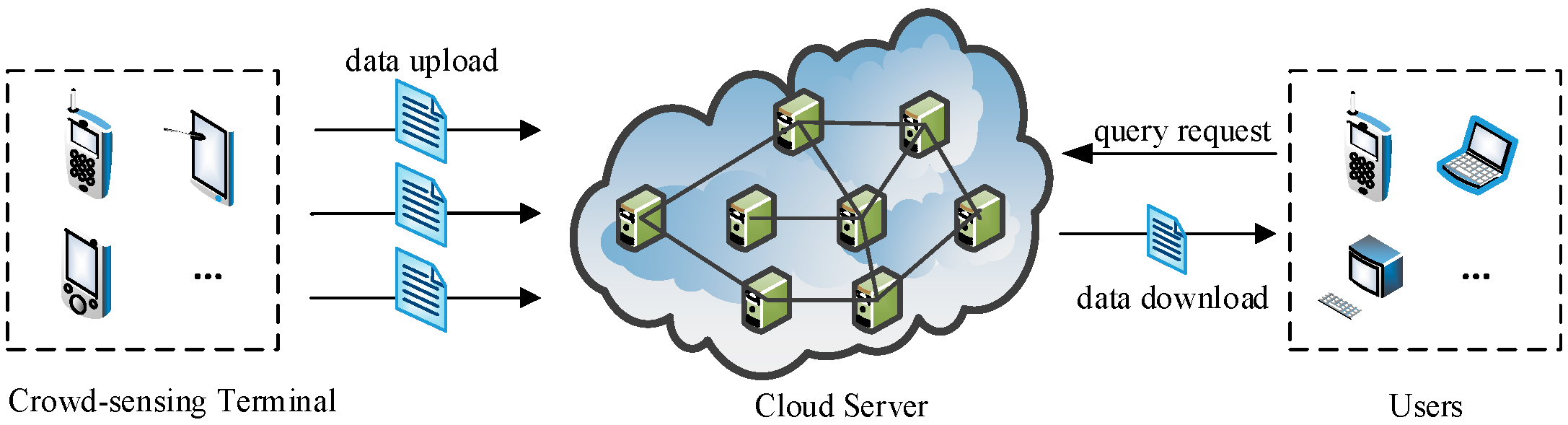
To protect the confidentiality of the location data in the cloud, one straightforward way is to encrypt data by the data owner (Owner) before outsourcing. In addition, to preserve user privacy, authorized users (Users) need to perform a complex series of encryption and decryption operations during query execution. However, this approach cannot be directly applicable to crowd sensing data because the mobile terminals in crowd sensing networks fail to perform the current big computation limited to compute and storage capability. More importantly, mobile terminals, which are the source of crowd sensing data, are mutually-distrusting as data owners. This situation makes up a totally different service structure, as depicted in
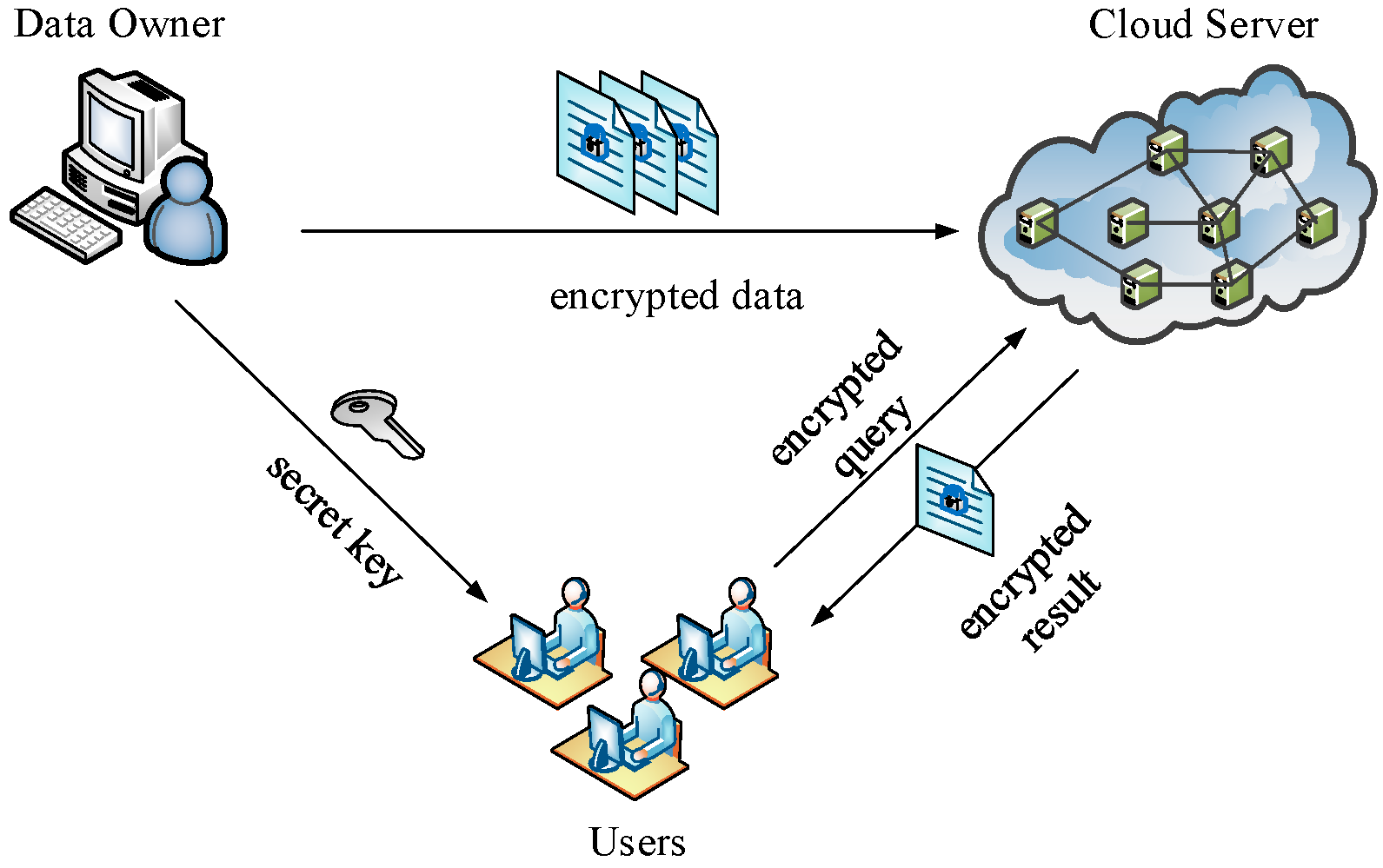
Figure 1. We call it Multi Owners and Multi Users (MOMU) cloud services structure based upon crowd sensing data, referred to as MOMU structure. It is different from the traditional Single Owner and Multi Users (SOMU) structure portrayed in
Figure 2, in which only one data owner has a large number of data and outsources them to the cloud, then authorized users access those data for issuing queries.
In this paper, we focus on the secure nearest neighbor (SNN) problem on crowd-sensing location data (MOMU structure is a typical structure in the applications of crowd sensing [
9,
10]), since LBS is the current hot topic in the study of big data [
11,
12,
13], furthermore, nearest neighbor (NN) queries are fundamental in LBS [
14,
15]. In the past few years, researchers have proposed various methods [
15,
16,
17,
18,
19] to address the SNN problem in SOMU model. The work in [
16] uses a new encryption scheme (ASPE) to preserve scalar product between the query vector and any vector for distance comparison, which is sufficient to find NN. Hu et al. [
17] propose a solution based on privacy homomorphism encryption scheme (ASM-PH). Instead of finding exact NN, [
15] allows a cloud party to approximate it based on secure Voronoi diagram (SVD). Similar to [
15], the work in [
18] also uses Voronoi to raise efficiency. Elmehdwi et al. [
19] propose a novel protocol over encrypted data based on Paillier cryptosystem [
20], which can calculate encrypted distance between data record and query record in a secure way.
One important observation about these prior works is that the data owners are all assumed to be a single trusted party. Hence, in the MOMU structure, it is impractical to share the secret key between all the data owners and users just like existing solutions [
15,
16,
17,
18,
19] because the compromise of any data owner would be a threat to data security of other owners. For instance, in a cloud system based on key-sharing, if an owner colludes with the cloud, the other owners’ data stored in cloud will be leaked because they could be decrypted with a sharing key. A natural idea is that multiple data owners could use their own unique keys. However, the SNN query across the data encrypted by different keys is another challenge (e.g., data availability, key management, etc.). In addition, the mobile terminals in crowd sensing networks cannot fulfill the requirements for computation and storage capability of the end-user in traditional methods. Therefore, the methods based on SOMU structure cannot be applied to crowd-sensing cloud server directly.
To address those challenges, our insight is that there is generally a proxy server of service providers in a cloud environment. Thus, we can use the proxy server to share the hard work for the end-user. In order to ensure availability of encrypted data by different keys, we also provide a series of protocols of secure two-party computation coordinating to the proxy architecture, which not only protects the confidentiality of the location data from various data owners but also allows the specified user to perform the SNN query efficiently. In summary, our paper makes the following contributions:
We propose a Security Architecture over MOMU Cloud Service System (SAMOMU) model based on partition of public cloud and proxy server to meet the security and performance requirements of MOMU structure.
In the SAMOMU model, a method to solve the SNN problem is presented by combining SVD method and a series of secure two-party computation protocols.
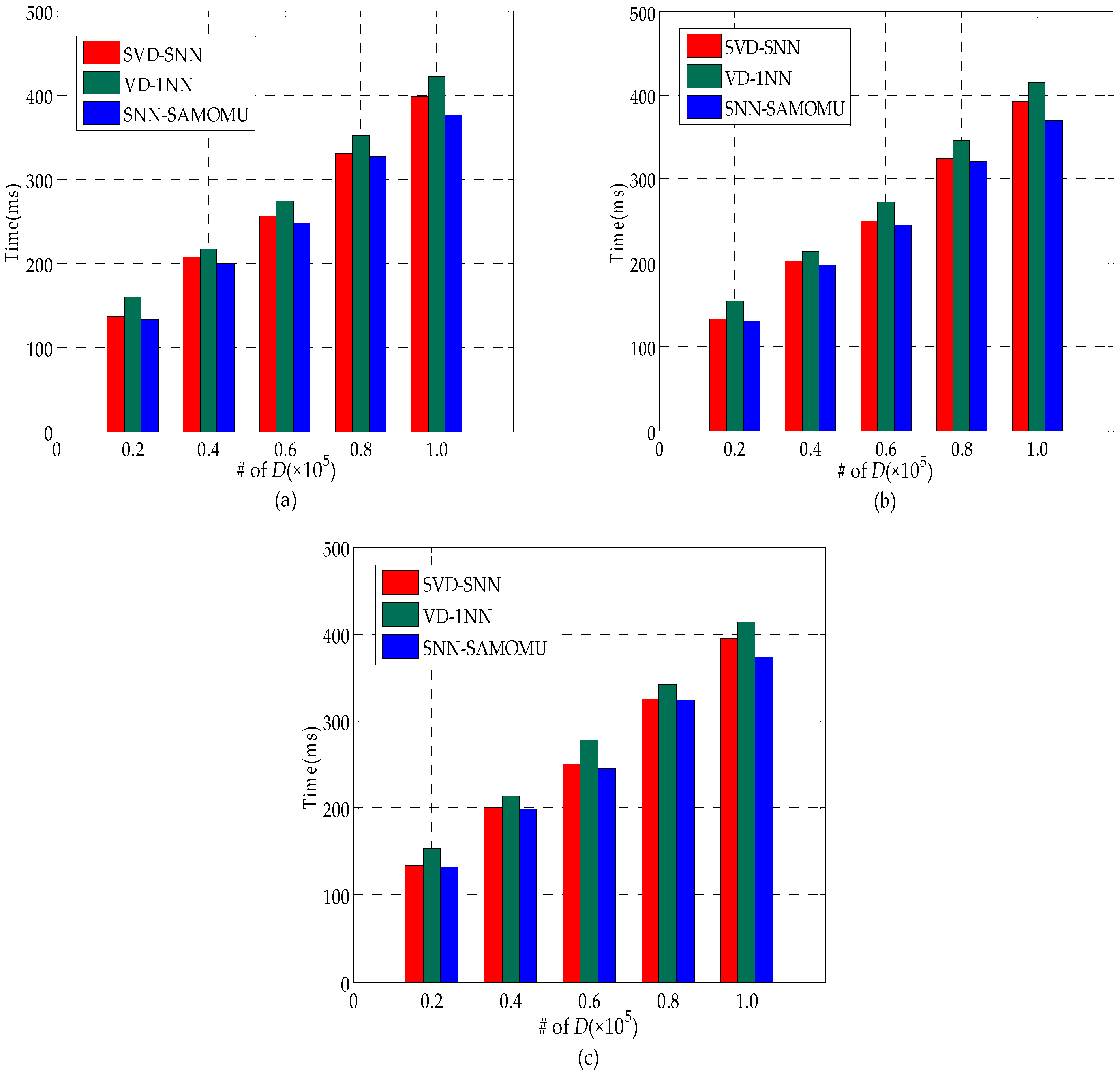
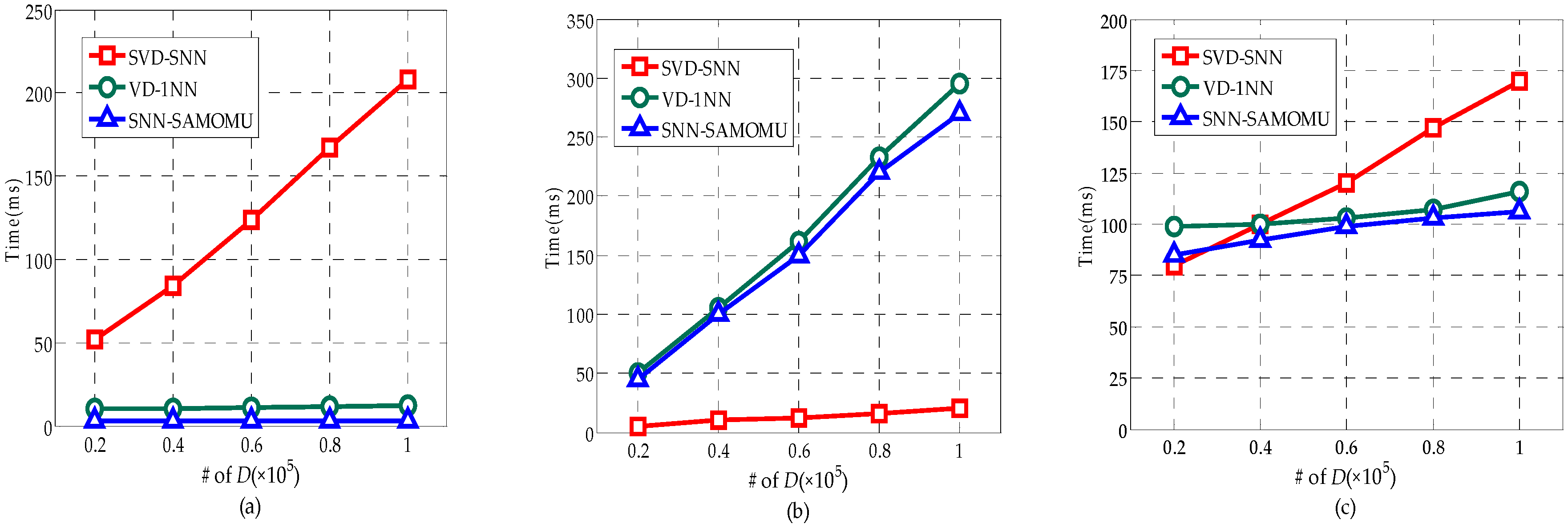
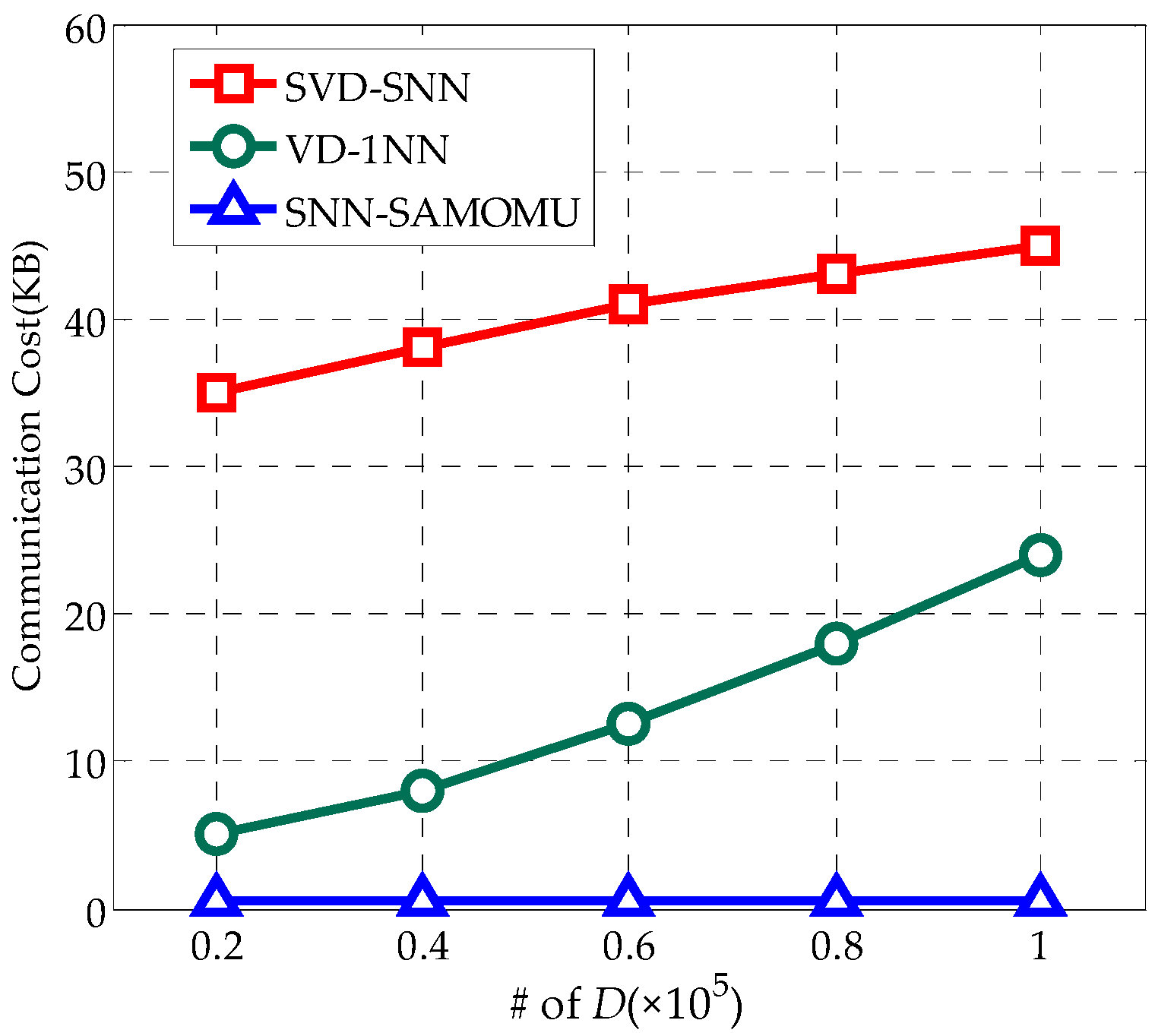
We present an extensive experimental evaluation of the proposed scheme, which shows that the proposed method has good performance for crowd-sensing data.
The remainder of this paper proceeds as follows. Related works are surveyed in
Section 2. We define our system model and design goals in
Section 3. A set of basic security protocols which are utilized in our scheme are provided in
Section 4.
Section 5 presents the details of our scheme. The security and performance analysis are carried out in
Section 6. Finally,
Section 7 concludes the paper and discusses potential future directions.
2. Related Works
In this section, we first review several nearest neighbor query methods for location privacy in LBS, and then we present an overview of the existing SNN techniques.
2.1. Query Location Privacy in LBS
In traditional LBS model, the methods should ensure location privacy in the sense that the user does not reveal any information about his location to the LBS provider. In this case, LBS server acts as the role of data owner. As a consequence, there is a simpler security requirement compared with the SNN query in the cloud, which focuses mainly on privacy preserving for the users.
In general, several main techniques for location privacy have been investigated in current studies. The first is the cloaking regions method [
21,
22], which assumes a trust anonymous party between the user and the server for transforming actual locations into vague locations. Obviously, the anonymizer becomes a communication bottleneck and a vulnerable point of attack. To count this privacy attack, Gao et al. [
23] propose a distributed structure for location privacy protection without a centralized anonymous server. Another category of work relies on Private Information Retrieval (PIR) [
24] to provide strong location privacy. This technique allows users to retrieve an object stored by a server without revealing which record he is retrieving. However, these PIR-based solutions [
25,
26] are still not efficient enough to be implemented on a real system.
2.2. Existing SNN Techniques
Existing SNN techniques generally rely on SOMU model, which only contains a single trusted data owner, as depicted in
Figure 2. Compared to the MOMU model, the significant difference is: the MOMU model involves multiple mutually-distrusting data owners.
In the methods [
15,
16,
17,
18,
19] based on SOMU model, the data owner outsources his database and DBMS functionalities (e.g., NN query) to the cloud server providers where only trusted users are allowed to query the host data. Wong et al. [
16] proposed a new encryption scheme (ASPE) that preserves the relative distances of all the database point to any query point that is sufficient to find NN. ASPE transforms data points and queries with secret matrices, which are symmetric keys for the encryption scheme. Thus, it must be shared with both the data owner and query users. As an alternate, Hu et al. [
17] proposed a method based on Privacy Homomorphism (ASM-PH) encryption scheme. During query processing, data owner sends the encrypted shadow index to user, and user needs to traverse the index locally to compute the distance between query point and an indexed point with the help of server. However, the methods in [
16,
17] are not secure because they are prone to chosen-plaintext attacks [
15].
To further improve the query performance, Yao et al. [
15] designed a novel SNN method based on secure Voronoi diagram (SVD). Instead of return exact NN, they allow a cloud server to return a relevant data partition. What is more notable, is that the work in [
18] also used Voronoi and order-preserving encryption (OPE) to solve the SNN problem accurately. Although it can provide exact result, the solution incurs expensive overhead of computation and communication on the end-user. More importantly, the encryption schemes used in [
15,
18] are symmetric, and both the data owners and users have to share the secret key, which make it impractical in MOMU structure where there are multiple mutually-distrusting data owners.
Recently, Elmehdwi et al. [
19] proposed a number of novel protocols over encrypted data based on Paillier cryptosystem [
20], which can further increase security during query execution. They assume the existence of two semi-honest cloud servers
P1 and
P2 such that the encrypted data is known only to
P1, whereas the secret key is just revealed to
P2. Using the secure protocols,
P1 collaborate with
P2 for the final result after receiving an encrypted query from the user. However these protocols cannot be put into use for inefficiency.
Crowd-sensing cloud server is based on the MOMU structure, in which the number of data owners increases and computing power of end-users decreases compared with SOMU structure. These changes about objective conditions cause the changes of the security and performance requirements. Hence, the methods above do not apply to MOMU structure in which there are multiple mutually-distrusting and the end-user cannot afford huge costs for compute or storage.
3. System Model and Design Goals
In this section, we formalize the system model, security and privacy requirements, and describe our design goals.
3.1. System Model
The cloud service system based upon crowd-sensing data is actually aggregations of the crowd-sensing system and the cloud system. The terminals in this system are divided into two kinds of entities in the function: the data owner (Owner) and the data user (User). As a data owner, the terminal will outsource his/her data to the cloud for efficient storage and management. In fact, there is generally a proxy server of service providers in a cloud service based on crowd-sensing data. With the crowd-sensing data in VANET, for example, the data collected through VANET are uploaded to the cloud and governed by the traffic administrative department while the users such as automobile manufacturers, garages and insurance companies need to access the relevant data. Nowadays, large companies usually set up their own proxy server for different types of server. In this scenario, the traffic administrative department can be viewed as a trusted authority (TA). When a user wants to check the information about insurance and vehicle maintenance, he has to access them using the proxy of the insurance company and the garage, respectively. This is similar to the social network, which may contain a variety of services in regard to foods, sports, garments and so on, a user acquires different kinds of data through the corresponding proxy servers of service providers. To this end, we propose a Security Architecture over MOMU Cloud Service System (SAMOMU), as depicted in
Figure 3.
Our system consists of five types of generic entities: Data Owners (Owners), Data Users (Users), Cloud Server (CS), Proxy Server (PS) and Trusted Authority (TA).
- (1)
Data Owners (Owners): We assume that our system requires m Owners, which are generally played by the sensor nodes, mobile phones and vehicle terminals, denoted as Own = {O1, O2, …, Om}. Data are generated by Owners, encrypted using their secret key and then outsourced to CS for storage.
- (2)
Data Users (Users): The system assumes there are n Users with limited computation and communication resources, denoted as Usr = {U1, U2, …, Un}. Note that the terminals that act as Owners could also take up positions as Users. They forward queries to the CS via the PS for the nearest neighbor.
- (3)
Cloud Server (CS): The CS stores all the encrypted data outsourced from Owners. After received NN requests from the PS, the CS interacts with the PS to process the data and returns the results to the Users.
- (4)
Proxy Server (PS): The PS takes on the task of providing those users with proxy services. In reality, much useful information is distributed among the crowd sensing networks, hence the PS normally caches the parsing results or extracts the metrics of interest. In SAMOMU model, the PS will host part of the computing task for Users.
- (5)
Trusted Authority (TA): TA is assumed to be trusted by all the other entities in the system to distribute and manage all the private keys, and to generate some parameters involved in the system.
Note that our systems are scalable and efficient for users. Specifically, users do not need to know the identities of other users or the total number of users involved in computation. Most importantly, because of the PS, the computation is non-interactive to users—users only need to outsource encrypted data initially and remain offline until retrieving encrypted outputs. It has been proven that the traditional single server model for secure outsourced computation cannot completely eliminate interactions between the user side and the server side (due to the impossibility of program obfuscation). The defect of this architecture is that the PS is likely to become a Single Point of Failure (SOF). However, in the real world, all service providers have the separated proxy server, which is totally independent of each other. Furthermore, service providers can adopt the hot-standby technique for solving the SOF from a view of engineering. Although the providers need to increase investment in infrastructure, it would make for a pleasant user experience in return. This is also the basic motivation of the paper.
3.2. Security and Privacy Requirements
In our security and privacy model, we assume PS and CS are both semi-honest (i.e., honest-but-curious). Meanwhile, we also assume these two servers are non-colluding. It means that neither of these two servers intends to corrupt users’ data or computation process to prevent users from utilizing data correctly, but each server will try to learn the content of users’ data (i.e., inputs), intermediate or final results of the computation without colluding with another server.
We remark that those assumptions are not initiated by our work, but rather derive from the related research [
19,
27,
28,
29]. According to the requirements of crowd-sensing scenario, the SAMOMU partitions server functions under the management of the TA. Actually, the security of our system is stronger than the Two-Clouds architecture [
19], because the TA would be charge of the key management, the collusion between the PS and the CS cannot breakdown the full security of our system. To provide a flexible tradeoff between security and performance, we define the concrete data confidentiality and query privacy to against adversary
Adv as follows.
Definition 1 (Data Confidentiality Definition). Upon completion of the SAMOMU model, Adv cannot learn any plain data stored in the CS when Adv did not collude with any Owners. If an Owner was captured by Adv, the adversary would not get any assistance to obtain sensor data generated by other Owners.
Definition 2 (Query Privacy Definition). Neither the query point nor the result for users should be reveal to the Adv.
To satisfy these privacy requirements, the active adversary
Adv in our model has the following attacking abilities:
Adv may eavesdrop all the communication links to get the encrypted data. In addition,
Adv may compromise CS, some Users and Owners simultaneously, but subjects to the following restrictions: (1)
Adv cannot compromise the CS and the PS at the same time; and (2) in a process of query,
Adv cannot compromise the User who launched this query. Moreover, we do not aim to protect access pattern in this paper due to the extremely high complexity, i.e., to protect it, the algorithm has to “touch” the whole dataset [
24].
3.3. Design Goals
In order to achieve the SNN query under SAMOMU model, our method will fulfill privacy and performance guarantees as follows:
Data confidentiality and query privacy: The data confidentiality and query privacy as described in the Definitions 1 and 2 should be guaranteed.
Reduce the end-users’ cost: The end-users in SAMOMU model generally have limited computation and communication resources, thus our method should be designed for reducing the end-users’ cost by using the PS efficiently.
Access Control: A large number of parties are involved in the system, therefore control of the user’s access request by attribute-based encryption (ABE) [
30] is necessary.
We list the main technologies used in our method in
Table 1; these cannot apply to our method directly, and the improvements and combinations of them are technical contribution of our work.
4. Basic Security Protocols
In this section, we present a set of secure two-party computation protocols that will be used as sub-routines while constructing our proposed scheme in
Section 5. We firstly introduce an encryption scheme using secret-sharing [
31], based here to build our protocols.
4.1. The Encryption Scheme Based on Secret-Sharing
Under secret sharing, the encryption scheme used in [
31] aims to split a plaintext into a secret key and a ciphertext for data confidentiality. The concrete algorithm is showed in Definition 3.
Definition 3. The secret sharing encryption process consists of two steps:
Step 1 (Key Generation). Generate a public parameter PP = <g, n> in the follow way: choose randomly two prime numbers p and q, then compute n = p
× q, = (p − 1)·(q − 1). Choose randomly a positive number g that is co-prime with n. Generate randomly a secret key sk = {m, a} (0 < m, a < n).
Step 2 (Share Computation). Given a sensitive value x, choose randomly a number r, the encrypted value Esk,r(x) is given by Esk,r(x) = x·(mgra mod n)−1 mod n, where ( )−1 denotes the modular inversion. To recover x, one needs all shares sk, r and Esk,r(x) and compute Dsk,r(Esk,r(x)) = Esk,r(x)·(mgra mod n) mod n. We refer the reader to [31] for correctness and security proof of this scheme. 4.2. Secure Two-Party Computation Protocols
We present a set of protocols based on the encryption scheme above. All of the below protocols are considered under two-party semi-honest setting: Data Normalization (DataNorm) protocol, Secure Distance (SecDist) protocol, Secure Compare (SecComp) protocol, Secure Minimum of k Numbers (SecMink) protocol.
Data Normalization (DataNorm). We assume that a party
P1 holds a secret key
sk1 = {
m1,
a1}, a random number
r1, a target key
sk2 = {
m2,
a2} and a target number
r2 while a party
P2 has encrypted value
. The goal of the DataNorm protocol is to compute the encryption of
x, which is encrypted by
sk2 and
r2. At the end, the output is known only to
P2. In our query scheme described in
Section 5, we will use the DataNorm protocol to make a data normalization over the encrypted data, although those data were encrypted using different keys of multiple data owners. Thanks to this, we can ensure availability of encrypted data. The protocol is shown in Algorithm 1.
| Algorithm 1. DataNorm (, {sk1,r1}, {sk2,r2}) − |
Require: P1 has sk1 = {m1, a1}, sk2 = {m2, a2},r1, r2; P2 has - (1)
P1:
- (a)
Pick two random numbers m3, a3, r3 - (b)
p ← a3−1(r2a2 − r1a1) mod - (c)
q ← m1m3pm2−1 mod n - (d)
s ← ( mod n)−1 - (e)
Send p, q, s to P2
- (2)
P2:
- (a)
← ·q·sp
|
Definition 4 (Correctness).
If DataNorm protocol presented in Algorithm 1 is correct, a party P2 can get the encryption of x, which is encrypted by sk2 and r2.
Proofs of Correctness.
We can use
sk2 and
r2 to decrypt ciphertext of
P2, converting from
back to plain text
x. The process is as follows.
□
Secure Distance (SecDist). Consider a party
P1 with secret key
sk, a secret share
r and a party
P2 with private input
Esk,r(
X),
Esk,r(
Y). Here,
X and
Y are two-dimensional vectors where
Esk,r(
X) ≤
Esk,r(
x1),
Esk,r(
x2)>, and
Esk,r(
Y) = <
Esk,r(
y1),
Esk,r(
y2)>. The goal of the SecDist protocol is to compute
Esk,r(
), where
denotes the Euclidean distance between
X and
Y. During this protocol, no information regarding
X and
Y is revealed to
P1 and
P2. The SecDist protocol described in Algorithm 2 will be used as a sub-routine to construct our SNN method in
Section 5.
| Algorithm 2. SecDist(Esk,r(X),Esk,r(Y)) − |
Require: P1 has sk = {m, a}, r; P2 has - (1)
P2:
- (a)
← (Esk,r(x1) − Esk,r(y1))2 + (Esk,r(x2) − Esk,r(y2))2
- (2)
P1:
- (a)
← m2, ← 2a, ← {,}
- (3)
P1 and P2:
- (a)
← DataNorm(,{, r},{sk, r}) - (b)
P2 get
|
Definition 5 (Correctness).
If SecDist protocol presented in Algorithm 2 is correct, a party P2 can get the value , which can be decrypted by sk and r.
Proofs of Correctness.
We can use
sk and
r to decrypt ciphertext of
P2, converting from
back to plain text
. The process is as follows.
□
Secure Compare (SecComp). In this protocol, P1 holds sk = {m, a}, r and P2 holds Esk,r(x), Esk,r(y). The goal of the SecComp protocol is to compare x with y without revealing any information about x and y to P1 and P2. This protocol returns true if x > y, otherwise it returns false. The protocol is shown in Algorithm 3.
| Algorithm 3. SecComp(Esk,r(x), Esk,r(y)) → true/false. |
Require: P1 has sk = {m, a}, r;P2 has Esk,r(x) and Esk,r(y)
- (1)
P1:
- (a)
Pick a random positive number z - (b)
Esk,r(z) ← z·m·gra - (c)
Send Esk,r(z) to P2
- (2)
P2:
- (a)
t ← (Esk,r(x) − Esk,r(y))·Esk,r(z)
- (3)
P1:
- (a)
= 〈m2, 2a〉, = 〈1, 0〉
- (4)
P1 and P2:
- (a)
f ← DataNorm(t,,)
- (5)
P2:
- (a)
IF f > 0 THEN RETURN true ELSE RETURN false RETURN false
|
Definition 6 (Correctness).
If SecComp protocol presented in Algorithm 3 is correct, a party P2 will get a f > 0 iff x > y.
Proofs of Correctness. f = = (x − y)·z·1·gr·0 = (x − y)·z and z > 0, so iff f > 0 then x > y, else x < y. □
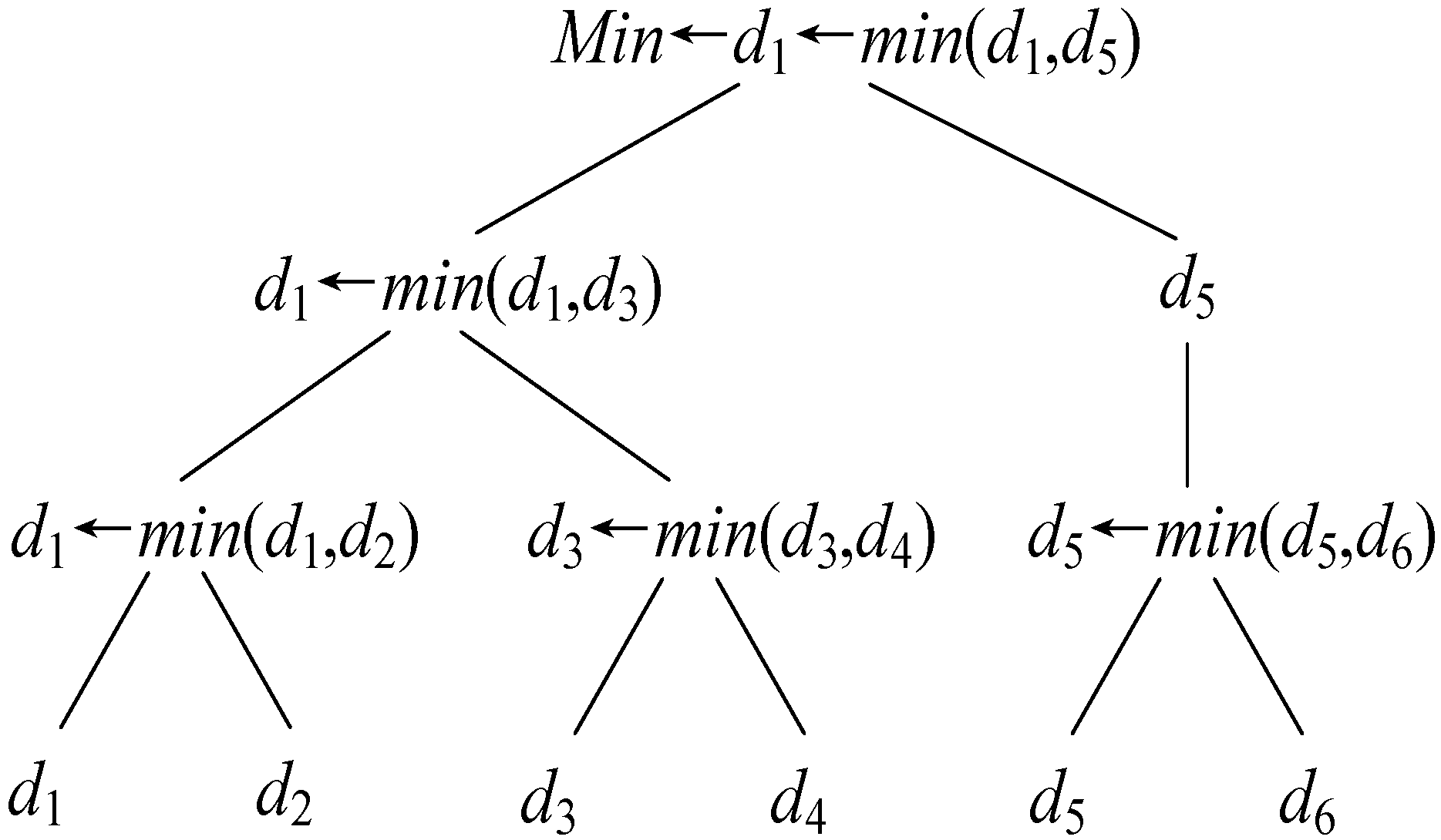
Secure Minimum of k Numbers (SecMink). We assume that
P1 has
sk = {
m,
a},
r and
P2 has
Esk,r(
x1),
Esk,r(
x2), …,
Esk,r(
xk), the goal of the SecMin
k protocol is to securely compute
Min = min(
x1,
x2, …,
xk). During this protocol, no information regarding
xi (1 ≤
i ≤
k) is revealed to
P1 and
P2. On the basis of the SecComp protocol, all the values in the SecMin
k protocol are compared in pairs using the divide-and-conquer strategy. Note that the computation complexity of SecMin
k is bounded by
O(log
2k). For instance,
P1 has
sk = {
m,
a},
r and
P2 has
Esk,r(
x1),
Esk,r(
x2), …,
Esk,r(
x6), the minimum value solving process is present in
Figure 4. The protocol is shown in Algorithm 4.
| Algorithm 4. SecMink(Esk,r(x1), Esk,r(x2), …, Esk,r(xk)) → Min. |
Require: P1 has sk = {m, a}, r; P2 has Esk,r(x1), Esk,r(x2), …, Esk,r(xk)
- (1)
P2:
- (a)
di ← Esk,r(xi), FOR 1 ≤ i ≤ k - (b)
num ← k
- (2)
P1 and P2, FOR i = 1 TO :
- (a)
FOR : IF i = 1 THEN IF SecComp(d2j−1, d2j) THEN d2j−1 ← d2j ELSE IF SecComp(d2i(j−1)+1, d2ij−1) THEN d2i(j−1)+1 ← d2ij−1 - (b)
- (3)
|
5. The Proposed SNN-SAMOMU Query Scheme
Based on the secure two-party computation protocols presented in
Section 4, we propose a SNN query scheme in SAMOMU model, which consists of the following phases: System Setup, Data Outsourcing, Access Control and Result Query.
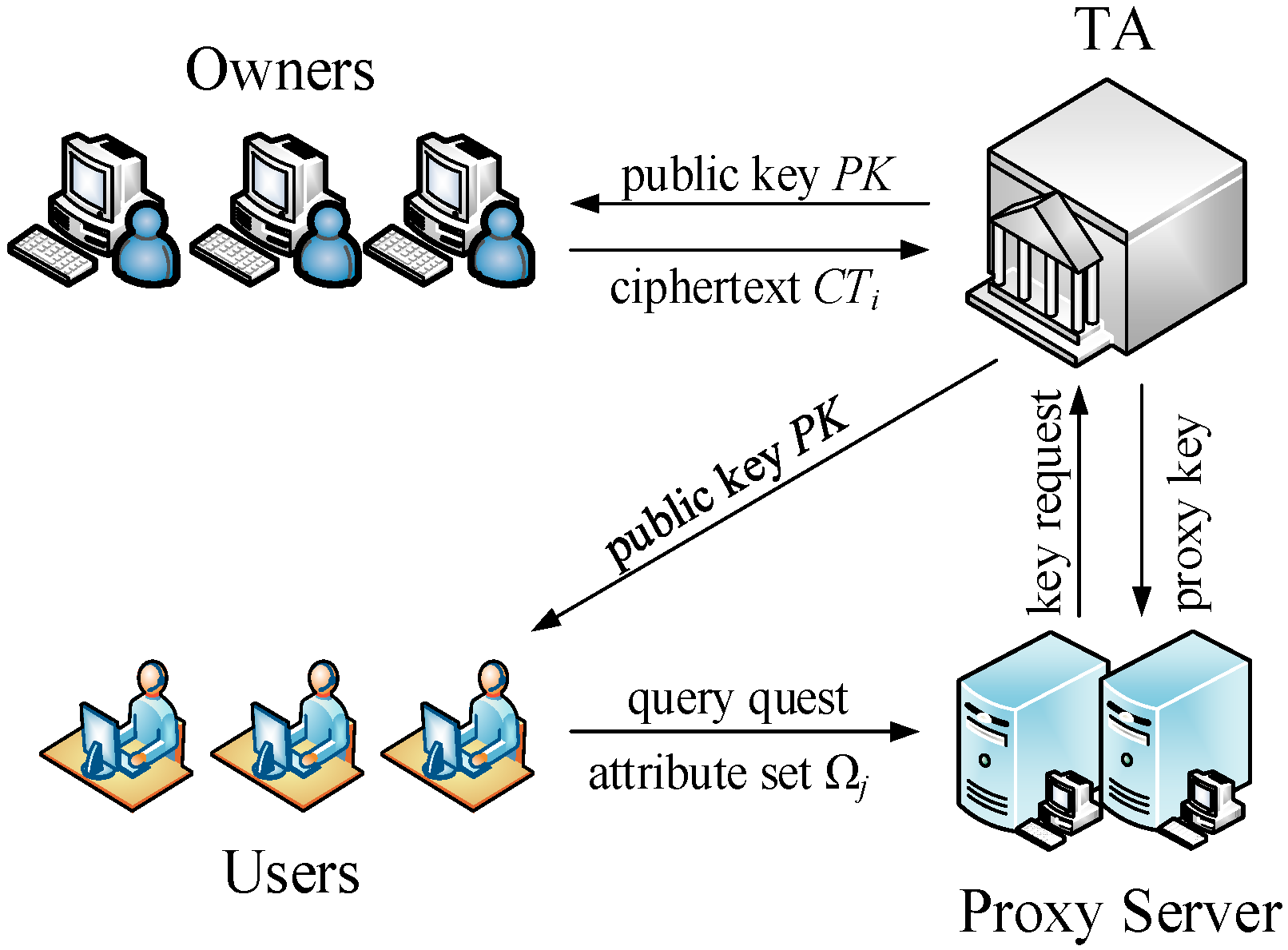
Figure 5 shows a SNN-SAMOMU query framework. Firstly, TA initializes the system, then data owners encrypt their data and outsource the corresponding encrypted data to CS while uploading random parameters to PS. To guarantee the access control, data owners use attribute-based encryption (ABE) to encrypt their own secret keys and send them to TA for management. Once the data user is authenticated by TA, PS will receive a proxy key from TA for computation. In the result query phase, PS will cooperate with CS to perform a query protocol for a result point as output to the user. Finally, we present two strategies to boost performance of our scheme.
5.1. System Setup
The TA calls the Key Generation algorithm to generate a public parameter PP, the users’ keys for m Users and the owners’ keys for n Owners. Let Key_Oi (1 ≤ i ≤ m) and Key_Uj (1 ≤ j ≤ n) denote users’ keys and owners’ keys, respectively. The TA publishes PP and sends the keys to the corresponding Owners and Users via secure channels.
5.2. Data Outsourcing
The Owners divide the data space into
K disjoint intervals through SVD algorithm [
15] locally, then use the
PP and owners’ keys to encrypt their own data and index by the encryption scheme described in
Section 4.1. Finally, the encrypted data and index are outsourced to the CS. Our data outsourcing protocol runs in the following four steps.
- (1)
The data owner Oi receives a public parameter PP and his key Key_Oi.
- (2)
Oi divides the data space, which is corresponding to his two-dimensional point set
Di, into
Ki disjoint intervals through SVD algorithm, then obtains
Ki rectangular data partition
Bi,k presented in
Figure 6, i.e.,
Di = <
Bi,1,
Bi,2, …,
>. Obviously, the rectangular partition can be uniquely identified by its lower-left (
LL) and upper-right (
UR) corners.
- (3)
Oi randomly select a number
r_
oi and encrypt
Ki data partition above through the using of
Key_Oi and
r_
oi, then obtains
Ki data items in the format shown in
Figure 7. The process of encryption is described in Algorithm 5.
| Algorithm 5. BlockEncryption. |
| Input:Key_Oi, r_oi, Ki data partition. |
| Output:Ki data items in the format shown in Figure 7. |
- (a)
WHILE(1 ≤ k ≤ Ki)
- (b)
Encrypt the LL and UR of Bi,k to get , , , - (c)
Encrypt the points contained within the scope of Bi,j to get , where - (d)
construct the data item in the format shown in Figure 7
- (e)
END WHILE
|
- (4)
Oi uploads the data items generated in Step 3 to the CS and send r_oi to the PS.
5.3. Access Control
In our method, the users have the capacity to access the encrypted data on the CS via the PS, which are uploaded by the Owners. In the real scenario, however, not all of the data can be visited by all users, only the user who was authenticated by the data owner can access the uploaded data. Hence the access policy in our system is necessary. In this paper, we use ABE [
30] to achieve access control in which the data owner has the right to set access policy, so it is suitable for the data-sharing of crowd sensing networks.
For example, in VANET, a data collector as the data owner will outsource their data to the cloud, but these data are only expected to open to the owners of the A-region and the B-car. Naturally, he informs the management department as the TA of the access condition. Before owners visiting the data stored in cloud through a proxy server of the manufacturer, the proxy needs to send the owner’s attributes (area, automaker, etc.) to management department for the permission to the specific dataset. Owners cannot visit the data in the cloud via the proxy until the condition is met.
The framework of access control is shown in
Figure 8. All data owners upload their ciphers that contain access policy to TA. After receiving a query request from the User, PS sends the user’s attributes to TA to be verified and obtains the proxy key. Once being verified by TA, PS can obtain the proxy key and perform the next phase of the query over the corresponding dataset in the cloud. The protocol sequence diagram in access control phase is shown in
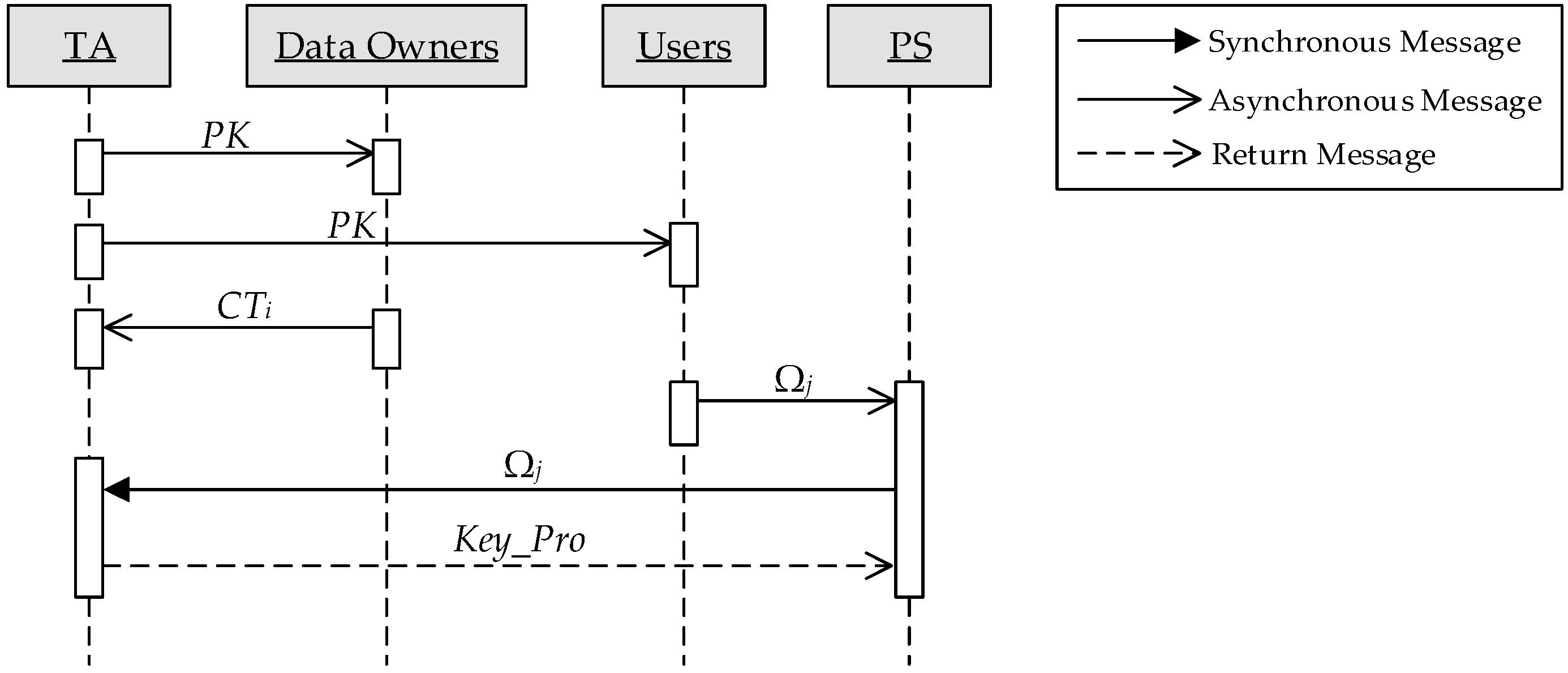
Figure 9. Specific processes are as follows:
- (1)
TA generates the public key PK and the master key MK used in ABE and publishes the PK.
- (2)
The data owner Oi with a access policy APi, PK and Key_Oi computes ciphertext CTi and sends it to TA.
- (3)
The data user Uj sends his own attributes Ωj to PS.
- (4)
PS sends Ωj to TA for requesting a proxy key.
- (5)
TA with Ωj and MK outputs the user’s attribute private key ASK[Ωj] and inserts Key_Uj into the header of the proxy key chain.
- (6)
TA takes CTi and ASK[Ωj] as input, achieves a decryption to get Key_Oi and inserts it into Key_Proj only if Ωj fully meets the access policy, otherwise output ⊥, i.e., this user does not have permission to access the data of Oi. This step is repeated until all of the dataset were visited, as a result, generates a complete proxy key chain Key_Proj.
- (7)
TA sends Key_Proj to PS.
5.4. Result Query
The data user
Uj randomly chooses a parameter
r_
uj, encrypts the query point
Q with
Key_
Uj and
r_
uj, then sends the encrypted query and
r_
uj to PS. Next, PS transfers the encrypted query to CS and then destroys it locally (This is a reasonable action, because a person would not keep all secret shares locally for the data security). Through the access control process described in
Section 5.3, the proxy gets the key chain
Key_Proj, i.e.,
Uj can visit the data in the cloud via a proxy server. Suppose
Uj can get a permission for
w dataset, then
Key_Proj = {
Key_Uj,
Key_O1, …,
Key_Ow}. Let
= {
,
, …,
} denote
w corresponding dataset in the cloud, where
is composed of
Ki data items shown in
Figure 7.
Firstly, the PS randomly selects a key skq and a parameter rq for a query. The PS and the CS view skq and rq as a normalized key and a normalized parameter for this query, respectively. The encrypted data in the CS were given normalized treatment by DataNorm algorithm. Then the PS and the CS find a block that contains the query point by the SecComp algorithm, i.e., find a block B, making xQ > xLL, yQ > yLL, xUR > xQ and yUR > yQ. Repeat the above operation over dataset of size w until output an encrypted result point to the Uj. At last Uj decrypts the ciphertext to obtain a nearest neighbor. The process of SNN query is described formally in Algorithm 6.
| Algorithm 6. SNN-SAMOMU. |
| Require: CS has EKey_O,r_o(D) and |
| PS has Key_Proj, skq and rq |
| Uj has Key_Uj and r_uj. |
- (1)
PS and CS: FOR 1 ≤ i ≤ w- (a)
CS get and by DataNorm algorithm - (b)
get the block B where the nearest neighbor locate by SecComp algorithm - (c)
WHILE (tk∈B) END WHILE - (d)
Mini ← - (e)
get δ where Mini == - (f)
Resi = and Mini’ =
- (2)
PS and CS:
- (a)
Min’ ← SecMinw(Min1’, Min2’, …, Minw’) - (b)
get ξ where Min’ == ’ - (c)
get Res = DataNorm(,{skq,rq},{Key_Uj,r_uj})
- (3)
- (4)
Uj:
- (a)
NN ←
|
5.5. Optimization
Our scheme runs on the top of encrypted data for the SNN query, whereas it does introduce inefficiency. Now we discuss two strategies to boost the efficiency: offline computation and pipeline execution.
In our protocols, the actual online computation costs with an offline phase can be much less than their costs without an offline phase. For example, consider the DataNorm primitive described in Algorithm 1. During the execution of DataNorm, P1 has to compute the encrypted value s = ( mod n)−1, where m3, a3 and r3 are random numbers in ZN. However, since these numbers are integers chosen by P1 at random, the computation of s is independent of any specific factor of DataNorm. That is, P1 can precompute the value of s during the offline phase, thus reducing its online computation time. In a similar manner, P1 and P2 can precompute certain intermediate values in the protocols.
We are able to further reduce the online execution time by adopting the technique of pipeline execution. Take the execution of SecMink for instance, P1 and P2 would like to process SecComp(d1, d2) and SecComp(d3, d4). Here the execution of SecComp(d3, d4) does not have to wait for the end of SecComp(d1, d2). Instead, they can be executed synchronously. We expect that we could further save at least one-third of the online execution time in the long run when we have a lot of SecComp operations to perform. Likewise, we could pipeline the SNN-SAMOMU protocol to save much time.
7. Conclusions
In this paper, we focus on the secure nearest neighbor (SNN) problem on crowd-sensing location data. The previous SNN techniques generally rely on the Single Owner and Multi Users (SOMU) model, which only contains a single trusted data owner. However, the previous big data system structure has changed because of the crowd-sensing data, i.e., the security and performance requirements have changed. Given all this, we proposed a SNN query scheme based on the SAMOUMU model, which is constructed by the protocols of secure two-party computation and SVD algorithm. We showed a theoretical analysis that our scheme can protect the data confidentiality and query privacy. Finally, extensive experimental evaluations are presented to show that our scheme is applicable to crowd-sensing data and significantly lower the users’ cost. As a future work, we will extend our method to k nearest neighbors and further reduce the server’s cost.