1. Introduction
This work studies the energy-distortion tradeoff (EDT) for the transmission of a pair of correlated Gaussian sources over a two-user Gaussian broadcast channel (GBC) with noiseless, causal feedback, referred to as the GBCF. The EDT was originally proposed in [
1] to characterize the minimum energy-per-source sample required to achieve a target distortion at the receiver, without constraining the source-channel bandwidth ratio. In many practical scenarios, e.g., satellite broadcasting [
2], sensor networks measuring physical processes [
3,
4] and wireless body-area sensor networks [
5,
6,
7], correlated observations need to be transmitted over noisy channels. Moreover, in various emerging applications, particularly in the context of the Internet of Things, the sampling rates are low; and hence, the channel bandwidth for transmission is much larger than the rate of the sources. Consequently, the main fundamental limitation for the communication system is the available energy per source sample. For example, in wireless body-area sensor networks, wireless computing devices located on, or inside, the human body measure physiological parameters, which typically exhibit correlations as they originate from the same source. These devices commonly have limited energy supply due to their size and are also subject to transmission power constraints due to safety restrictions, while bandwidth can be relatively large as communications takes place over short distances [
8,
9,
10]. In this application, transmission of correlated parameters measured by a single sensor to different devices can be modeled as a BC with correlated sources. As an example for such a setting, consider a sensor measuring heart rate, as well as cardiac output (volume of blood outputted from the heart per unit time), which are correlated parameters (see, e.g., [
10] (Section 2.6)), where the heart rate measurements are communicated to a smart watch (e.g., for the purpose of fitness tracking), while the cardiac output is communicated to a smart phone (e.g., for health monitoring and reporting purposes).
It is well known that for lossy transmission of a Gaussian source over a Gaussian memoryless point-to-point channel, either with or without feedback, when the source-channel bandwidth ratio is fixed and the average power is finite, then separate source and channel coding (SSCC) achieves the minimum possible average mean square error (MSE) distortion [
11] (Theorem 3). In [
1] (Cor. 1), it is further shown that SSCC is optimal also in the sense of EDT: for any target MSE distortion level, the minimal transmission energy is achieved by optimal lossy compression [
12] (Chapter 13) followed by the most energy efficient channel code [
13]. While [
1] (Cor. 1) considered unbounded number of source samples, more recent works [
14] (Theorem 9) and [
15] showed that similar observations hold also for the point-to-point channel with a finite number of source samples. Except for a few special scenarios, e.g., [
16,
17,
18] and the references therein, the optimality of SSCC does not generalize to multiuser networks, and a joint design of the source and channel codes can improve the performance.
An example for a setting in which SSCC is sub-optimal is the transmission of a pair of correlated Gaussian sources over a GBC where the bandwidths of the source and the channel match (i.e., on average, a single source sample pair is transmitted over a single use of the channel). The complete characterization of the achievable distortion pairs for this problem was given in [
19], which also showed that a joint source-channel coding (JSCC) transmission scheme is optimal while separation-based schemes cannot achieve the optimal performance. JSCC for the transmission of correlated sources over GBCs with a source-channel bandwidth mismatch was recently studied in [
20], where novel hybrid digital/analog coding schemes were proposed and shown to be superior to other schemes known in the literature. It should be noted that the transmission of correlated sources over GBCs is an important communications scenario, which applies to a vast number of practical applications, including broadcasting video [
21,
22], images [
23] and physical measurements [
24].
The impact of feedback on lossy JSCC over multiuser channels was considered in relatively few works. Several achievability schemes and a set of necessary conditions for losslessly transmitting a pair of discrete and memoryless correlated sources over a multiple-access channel (MAC) with feedback were presented in [
25]. Lossy transmission of correlated Gaussian sources over a two-user Gaussian MAC with feedback was studied in [
26], in which sufficient conditions, as well as necessary conditions for the achievability of an MSE distortion pair were derived for the case in which the source and channel bandwidths match. The work [
26] also showed that for the symmetric setting, if the channel signal-to-noise ratio (SNR) is low enough, then uncoded transmission is optimal. While [
26] considered source-channel coding with a unit bandwidth ratio, [
1] studied the EDT for the transmission of correlated Gaussian sources over a two-user Gaussian MAC with and without feedback, when the bandwidth ratio is not restricted. Lastly, [
27] improved the lower bound derived in [
1] for the two-user Gaussian MAC without feedback and extended the results to more than two users.
While EDT analysis has gained some attention in recent years, the EDT of broadcast channels was considered only for GBCs without feedback. In particular, the work [
15] studied the transmission of Gaussian sources over a GBC and characterized the energy-distortion exponents, namely, the exponential rate of decay of the square-error distortion as the available energy-to-noise ratio increases without bound. For GBCFs, the existing literature mainly focused on channel coding aspects, considering independent and uniformly distributed messages. A key work in this context is the work of Ozarow and Leung (OL) [
28], which obtained inner and outer bounds on the capacity region of the two-user GBCF, by extending the point-to-point transmission strategy of Schalkwijk–Kailath (SK) [
29]. The work [
30] extended the OL scheme for two-user GBCFs by using estimators with memory (at the receivers) instead of the memoryless estimators used in the original OL scheme of [
28]. In contrast to the point-to-point case [
29], for GBCFs, both the scheme of [
28] and the scheme of [
30] are generally suboptimal. While the analysis and construction of the OL scheme [
28] are carried out in an estimation theoretic framework, the works [
31,
32] approached the problem of channel coding for the GBCF within a control theoretic framework. Specifically, [
32] proposed a transmission scheme based on linear quadratic Gaussian (LQG) control theory, that achieves rate pairs outside the achievable rate region of the OL code developed in [
28]. Recently, it was shown in [
33,
34] that, for the two-user GBCF when the noise components at the receivers are mutually independent with equal variances, the LQG scheme of [
32] achieves the maximal sum-rate among all possible linear-feedback schemes. Finally, it was shown in [
35] that the capacity of GBCFs with independent noises at the receivers and only a common message cannot be achieved using a linear feedback scheme. Instead, the work [
35] presented a capacity-achieving non-linear feedback scheme.
JSCC for the transmission of correlated Gaussian sources over GBCFs when the number of transmitted symbols is finite (referred to as the finite horizon regime) was previously considered in [
36], which studied the minimal number of channel uses required to achieve a target MSE distortion pair. Three linear encoding schemes based on uncoded transmission were considered: the first scheme was a JSCC scheme based on the coding scheme of [
28], to which we shall refer as the OL scheme; the second scheme was a JSCC scheme based on the scheme of [
32], to which we shall refer as the LQG scheme; and the third scheme was a JSCC scheme whose parameters are obtained using dynamic programming (DP) (in the present work we discuss only the former OL and LQG schemes since the scheme based on DP becomes analytically and computationally infeasible as the number of channel uses goes to infinity). We note that linear and uncoded transmission, as implemented in the OL and in the LQG schemes, has important advantages, including low computational complexity, short coding delays and small storage requirements, which make this type of coding very desirable. We further note that although the LQG channel coding scheme of [
32] for the two-user GBCF (with two messages) achieves the largest rate region out of all known channel coding schemes, in [
36], it was shown that when the time horizon is finite, JSCC based on the OL scheme can achieve MSE distortion pairs lower than the JSCC based on the LQG scheme. In the present work, we analyze lossy source coding over GBCFs using SSCC and JSCC schemes based on a different performance metric: the EDT.
We note here that, as discussed above, noiseless feedback has been studied extensively in wireless Gaussian networks. An immediate benefit of this analysis is that the performance obtained for noiseless feedback serves as an upper bound on the performance for channels with noisy feedback. The analysis of noiseless feedback scenarios also leads to guidelines and motivation, which then can be applied to channels with noisy feedback. Indeed, the works [
37,
38], which studied channel coding for point-to-point Gaussian channels with noisy feedback and for GBCs with noisy feedback, respectively, considered transmission schemes, which are based on the SK [
29] and on the OL schemes [
28], respectively, originally developed for noiseless feedback scenarios. In [
37,
38], the noise in the feedback links was handled by applying modulo-lattice precoding in both the direct and feedback links. It is shown in [
37,
38] that, while having noise in the feedback links results in a performance degradation compared to the case of noiseless feedback [
37] (Section V.D), many of the benefits of noiseless feedback can be carried over to the more practical setup of noisy feedback, thereby further motivating the current work. It follows that the analysis of noiseless feedback models provides practically relevant insights while facilitating simpler analysis.
Main contributions: In this work, the EDT for GBCFs is studied for the first time. We derive lower and upper bounds on the minimum energy per source pair required to achieve a target MSE distortion at each receiver, for the problem of transmitting a pair of Gaussian sources over a two-user GBCF, without constraining the number of channel uses per source sample. The new lower bound is based on cut-set arguments, while the upper bounds are obtained using three transmission schemes: two SSCC schemes and an uncoded JSCC scheme. The first SSCC scheme jointly compresses the two source sequences into a single bit stream, and transmits this stream to both receivers as a common message. The second SSCC scheme separately encodes each source sequence into two distinct bit streams, and broadcasts them via the LQG channel code of [
32]. It is shown that in terms of the minimum energy-per-bit, the LQG code provides no gain compared to orthogonal transmission, from which we conclude that the first SSCC scheme, that jointly compresses the sequences into a single stream, is more energy efficient. As both SSCC schemes apply coding over multiple samples of the source pairs, they require high computational complexity, long delays and large storage space. We then consider the uncoded JSCC OL scheme presented in [
36]. For this scheme, we first consider the case of fixed SNR and derive an upper bound on the number of channel uses required to achieve a target distortion pair. When the SNR approaches zero, the required number of channel uses grows, and the derived bound becomes tight. At the limiting scenario of
, this provides a simple upper bound on the EDT. While our primary focus in this work is on the analysis of the three schemes mentioned above, such an analysis is a first step towards identifying schemes that would achieve improved EDT performance in GBCFs.
Numerical results indicate that the SSCC scheme based on joint compression achieves better EDT compared to the JSCC OL scheme; yet, the gap is quite small. Moreover, in delay-sensitive applications, there is a constraint on the maximal allowed latency in transmitting each source sample to the destination. In such scenarios, coding over large blocks of independent and identically distributed (i.i.d.) pairs of source samples is not possible, and instantaneous transmission of each observed pair of source samples via the JSCC-OL scheme may be preferable in order to satisfy the latency requirement, while maintaining high energy efficiency.
The rest of this paper is organized as follows: The problem formulation is detailed in
Section 2. The lower bound on the minimum energy per source sample is derived in
Section 3. Upper bounds on the minimum energy per source sample are derived in
Section 4 and
Section 5. Numerical results are detailed in
Section 6, and concluding remarks are provided in
Section 7.
5. Upper Bound on E(D) via the OL Scheme
Next, we derive a third upper bound on
by applying uncoded JSCC transmission based on the OL scheme [
36] (
Section 3). This scheme sequentially transmits the source pairs
,
, without source coding. Thus, the delay introduced by the OL scheme is significantly lower than the delay introduced by the schemes discussed in
Section 4. We note that the OL scheme is designed for a fixed
, and from condition (
3) we obtain that
. An upper bound on
can now be obtained by first calculating the minimal number of channel uses required by the OL scheme to achieve the target distortion
D, which we denote by
, and then determining the required energy via
.
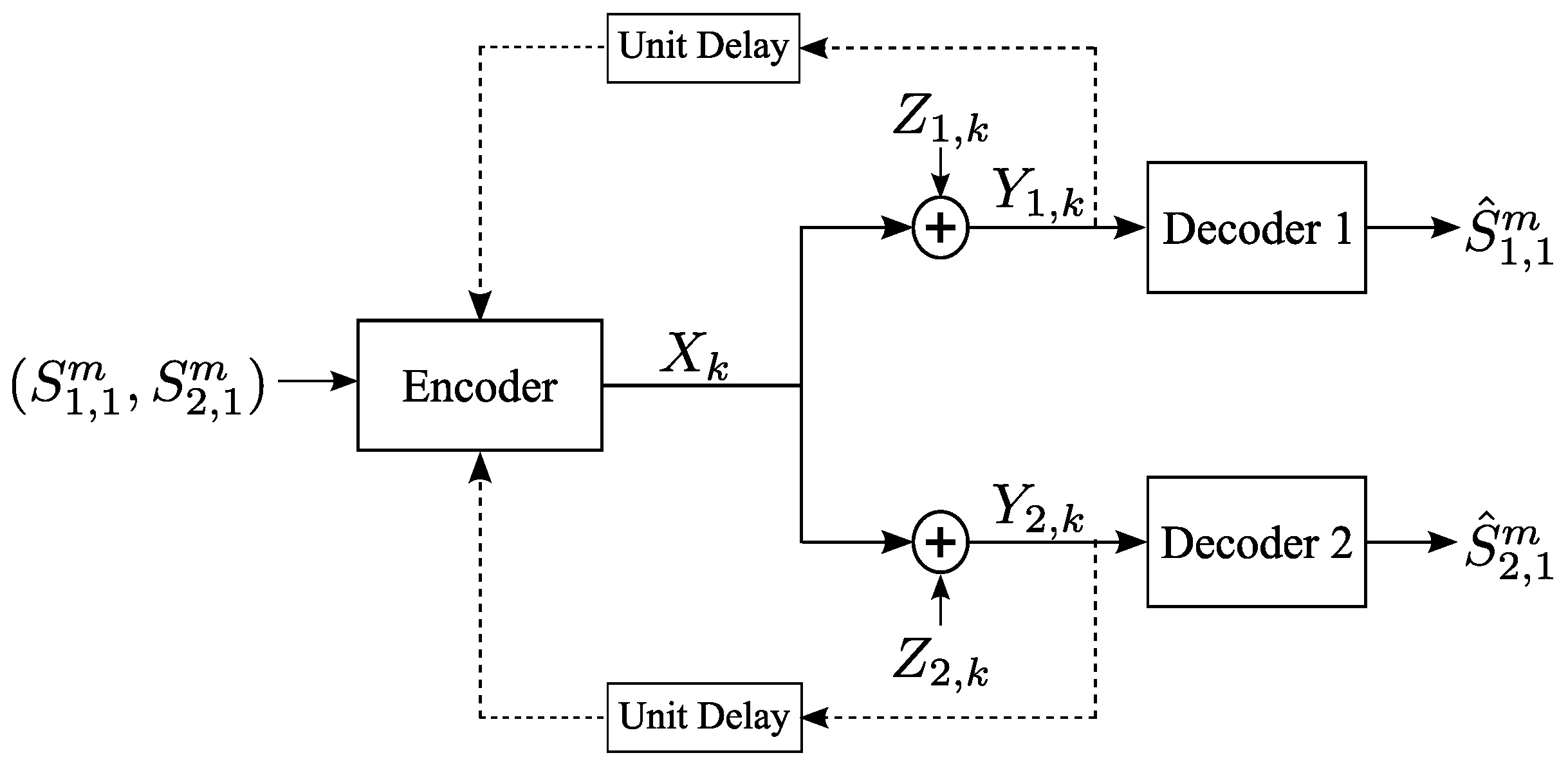
5.1. JSCC Based on the OL Scheme
In the OL scheme, each receiver recursively estimates its intended source samples. At each time index, the transmitter uses the feedback to compute the estimation errors at the receivers at the previous time index, and transmits a linear combination of these errors. The scheme is terminated after channel uses, when the target MSE D is achieved at each receiver.
Setup and Initialization: Let be the estimate of at Rx after receiving the channel output , be the estimation error after k transmissions, and define . It follows that . Next, define to be the MSE at Rx after k transmissions, to be the correlation between the estimation errors after k transmissions, and . For initialization, set and ; thus, . Note that for this setup and initializations, we have .
Encoding: At the
channel use the transmitter sends
, and the corresponding channel outputs are given by (
1).
Decoding: Each receiver computes
, based only on
via
, which can be explicitly computed as in [
28] (p. 669). Then, similarly to [
45] (Equation (7)), the estimate of the source
is given by
. Let
and
. The instantaneous MSE
is given by the recursive expression [
28] (Equation (
5)):
where the recursive expression for
is given by [
28] (Equation (7)):
Remark 7 (Initialization of the OL scheme).
Note that in the above OL scheme we do not apply the initialization procedure described in [28] (p. 669), as it optimizes the achievable rate rather than the distortion. Instead, we set and , thus, taking advantage of the correlation between the sources. Moreover, in Appendix C, it is explicitly shown that for the OL scheme, in the low SNR regime, the impact of the correlation between the sources on the distortion at the receivers lasts over a large number of channel transmissions. It thus follows that the proposed initialization clearly exploits the correlation between the sources.. We further note that [36] (Section III.B) considered several initialization methods for the OL scheme and showed that setting and outperforms the other studied initialization approaches. Let
denote the minimal energy per source pair required to achieve MSE
D at each receiver using the OL scheme. Since in the OL scheme
, we have
. From (13) one observes that the MSE value at time instant
k depends on
and the MSE at time
. Due to the non-linear recursive expression for
in (14), it is very complicated to obtain an explicit analytical characterization for
. For any fixed
P, we can upper bound
, and therefore
, via upper bounding
. In [
36] (Theorem 1) we showed that
, which leads to the upper bound:
. However, when
, the upper bound
is not tight This can be seen by considering a numerical example: Let
, and consider two possible values for
P:
and
. Via numerical simulations one can find that
, while the upper bound is 46,058. For
we have
, while the upper bound is 4,605,176. Thus, the gap between
and the above bound increases as
P decreases. For this reason, in the next subsection we derive a tighter upper bound on
whose ratio to
approaches 1 as
. This bound is then used to derive a tighter upper bound on
.
5.2. A New Upper Bound on
Following ideas from [
1] (Theorem 7), we assume a fixed
and approximate the recursive relationships for
and
given in (13) and (14) for small values of
. We note that while [
1] (Theorem 7) obtained only asymptotic expressions for
and
for
, in the following we derive tight bounds for these quantities and obtain an upper bound on
which is valid for small values of
. Then, letting
, the derived upper bound on
yields an upper bound on
, and therefore on
.
First, define:
and
. We further define the positive quantities
and
:
and finally, we define the quantities:
For small values of , the following theorem provides a tight upper bound on :
Theorem 4. Let P satisfy the conditions and . The OL scheme achieves MSE D at each receiver within channel uses, where, is given by: Proof outline. Let
(otherwise replace
with
). From [
28] (p. 669) it follows that
monotonically decreases with
k until it crosses zero. Let
be the largest time index
k for which
. In the proof of Theorem 4 we show that, for sufficiently small
,
. Hence,
decreases until time
and then it has a bounded magnitude (larger than zero). This implies that the behavior of
is different in the regions
and
. Let
be the MSE after
channel uses. We first derive upper and lower bounds on
, denoted by
and
, respectively. Consequently, we arrive at the two cases in Theorem 4: (17a) corresponds to the case of
, while (17b) corresponds to the case
. The detailed proof is provided in
Appendix C. ☐
Remark 8 (Bandwidth used by the OL scheme).
Note that as , increases to infinity. Since, as , , it follows that as , . Assuming the source samples are generated at a fixed rate, this implies that the bandwidth used by the OL scheme increases to infinity as .
Remark 9 (Theorem 4 holds for non-asymptotic values of
P).
Note that the conditions on P in Theorem 4 can be written as with depending explicitly on and . Plugging in (15) into the condition , we obtain the condition: . We note that, in this formulation the coefficients of , are all positive. Therefore, the left-hand-side (LHS) is monotonically increasing with P, and since is constant, the condition is satisfied if , for some threshold . Following similar arguments, the same conclusion holds for with some threshold instead of . Thus, by setting we obtain that the conditions in Theorem 4 restrict the range of power constraint values P for which the theorem holds for some .
5.3. An Upper Bound on
Next, we let , and use derived in Theorem 4 to obtain an upper bound on , and therefore on . This upper bound is stated in the following theorem.
Theorem 5. Let . Then, , where Proof. We evaluate
for
. Note that
, which implies that
. To see why this holds, consider, for example,
:
Since , and are constants, and since , we have . Now, since is constant we have . Taking the product of these two asymptotics we conclude that .
Now, for
we bound the minimum
as follows: First, for
defined in (16g), we multiply both sides of (17a) by
P. As
, then, as
, we obtain:
where (a) follows from (16f) by noting that
, and therefore, when
,
. This implies that as
we have
. Finally, note that for
we have
.
Next, for
we bound the minimum
by first noting that since
and
, then
. Now, for
defined in (16h), multiplying both sides of (17b) by
P, we obtain:
where (a) follows from the fact that
, see (16a). This concludes the proof. ☐
Remark 10 (Performance for extreme correlation values).
Similarly to Remark 5, as , the gap between and is not bounded, which is in contrast to the situation for the OL-based JSCC for the Gaussian MAC with feedback, cf. [1] (Remark 6). When we obtain that , for all , which follows as the sources are independent. When and then , in this case we also have and . Remark 11 (Comparison of the OL scheme and the separation-based schemes).
From (10)
and (18)
, it follows that if then is given by:Note that is independent of D in this range. Similarly, from (11)
and (18)
it follows that if then is independent of D and is given by:Note that in both cases the gap decreases as decreases, which follows as the scenario approaches the transmission of independent sources. The gap also increases as decreases. Remark 12 (Uncoded JSCC via the LQG scheme).
In this work, we do not include an analysis of the EDT of JSCC using the LQG scheme, , because JSCC-LQG does not lend itself to a concise analytical treatment, and, moreover, our numerical study demonstrated that, in terms of EDT, JSCC-LQG is generally inferior to JSCC-OL. To elaborate on these aspects, we first recall that the LQG scheme of [32] was already applied to the transmission of correlated Gaussian sources over GBCFs in [36] (Section IV). It follows from the derivations in [36] that is expressed as the solution of an optimization problem which does not have an explicit analytic solution. It is also shown in [36] that, for a finite duration of transmission and low transmission power, when the covariance matrix of the sources is different from the covariance matrix of the steady-state of the LQG scheme, then the JSCC-OL scheme outperforms the JSCC-LQG scheme, which stands in contrast to the results of [33] for the channel coding problem. This surprising conclusion carries over to the EDT as well. Indeed, using the results of [36] we carried out an extensive numerical study of JSCC-LQG, the outcome of which was that the JSCC-LQG scheme of [36] (Section IV) achieves roughly the same minimum energy as the SSCC- scheme. Since in Section 6 we show that the JSCC-OL scheme outperforms the SSCC- scheme in terms of the EDT, we decided to exclude the JSCC-LQG scheme from the numerical comparisons reported in Section 6. 6. Numerical Results
In the following, we numerically compare
and
. We set
and consider several values of
and
.
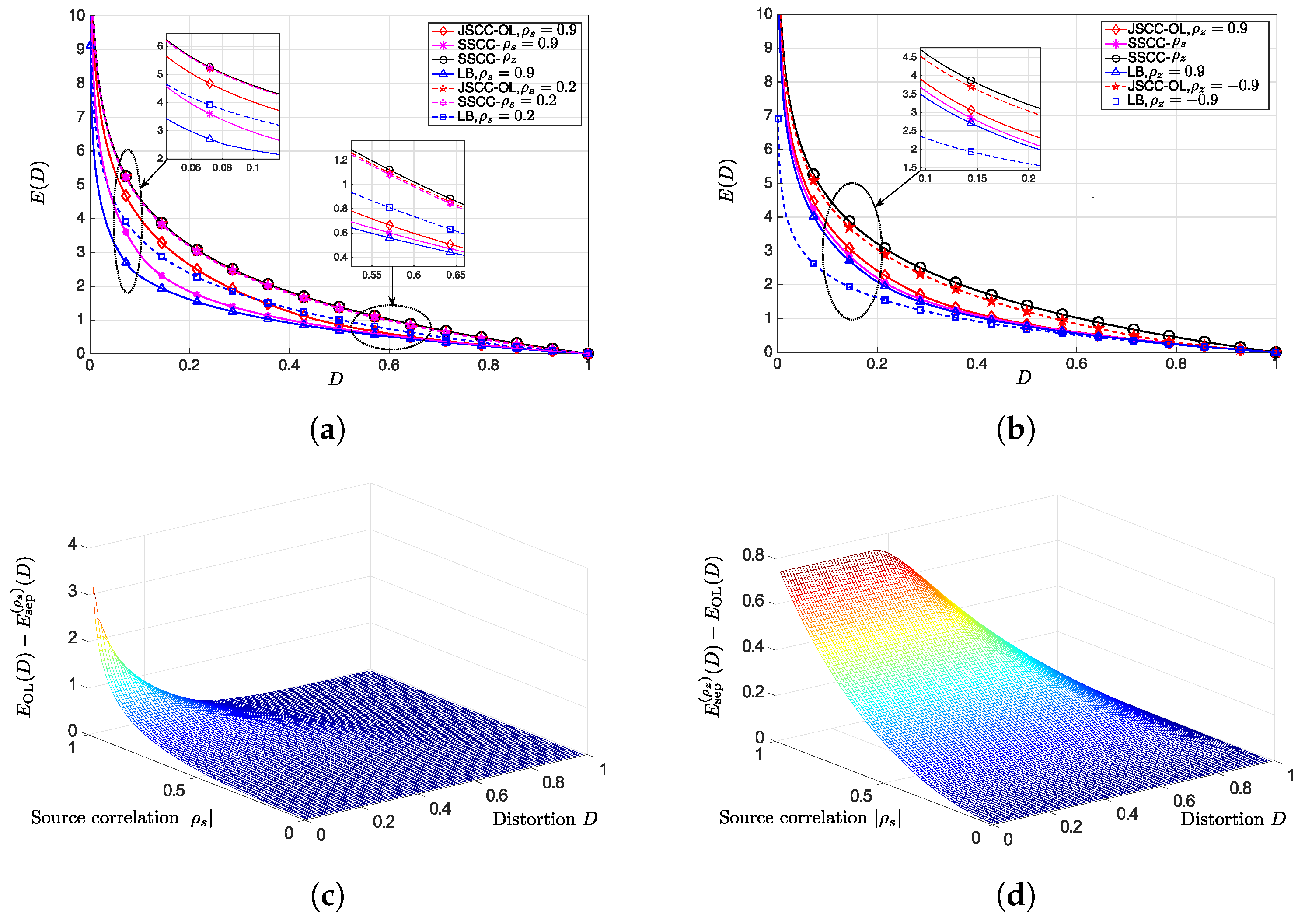
Figure 2a depicts
and
for
, and for two values of
:
and
. As
is not a function of
, it is plotted only once. It can be observed that when
, then
and
are almost the same. This follows because when the correlation between the sources is low, the gain from utilizing this correlation is also low. Furthermore, when
the gap between the lower bound and the upper bounds is evident. On the other hand, when
, both SSCC-
and OL significantly improve upon SSCC-
. This follows as SSCC-
does not take advantage of the correlation among the sources. It can further be observed that when the distortion is low, there is a small gap between OL and SSCC-
, while when the distortion is high, OL and SSCC-
require roughly the same amount of energy per source-pair sample. This is also supported by
Figure 2c. We conclude that as the SSCC-
scheme encodes over long sequences of source samples, it better exploits the correlation among the sources compared to the OL scheme.
Figure 2b depicts
and
vs.
D, for
, and for
. As
and
are not functions of
, we plot them only once. It can be observed that when
,
and
are very close to each other, as was analytically concluded in Remark 10. On the other hand, for
the gap between the bounds is large.
Note that while analytically comparing
,
and
for any
D is difficult, our numerical simulations suggest the relationship
, for all values of
. For example,
Figure 2c depicts the difference
for
, and for all values of
D and
. It can be observed that for low values of
, or for high values of
D,
. On the other hand, when the correlation among the sources is high and the distortion is low, then the SSCC-
scheme improves upon the OL scheme. When
we can use (19) to analytically compute the gap between the energy requirements of the two schemes. For instance, at
and
the gap is approximately 3.173.
Figure 2d depicts the difference
for
. It can be observed that larger
results in a larger gap. Again we can use (20) to analytically compute the gap between the energy requirements of the two schemes for a certain range of distortion values: At
and
, the gap is approximately 0.744. Finally, as stated in Remark 12, the LQG scheme achieves approximately the same minimum energy as the SSCC-
scheme, hence, OL is expected to outperform LQG. This is in accordance with [
36] (Section VI), which shows that for low values of
P, OL outperforms LQG, but, is in contrast to the channel coding problem in which the LQG scheme of [
32] is known to achieve higher rates compared to the OL scheme of [
28].
7. Conclusions and Future Work
In this work, we studied the EDT for sending correlated Gaussian sources over GBCFs, without constraining the source-channel bandwidth ratio. In particular, we first derived a lower bound on the minimum energy per source pair sample using information theoretic tools and then presented upper bounds on the minimum energy per source pair sample by analyzing three transmission schemes. The first scheme, SSCC-
, jointly encodes the source sequences into a single bit stream, while the second scheme, SSCC-
, separately encodes each of the sequences, thus, it does not exploit the correlation among the sources. We further showed that the LQG channel coding scheme of [
32] achieves the same minimum energy-per-bit as orthogonal transmission, and therefore, in terms of the minimum energy-per-bit, it does not take advantage of the correlation between the noises at the receivers. We also concluded that SSCC-
outperforms SSCC-
.
The third scheme analyzed is the OL scheme for which we first derived an upper bound on the number of channel uses required to achieve a target distortion pair, which, in the limit , leads to an upper bound on the minimum energy per source pair sample. Numerical results indicate that SSCC- outperforms the OL scheme, as well. On the other hand, the gap between the energy requirements of the two schemes is rather small. We note that the SSCC- scheme implements coding over blocks of samples of source pairs, which introduces high computational complexity, large delays and requires a large amount of storage space. On the other hand, the OL scheme applies linear and uncoded transmission to each source pair sample separately, which requires low computational complexity, short delays and limited storage space. Our results demonstrate that the OL scheme provides an attractive alternative for energy efficient transmission over GBCFs.
Finally, we note that for the Gaussian MAC with feedback, OL-based JSCC is very close to the lower bound, cf. [
1] (Figure 4), while, as indicated in
Section 6, for the GBCF, the gap between the OL-JSCC and the lower bound is larger. This difference is also apparent in the channel coding problem for GBCFs, namely between the achievable rate region of the OL scheme and the tightest outer bound (note that while the OL strategy achieves the capacity of the Gaussian MAC with feedback [
32] (Section V.A), for the GBCF the OL strategy is sub-optimal [
28]). Therefore, it is interesting to see if the duality results between the Gaussian MAC with feedback and the GBCF, presented in [
33,
34] for the channel coding problem, can be extended to JSCC and if the approach of [
33,
34] facilitates a tractable EDT analysis. We consider this as a direction for future work.