The Importance of the Security Culture in SMEs as Regards the Correct Management of the Security of Their Assets †
Abstract
:1. Introduction
- Technical Orientation: This deals with the technical management of information security through the use of computer systems, such as authentication and access control services.
- Management Orientation: This began when the top management became involved in information security with the evolution of the Internet and electronic business activities, and includes tasks regarding the preparation of information security, policies, procedures and methods, along with the designation of a person who is responsible for security.
- Institutional tendency: this is parallel to the first and second orientations and includes the creation of a corporative security culture covering the standardization, certification, measurement and concern about the human aspect in information security.
2. State of the Art
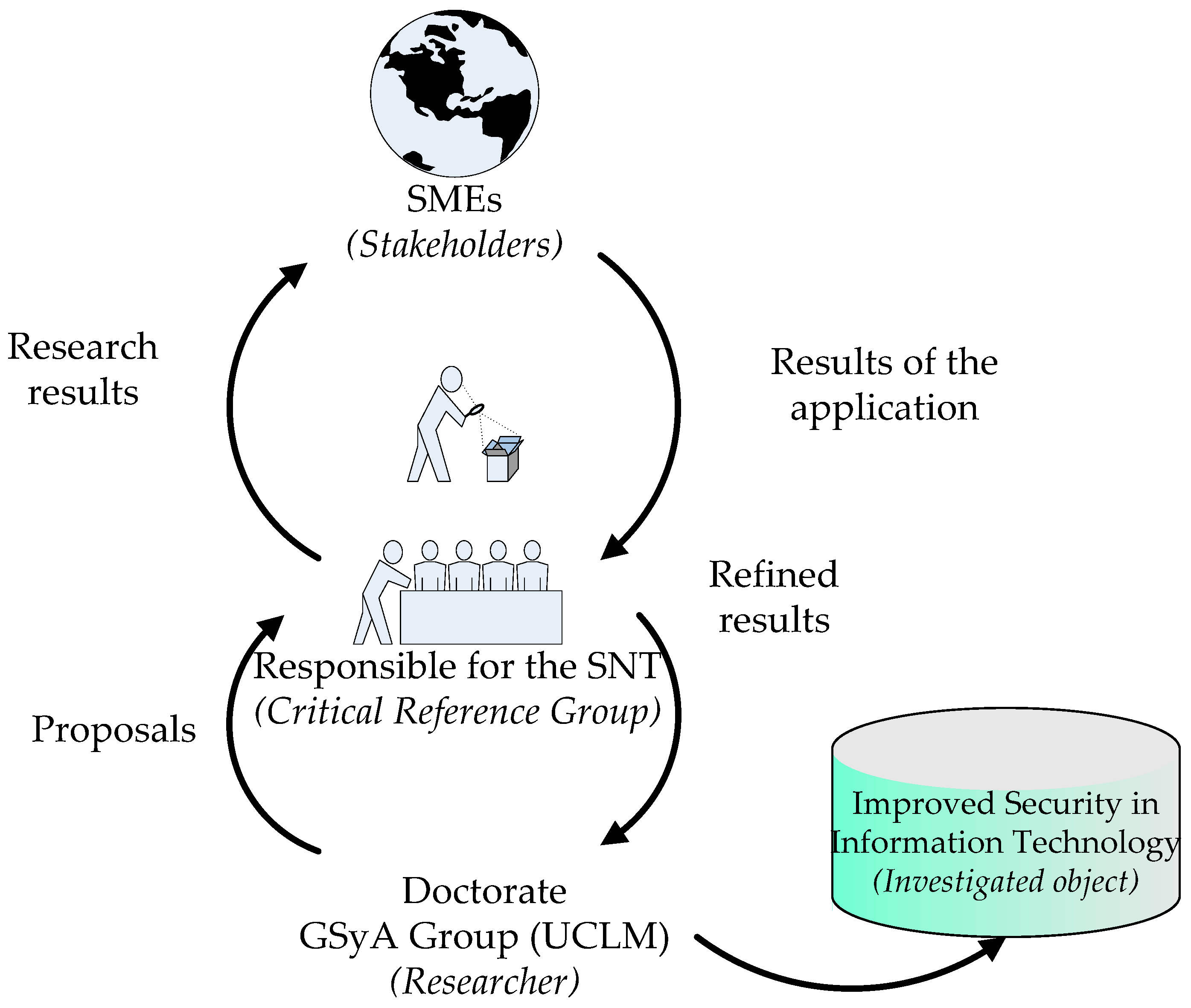
2.1. The Action Research Method
- The researcher, which is in this case the GSyA Research Group, made up of professors at the School of Computer Sciences at the University of Castilla-La Mancha in Ciudad Real, Spain.
- The object being researched, i.e., the problem to be resolved, which is in this case improving the security management of information technologies.
- The critical reference group (CRG): those for whom the research is being carried out and who also participate in the research. This consists of the Sicaman Nuevas Tecnologías S.L. company, its customers and the participants in the research projects.
- The fourth participant—the beneficiary, which consists of those organizations that may benefit from the results of the work, i.e. all those small and medium-sized companies that might wish to apply advanced information security management methods to their information systems in order to improve the security of their information technology products and processes in a controlled and methodical manner. The results obtained after carting out this research will improve the efficiency of the installation and maintenance processes of information security management systems. The principal beneficiaries will therefore be all those companies that are linked to the critical reference group.
- Planning: Once the problem related to incorporation of security management systems into SMEs had been identified, we planned the development of a methodology that would allow the creation of an ISMS with the minimum possible number of resources, which would be adapted to the size and maturity of the company.
- Action: having defined the principal elements involved in the ISMS-creation process, we then went on to create a model and to apply it in determined case studies. The elements that would be used to construct the final ISMS were also applied in the case study.
- Observation: Once the elements had been applied and the ISMS had been created, the results obtained were evaluated. This allowed us to improve the original proposals and to eventually define a methodology that would systemize the creation and evolution of an ISMS for a company, along with a model that would permit its validation. The entire method is supported by a prototype that allows the simple generation of ISMSs and the work to be carried out with them in order to analyze their evolution over time.
- Reflexion: the cyclical nature of the action research method was borne in mind, and results that were the product of successive iterations were therefore obtained. The research team has shared and contrasted these results in the national and international forums of scientific communities related to the topics being dealt with in this research.
- A suitable method with which to manage security and its level of maturity in SMEs’ information systems.
- A security maturity and management model based on the methodology developed and denominated as the base schema, which is appropriate for the resources of SMEs. The result was accepted by the critical reference group.
- Benefits for the participants: scientific benefits for the researcher and practical benefits for the beneficiaries.
- The knowledge obtained can be applied immediately.
2.2. Researches about the Security Culture
- Siponen [38] states that “the consciousness of information security” is a state in which an organization’s users are conscious of their mission as regards security, and this is divided into two categories: (i) the application framework (standardization, certification and institutionalization activities), and (ii) content (the human aspect).
- Dhillon [6] has a broad view of the term ”security culture”, and defines it as the behavior of an organization’s users that contributes towards the protection of data, information and knowledge.
- Eloff [31] defines the information security culture as a set of information security characteristics, such as integrity and the availability of information.
- For Chia [41], the information security culture is a fundamental aspect, and this author defines a set of dimensions that are important as regards measuring the efficiency of the information security culture: (i) a belief in the importance of information security; (ii) a long and short-term balance, goals, policies, procedures and continual improvement processes; (iii) cooperation and collaboration; and (iv) attention to auditing objectives and their fulfillment. This list has, however, recently been criticized by Helokunnas [42], who places particular emphasis on the human aspects of information security.
- Straub [43] maintains that with information systems it is always assumed that a person belongs to a single culture, and this author therefore proposes using the theory of social identity as a basis for research into the information security culture. The idea behind the social identity culture is that each individual is influenced by a multitude of cultures. According to [43], upon applying the social identity culture, users will be influenced by ethical aspects, each country’s legislation and the organization of security. This culture has an effect on the way in which the individual interprets the significance and importance of information security.
- Kuusisto [44] proposes a system in which the security culture is created on the basis of the interaction between the reference framework and its components.
- Finally, Detert [45] considers the security culture to be a key aspect of ISMSs, and has developed a general framework for information security which is based on eight dimensions [37] applied these eight dimension to the areas of information security and identified the principal factors of information security in each dimension.
2.2.1. Proposal of Dojkovski
- SMEs view the information system as a system that supports the company’s production departments and not as something that is vital for their business. This makes them reactive rather than proactive to security failures.
- For SMEs, cost is fundamental, and they view security as an unjustified expense.
- The managers are not concerned about security and neither, therefore, are the other employees.
- Users find it very difficult to fulfill this framework. What is more, it is very difficult to change the bad habits acquired, and none of the users wish to be responsible for the information security system assets.
- Initiatives should be appropriately managed, and the policies and procedures should be presented to users when they sign their contracts. This may be more difficult for SMEs, since they lack formal organizational structures. It is also important to consider the fulfillment of security within the evaluation of the employees’ work.
- The lack of appropriate information as regards security. Those surveyed considered e-learning to be a valid work tool with which to improve the level of the information security culture, as was the possibility of being able to share experiences with other SMEs. The problem is, however, that it is not normally possible for the workers at SMEs to go on courses for reasons of time and money, and many workers do not take these courses if there is no motivation for them to do so.
- E-Learning (cooperation, collaboration and the exchange of knowledge): SMEs could undertake electronic learning (e-learning) [61], and could also cooperate and collaborate electronically in information system security communities and forums [42] with the objective of improving the information system users’ security culture.
- Management: Awareness-raising programmes (supported by the management, threats of disciplinary measures, clauses in employment contracts, etc.), training, education or the value of leadership [62] are valuable initiatives for the development of the information security culture [12,54]. It is probable that different levels of awareness raising, training and educational needs are generated for the individual employees in SMEs.
- Security culture: Procedures with which to respond to new events (such as security violations) will help to underline the importance of information security for workers [27]. Incentives may also be useful as regards modifying employees’ behavior. However, Rosanas and Velilla [14] warn that management controls should be based on ethical values.
- Behavior: The management of initiatives whose intention is to develop desirable behavioral features with regard to the personnel’s responsibility, integrity, trust and ethics [20]. Strong values are, however, necessary to support management initiatives [14]. Information security is strengthened when strong values are disseminated among collaborating entities and other interested parties [42]. The development of intrinsic motivation is important [38], and can be supported by promoting those personnel who appropriately fulfil the security regulations [45].
- National ethics and organizational culture: According to Helokunnas [42], the creation of security forums at a national level may favor the creation of an information security culture.
- Motivating company owners to allocate appropriate funding to information security.
- Convincing company owners to carry out a formal risk analysis.
- Ensuring that company owners develop information security policies and procedures and assign responsibilities.
- Developing a proactive attitude towards information security.
- Identifying and establishing a series of awareness-raising activities that can be adapted to SME environments.
2.2.2. Proposal of Sneza
- National ethics and organizational culture. A nation’s culture may affect the organization of information security. Social ethics may also have an important impact. Helokunnas [51] states the importance of social networks as regards sharing problems related to information security and creating a consciousness about the subject.
- Government initiatives: governments could play a fundamental role in the creation of an information security culture by approving special legislation and providing support (courses, subsidies, etc.).
- Suppliers: suppliers could ensure that SMEs are reliable in the form of the additional guarantee of the security of the products they sell them.
- Leadership and corporative government: The owners of SMEs should demonstrate that they support information security management. According to Dutta [62], the management’s support is highly valued by large companies, but this is not the case at SMEs.
- Organizational culture: An organization’s culture and environment have a direct influence on the fulfilment of security management.
- Management: Firstly, SMEs consider the results of risk analyses to be a key aspect as regards guaranteeing that policies and procedures are really necessary. Secondly, SMEs must be guided by the risk of losing assets, which they discover via the risk analysis. Martins identified this need in large organizations. Thirdly, it is necessary to allocate a budget to security management, whose resources should include the initiatives needed to establish a security management culture. Martins also suggested that the budget has a great influence on organizations. Fourthly, the procedures used to respond to information security incidents would help to underline the importance of information security for the employees, and this has also been generally suggested by the OCDE [27]. Fifthly, SMEs should receive some kind of reward for periodically evaluating their information security culture. In addition, finally, the employment contract should include sanctions or incentives with which to motivate employees. All management processes should be evaluated periodically.
- Individual and organizational learning: e-learning, training and education are potentially valuable initiatives for the development of the information security culture for both SMEs and large companies [38,54,61]. The exchange of knowledge, cooperation and collaboration are important for learning at the different levels of the organization when the objective is to develop the information security culture. The learning processes should be evaluated periodically.
- Reviews and evaluation: SMEs should periodically examine and evaluate the measures adopted in order to continuously improve.
- Behavior: A series of external and internal initiatives could be used in an attempt to develop behavior regarding responsibility, integrity, trust and ethics. According to Dhillon [20], in large organizations this transformation originates from internal management initiatives, whilst in the framework proposed [63] this responsibility is shared by internal and external agents. Siponen [38] states the importance of intrinsic motivation. One efficient measure for an organization is that of providing those users who comply with information security regulations with benefits [45].
- It is necessary to persuade SME owners to undertake a formal scenario based on risk analysis and the protection of information assets. Recent information security findings have shown a strong correlation between the formal risk evaluation process and spending on information security [23].
- Australian SME owners do not understand the strategic value of IT in their businesses. Other studies have demonstrated that this is not an isolated case, and a study by O’Halloran [66] therefore demonstrated that SMEs in the United Kingdom do not understand how security provides their businesses with added value.
- A previous requirement for the development of the information security culture in SMEs is the development and communication of policies, procedures and responsibilities. As many experts and studies have pointed out, the majority of SMEs in developed countries lack policies of this nature [23,50,65].
- Cooperation, collaboration, knowledge exchange and electronic learning were valuable activities for Australian SME employees. This finding coincides with that of the study carried out by ISBS [23].
2.3. Conclusions
- Group 1. Characteristics oriented towards the application of framework regulations.
- ○
- Standardization: The implementation of the process will be based on the regulations related to the management of information security systems.
- ○
- Certification: This process will permit users to obtain any type of temporary certification.
- ○
- Measurement: This system will make it possible to measure the company’s level of security culture.
- ○
- Cultures: This system not only takes into account the internal cultural aspects, but also local, sectorial and international legislation.
- Group 2. Characteristics focused on users’ human aspects.
- ○
- Progressive adaptation: The process will permit the users’ security culture to be adapted in a progressive manner.
- ○
- Theoretical Approach: The process will be based on an appropriate theoretical and regulative approach.
- ○
- Practical Approach: The process will be oriented towards a practical application as regards users.
- ○
- Critical Aspects: The human aspect will be considered critical in the preparation process.
- ○
- Psychological Factors: Disciplinary actions, clauses, rewards for points, etc. and their effects on the users’ psychology when using the process will be taken into consideration.
- Group 3. Other desirable aspects for the process.
- ○
- Oriented towards SMEs: It must have an orientation if it is to be valid for both big companies and SMEs.
- ○
- Low cost resources: It should be oriented towards low costs as regards the implementation and maintenance of the system
- ○
- Core of the ISMS: The security culture process is the main process in information security management. (ISMS)
- ○
- Dynamic Knowledge Base: This process is able to learn from the security incidents and change those weaknesses into strengths by incorporating the incidents into the knowledge base in order to reinforce the security culture of those aspects.
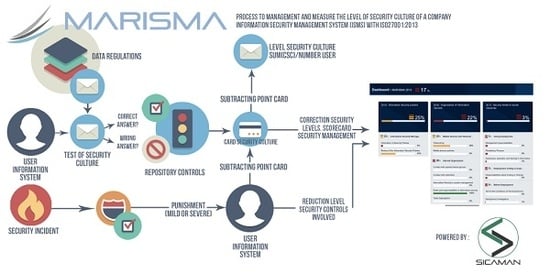
3. MARISMA Framework
- SMScG—Security Management Schema Generation: The principal objective of this sub-process is to construct the ‘schemas’, which are the structures needed to build ISMSs, and are created for a possible set of companies in the same category. These schemas are reusable and permit a reduction in both the time needed to create the ISMS and its maintenance costs so as to make them suitable for the dimension of an SME [68]. The use of schemas is of particular interest in the case of SMEs since their special characteristics signify that they tend to have simple information systems that are very similar to each other.
- SMSyG—Security Management System Generation: The main objective of this is the use of an already-existing schema to create an ISMS that will be suitable for a company.
- SMSyM—Security Management System Maintenance: The principal objective of this sub-process is to maintain and manage the security of the company’s information system, contributing information that is updated over time to the ISMS generated.
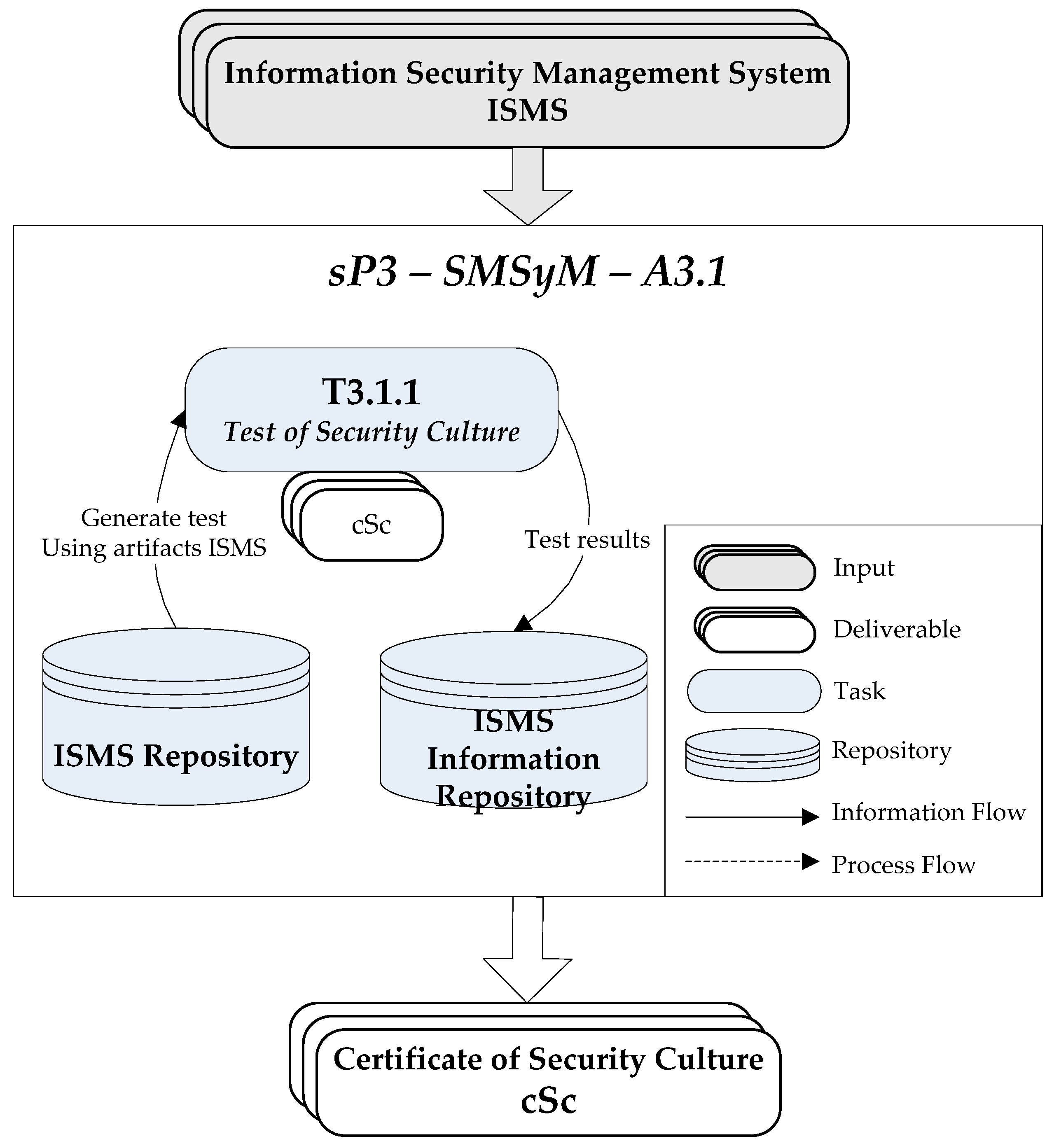
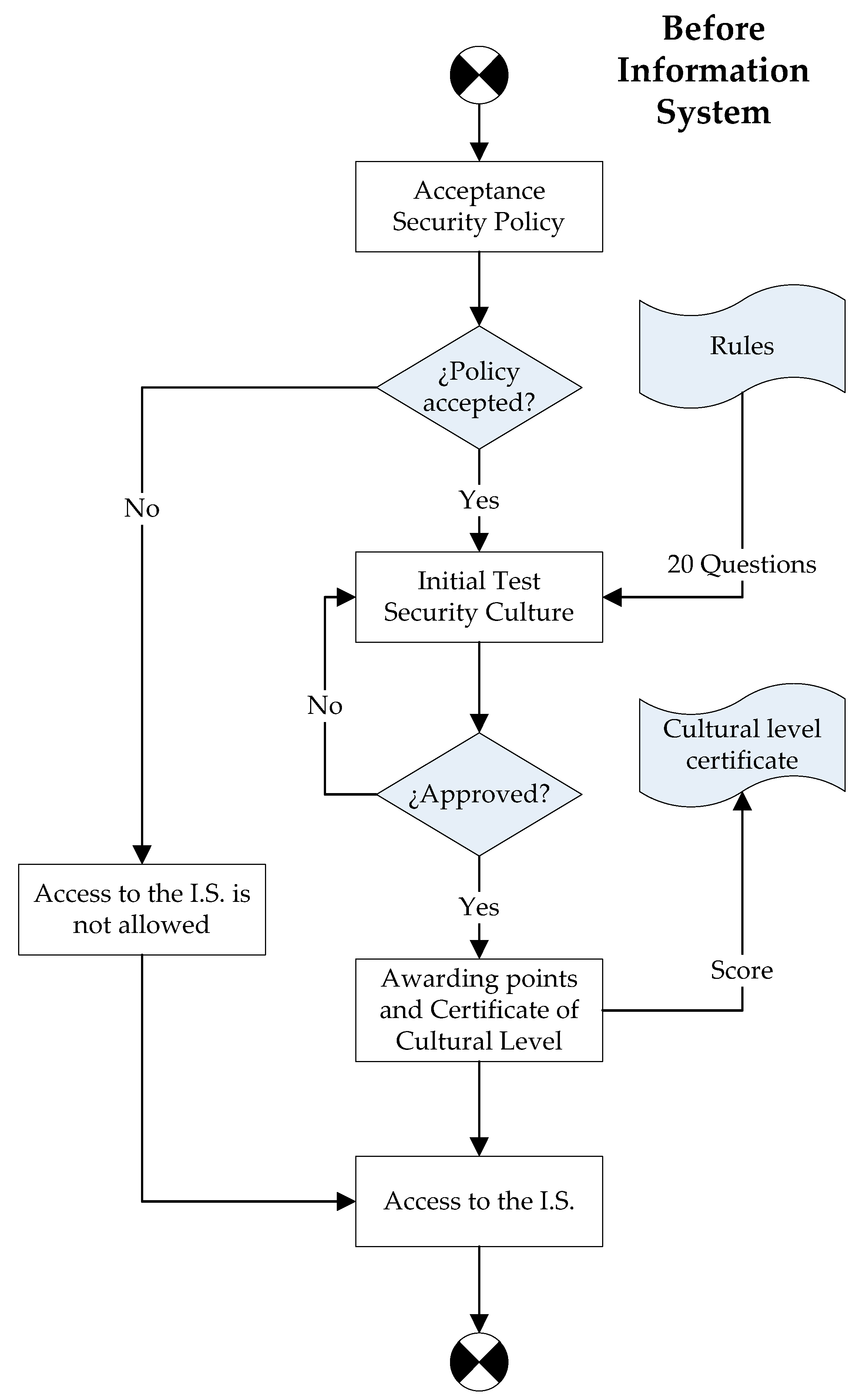
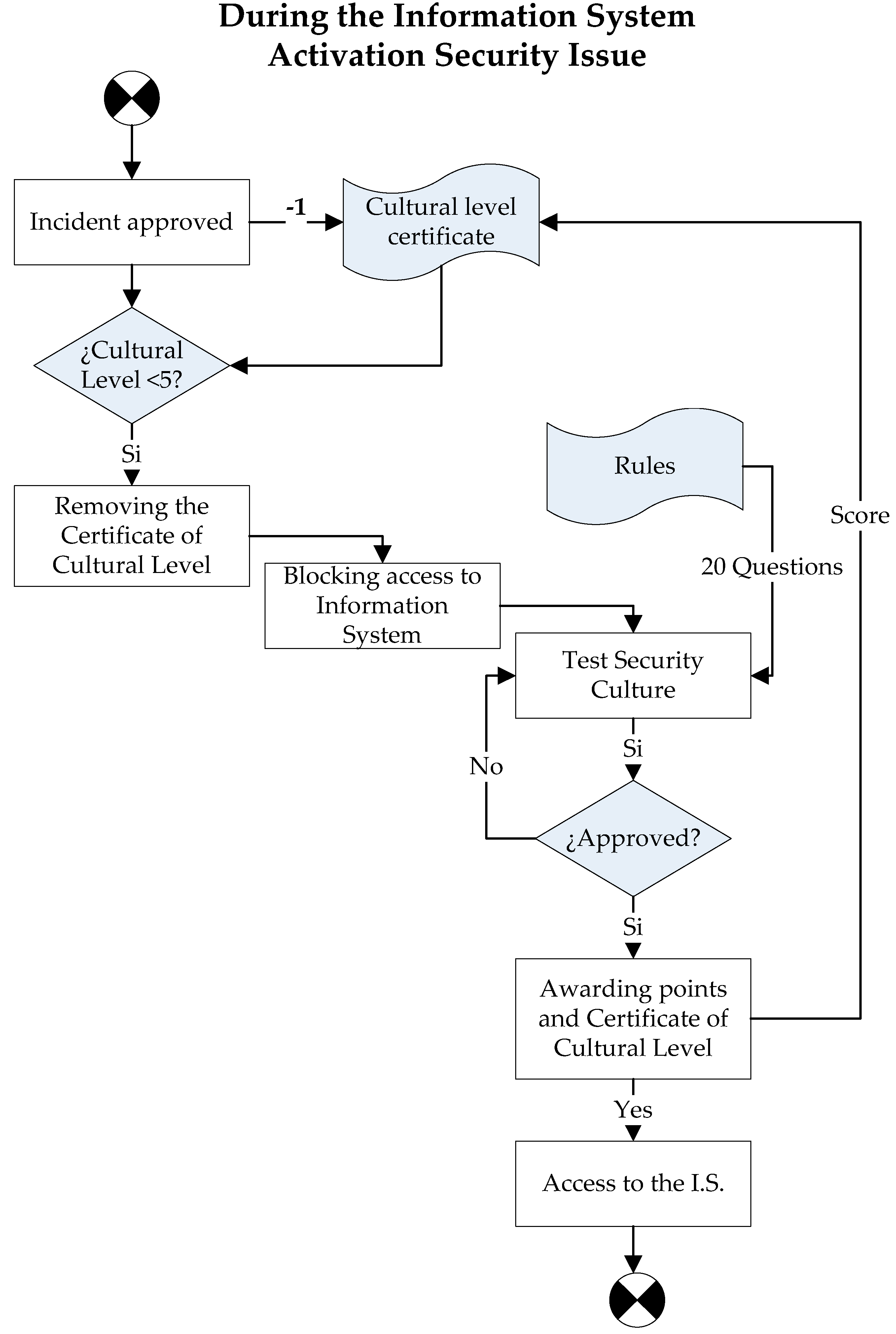
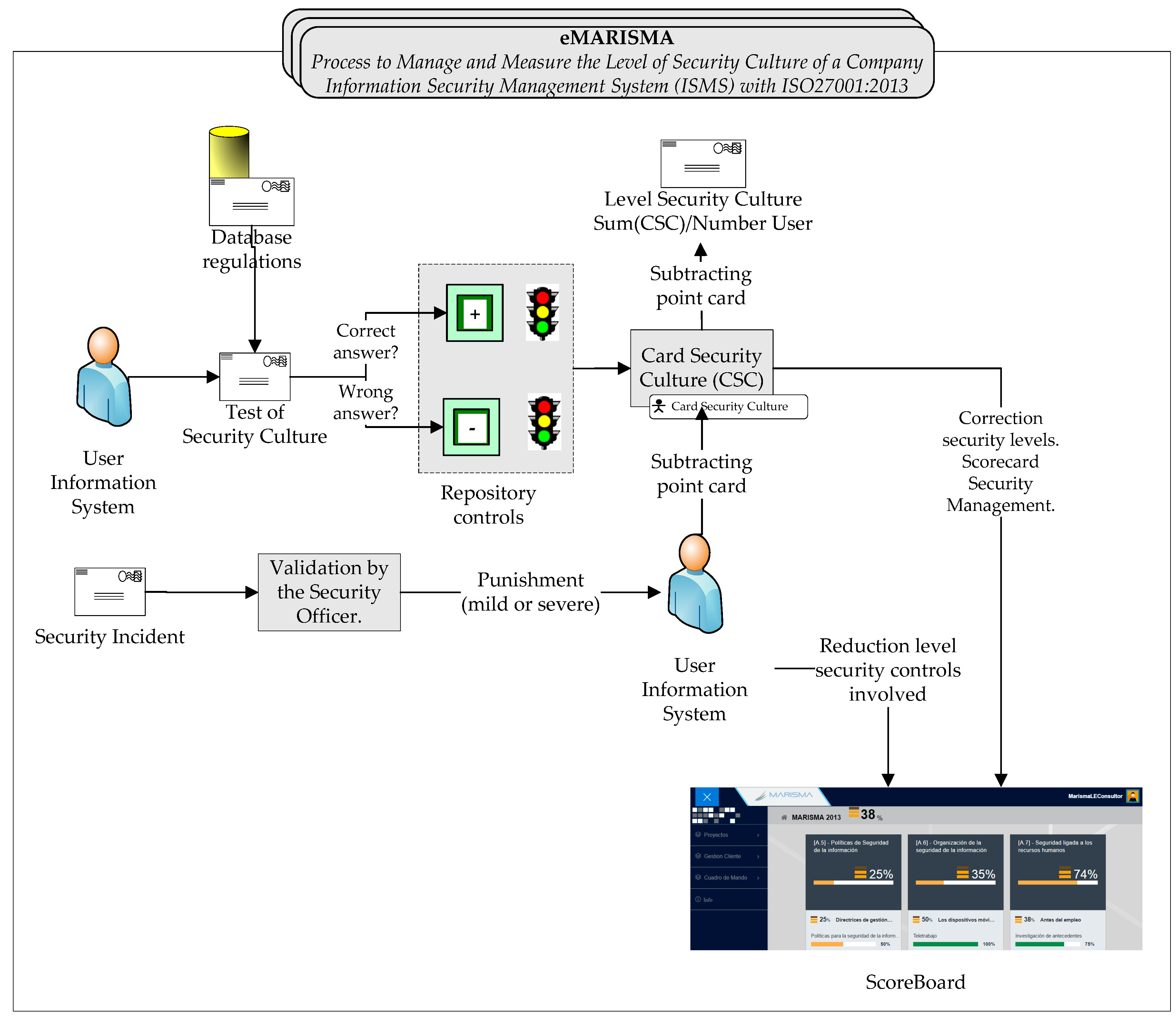
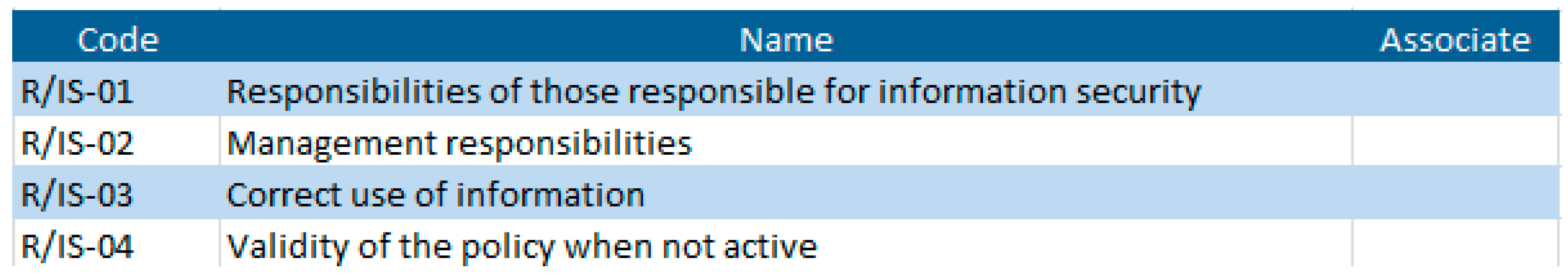
4. SME-SCCM: Security Culture Certificate Management
- Inputs: the inputs are the users’ responses to the questionnaire as regards the regulations generated by the system.
- Tasks: the sub-process will be formed of one single task—that of issuing the security certificates.
- Outputs: The output produced by this sub-process will consist of the security culture certificate, which will be issued only if the mark obtained in the questionnaire is five or above, otherwise the certificate will be denied. Those users who fail the test are advised to either study the ISMS security manual or attend a security management course in order to increase their knowledge of the material.
- Group 1. Characteristics oriented towards the application of the regulation framework.
- ○
- Normalization: The development process is based on the use of reusable patterns. The use cases were created with patterns regarding the ISO27001.
- ○
- Certification: The process developed permits the users to obtain a security points card, which enables them to access the system and provides an indication of the level they have.
- ○
- Measurement: The system makes it possible to measure the company’s level of security culture, at user, department and company levels.
- ○
- Culture: The process developed takes multicultural aspects into account, which merely have to be added to the corresponding pattern.
- Group 2. Characteristics oriented towards the users’ human aspect.
- ○
- Progressive adaptation: The process permits the users’ security culture to be adapted in a progressive manner because it lets them know their real level of security culture at all times. This is achieved through the use of the points card. It is possible for them to take the test again to obtain higher marks.
- ○
- Theoretical Approach: The process is based on the theoretical approach and appropriate regulations. In this case, the pattern used is based on the ISO27001 international standard.
- ○
- Practical Approach: The process is oriented towards being applied by users in a practical manner because it ensures that they are continuously conscious of their limits and can compare themselves with their colleagues.
- ○
- Critical Aspect: The human aspect has been considered critical when developing the process and is at its core.
- ○
- Psychological Factors: The points card works as a psychological measure that pressurises the users to improve and to be careful not to incur sanctions, since these are also seen by their superiors. Various kinds of disciplinary action had been taken before the implementation of the points card, none of which worked.
- Group 3. Other desirable aspects.
- ○
- Oriented towards SMEs: Its validity for SMEs was borne in mind, and it has principally been validated at this type of companies.
- ○
- Low cost resources: The implementation and maintenance costs are very low because of the simplicity of the process. More complex systems were tested but they did not work.
- ○
- Core of the ISMS: SME-SCCM has not been considered to be the core of the MARISMA methodology, although it is a very important process.
- ○
- Dynamic Knowledge Base: This process is able to learn from security incidents because the event module generates knowledge for the question base of the pattern selected. The tests are therefore generated in an intelligent manner, with priority being given to those questions that relate to greater vulnerabilities in the system.
5. Practical Application of MARISMA
- There was a progressive increase in the security culture of all ten companies of between 12% and 15%, between the first and last tests. No company’s level of security culture worsened.
- The level of security incidents at the companies was reduced by between 5% and 12% between the first and last tests. It is important to highlight that some companies took additional decisions that enabled these results to increase. The level of incidents did not increase at any if the companies.
6. Conclusions
- Awareness raising, responsibility, response, ethics: A system of courses based on simple test-type questions and a system of rewards and sanctions is used to progressively create consciousness of the security culture in information system users. Activity A3.1 is based on simple questionnaires.
- Democracy: The system should protect the company and its users’ jobs, as long as this does not suppose any impediment towards them carrying out their work efficiently. The principal objective of Activity A3.1 is to permit access only to those users who are conscious of the importance of security in the information system.
- Risk Evaluation: The system should be capable of continuously self-evaluating its risks and of providing measures to deal with them. The document obtained in Activity A3.1 (the security culture certificate) provides constancy of the level of knowledge that users have attained as regards regulations, and this measure is completed with the risk evaluation and the improvement plan in Activity A2.3 (Risk analysis).
- Design and realization of security: The methodology is intended to be integrated into the framework as another piece of it, and is oriented towards organizing the means used to work as regards security without being a burden for the workers. Activity A3.1 is totally integrated into daily work with the ISMS, and is simply one more activity.
- Security management: The methodology should allow security to be managed in a way that is comfortable such that the security culture with which it is associated can be introduced into the information system users naturally. The entire MARISMA methodology is focused on simplicity when working with it.
- Re-evaluation: The methodology should have metrics that permit the system to be able to periodically re-evaluate itself at a low cost, and to recommend suitable metrics. The MARISMA methodology has both general and specific characteristics that allow the security scoreboard to be kept updated at all times at a low cost, which makes it possible to know the level of fulfillment of the security controls at all times. One example of these metrics is each user’s security culture certificate, which defines a minimum security culture level for the system users.
- Simplicity: It is a practical method to apply and its users do not reject it. Some of the companies that participated in this research have included an automated process in their intranet, such that if a user does not have the security card or if it is lost, access to the company’s intranet will be blocked until the answer to the question is correct, and the certificate is once again awarded. The convenience of the method signifies that the users do not see it as an obstacle in their job, and they therefore understand its objective.
- Quantitative value: This method permits the company to attain a quantitative figure of the level of its security culture, which can be compared with different time periods. This is of great value for the companies because it lets them know whether the decisions they are making are appropriate.
- Low cost: The implementation of the process implies very low costs for the companies. They do not require a great investment from others. (e.g., Consultants). It does not consume resources, even as regards its maintenance.
- Learning: The constant capacity to improve the knowledge base on the basis of the security events that make it possible to reinforce the users’ knowledge of security in the weaker aspects of the company.
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Santos-Olmo, A.; Sánchez, L.E.; Ismael, C.; Camacho, S.; Daniel, M.; Fernández-Medina, E. Importancia de la Cultura de la Seguridad en las PYMES para la correcta Gestión de la Seguridad de sus Activos. In Proceedings of the VIII Congreso Iberoamericano de Seguridad Informática (CIBSI15), Quito, Ecuador, 10–12 November 2015; pp. 14–27. (In Spanish)
- Whitman, M.; Mattord, H. Principles of Information Security; Cengage Learning: Boston, MA, USA, 2012. [Google Scholar]
- Disterer, G. ISO/IEC 27000, 27001 and 27002 for information security management. J. Inf. Secur. 2013, 4, 92–100. [Google Scholar] [CrossRef]
- Beckers, K.; Faßbender, S.; Heisel, M.; Küster, J.C.; Schmidt, H. Supporting the development and documentation of ISO 27001 information security management systems through security requirements engineering approaches. In Engineering Secure Software and Systems; Barthe, G., Livshits, B., Scandariato, R., Eds.; Springer: Berlin, Germany; Heidelberg, Germany, 2012; pp. 14–21. [Google Scholar]
- Von Solms, R. Information Security Management: Processes and Metrics. Ph.D. Thesis, University of Johannesburg, Johannesburg, Republic of South Africa, June 1993. [Google Scholar]
- Dhillon, G. Managing Information System Security; Palgrave Macmillan: London, UK, July 1997. [Google Scholar]
- Candiwan, C. Analysis of ISO27001 implementation for enterprises and SMEs in indonesia. In Proceedings of the International Conference on Cyber-Crime Investigation and Cyber Security (ICCICS2014), Kuala Lumpur, Malaysia, 17–19 November 2014; pp. 50–58.
- Whitman, M.; Mattord, H. Management of information security; Cengage Learning: Boston, MA, USA, 2013. [Google Scholar]
- Johnson, M. Cybercrime: Threats and Solutions; Ark Group: London, UK, 2015. [Google Scholar]
- Furnell, S.M.; Gennatou, M.; Dowland, P.S. Promoting security awareness and training within small organisations. In Proceedings of the 1st Australian Information Security Management Workshop, Deakin University, Geelong, Australia, 7 November 2000.
- Schlienger, T.; Teufel, S. Information security culture—From analysis to change. In Proceedings of the 3rd Annual IS South Africa Conference, Johannesburg, South Africa, 9–11 July 2003.
- Lichtenstein, S.; Swatman, P.M.C. Effective management and policy in E-business security. In Proceedings of the Fourteenth Bled Electronic Commerce Conference, Bled, Slovenia, 25–26 June 2001.
- Cole, K.S.; Stevens-Adams, S.M.; Wenner, C.A. A Literature Review of Safety Culture; Sandia National Laboratories: Livermore, CA, USA, 2013. [Google Scholar]
- Rosanas, J.M.; Velilla, M. The Ethics of management control systems: Developing technical and moral values. Bus. Ethics 2005, 53, 87–96. [Google Scholar] [CrossRef]
- Schultz, E. The Human Factor in Security. Comput. Secur. 2005, 24, 425–426. [Google Scholar] [CrossRef]
- Bugdol, M.; Jedynak, P. Integrated Management Systems; Springer: Cham, Switzerland, 2015. [Google Scholar]
- Von Solms, B. Information Security—The Third Wave? Comput. Secur. 2000, 19, 615–620. [Google Scholar] [CrossRef]
- Bozic, G. The role of a stress model in the development of information security culture. In Proceedings of the MIPRO 35th International Convention, Opatija, Croatia, 21–25 May 2012.
- Magklaras, G.; Furnell, S. The insider misuse threat survey: Investigating IT misuse from legitimate users. In Proceedings of the 5th Australian Information Warfare & Security Conference, Perth, Western Australia, 25–26 November 2004; pp. 42–51.
- Dhillon, G.; Backhouse, J. Current directions in information systems security research: Toward socio-organizational perspectives. Inform. Syst. J. 2001, 11, 127–153. [Google Scholar] [CrossRef]
- Galletta, D.F.; Polak, P. An empirical investigation of antecedents of internet abuse in the workplace. In Proceedings of the AIS SIG-HCI Workshop, Seattle, DC, USA, 12–13 December 2003.
- CSI/FBI. Tenth Annual CSI/FBI Computer Crime and Security Survey; Computer Security Institute: College Park, MD, USA, 2005. [Google Scholar]
- ISBS. Information Security Breaches Survey 2006; Department of Trade and Industry: London, UK, 2006. [Google Scholar]
- AusCERT. Australian Computer Crime and Security Survey; AusCERT: Gold Coast, Australia, 2005. [Google Scholar]
- Ernst&Young. 2006 Global Information Security Survey; EYGM Limited: London, UK, 2006. [Google Scholar]
- DTI. The Empirical Economics of Standards; Department of Trade and Industry: London, UK; Available online: http://www.immagic.com/eLibrary/ARCHIVES/GENERAL/UK_DTI/T050602D.pdf (accessed on 27 June 2016).
- OECD. OECD Guidelines for the Security of Information Systems and Networks: Towards a Culture of Security; OECD, Ed.; Organisation for Economic Co-operation and Development (OECD): Paris, France, 2002. [Google Scholar]
- Seaman, C.B. Qualitative methods in empirical studies of software engineering. IEEE Trans. Softw. Eng. 1999, 25, 557–572. [Google Scholar] [CrossRef]
- Avison, D.; Lau, F.; Myers, M.D.; Nielsen, P.A. Action research. Commun. ACM 1999, 42, 94–97. [Google Scholar] [CrossRef]
- Genero, M.; Cruz-Lemus, J.A.; Piattini, M. Investigación-Acción. In Métodos de Investigación en Ingeniería del Software; RA-MA, Ed.; ACM: New York, NY, USA, 2014; pp. 171–199. [Google Scholar]
- Martins, A.; Eloff, J.H.P. Information Security Culture. In Proceedings of the IFIP TC11 17th International Conference on Information Security (SEC2002), Cairo, Egipt, 7–9 May 2002.
- Schlienger, T.; Teufel, S. Information security culture: The socio-cultural dimension in information security management. In IFIP TC11 17th International Conference on Information Security (SEC2002), Cairo, Egipt, 7–9 May 2002.
- Nosworthy, J. Implementing information security in the 21st century—Do you have the balancing factors. Comput. Secur. 2000, 19, 337–347. [Google Scholar] [CrossRef]
- Zakaria, O.; Gani, A. A conceptual checklist of information security culture. In Proceedings of the 2nd European Conference on Information Warfare and Security, University of Reading, Reading, UK, 30 June–1 July 2003.
- Zakaria, O.; Jarupunphol, P.; Gani, A. Paradigm mapping for information security culture approach. In Proceedings of the 4th Australian Conference on Information Warfare and IT Security, Adelaide, Australia, 20–21 November 2003.
- Schein, E.H. Organizational Culture and Leadership, 2nd ed.; Jossey-Bass: San Francisco, CA, USA, 1992. [Google Scholar]
- Chia, P.A.; Ruighaver, A.B.; Maynard, S.B. Understanding organizational security culture. In Proceedings of the PACIS Security Culture, Tokyo, Japan, 2–3 September 2002.
- Siponen, M.T. A conceptual foundation for organizational information security awareness. Inform. Manag. Comput. Secur. 2000, 8, 31–41. [Google Scholar] [CrossRef]
- Von Solms, B.; Von Solms, R. Incremental information security certification. Comput. Secur. 2001, 20, 308–310. [Google Scholar] [CrossRef]
- Vroom, C.; Von Solms, R. Towards information security behavioural compliance. Comput. Secur. 2004, 23, 191–198. [Google Scholar] [CrossRef]
- Chia, P.A.; Maynard, S.B.; Ruighaver, A.B. Exploring organisational security culture: Developing a comprehensive research model. In Proceedings of the IS ONE World Conference, Las Vegas, NV, USA, 4–5 April 2002.
- Helokunnas, T.; Kuusisto, R. Information security culture in a value net. In Proceedings of the 2003 IEEE International Engineering Management Conference (IEMC 2003), Albany, NY, USA, 2–4 November 2003.
- Straub, D.; Loch, K. Toward a theory-based measurement of culture. Glob. Inform. Manag. 2002, 10, 13–23. [Google Scholar] [CrossRef]
- Kuusisto, T.; Ilvonen, I. Information security culture in small and medium size enterprises. In Frontiers of e-Business Research 2003; Tampere University of Technology & University of Tampere: Tampere, Finland, 2003. [Google Scholar]
- Detert, J.; Schroeder, R.; Mauriel, A.J. A framework for linking culture and improvement initiatives in organisations. Acad. Manag. Rev. 2000, 25, 850–863. [Google Scholar]
- Taylor, M.; Murphy, A. SMEs and eBusiness. Small Bus. Enterp. Dev. 2004, 11, 280–289. [Google Scholar] [CrossRef]
- Hutchinson, D.; Armitt, C.; Edwards-Lear, D. The application of an agile approach to it security risk management for SMES. In Proceedings of the 12th Australian Information Security Management Conference, Perth, Australia, 1–3 December 2014.
- Dojkovski, S.; Lichtenstein, S.; Warren, M.J. Challenges in fostering an information security culture in australian small and medium sized enterprises. In Proceedings of the 5th European Conference on Information Warfare and Security, Helsinki, Finland, 1–2 June 2006.
- Hutchinson, D.; Warren, M. e-Business Security Management for Australian Small SMEs—A Case Study. In Proceedings of the 7th International We-B (Working for E-Business) Conference: e-Business: How Far Have We Come? Orlando, Florida, 11–13 June 2006.
- Dimopoulos, V.; Furnell, S.; Jennex, M.E.; Kritharas, I. Approaches to IT security in small and medium enterprises. In Proceedings of the 2nd Australian Information Security Management Conference, Securing the Future, Perth, Australia, 26 November 2004; pp. 73–82.
- Helokunnas, T.; Iivonen, L. Information security culture in small and medium size enterprises. In e-Business Research Forum—eBRF 2003; Tampere University of Technology: Tampere, Finland, 2003. [Google Scholar]
- Warren, M.J. Australia’s agenda for E-security education and research. In Proceedings of the TC11/WG11.8 Third Annual World Conference on Information Security Education (WISE3), Naval Post Graduate School, Monterey, CA, USA, 26–28 June 2003.
- Von Solms, R.; Von Solms, B. From policies to culture. Comput. Secur. 2004, 23, 275–279. [Google Scholar] [CrossRef]
- Furnell, S.M.; Clarke, N.L. Organisational security culture: Embedding security awareness, education and training. In Proceedings of the 4th World Conference on Information Security Education (WISE 2005), Moscow, Russia, 18–20 May 2005.
- Van Niekerk, J.C.; Von Solms, R. Establishing an information security culture in organisations: An outcomes-based education approach. In Proceedings of the ISSA 2003:3rd Annual IS South Africa Conference, Johannesburg, South Africa, 9–11 July 2003.
- Hutchinson, D.; Warren, M. Australian SMES and e-security guides on trusting the internet. In Proceedings of the Fourth Annual Global Information Technology Management World Conference, Calgary, AB, Canada, 8–10 June 2003.
- Knapp, K.J.; Marshall, T.E.; Rainer, R.K.; Ford, F.N. Information security: Management’s effect on culture and policy. Inform. Manag. Comput. Secur. 2006, 14, 24–36. [Google Scholar] [CrossRef]
- Lichtenstein, S. Internet Security Policy for Organisations. Ph.D. Thesis, Monash University, Melbourne, Australia, June 2001. [Google Scholar]
- Stanton, J.M.; Stam, K.R.; Mastrangelo, P.; Jolton, J. Analysis of end-user security behaviors. Comput. Secur. 2004, 24, 124–133. [Google Scholar] [CrossRef]
- Lichtenstein, S.; Swatman, P.M.C. The potentialities of focus groups in e-Business research: Theory validation, in seeking success in e-Business: A multi-disciplinary approach. In IFIP TC8/WG 8.4 Second Working Conference on E-business: Multidisciplinary Research and Practice; Kluwer Academic Publishers: Copenhagen, Denmark, 2003. [Google Scholar]
- Furnell, S.; Warren, A.; Dowland, P.S. Improving security awareness and training through computer-based training. In Proceedings of the 3rd World Conference on Information Security Education (WISE 2004), Monterey, CA, USA, 26–28 July 2004.
- Dutta, A.; McCrohan, K. Management’s role in information security in a cyber economy. Calif. Manag. Rev. 2002, 45, 67–87. [Google Scholar] [CrossRef]
- Sneza, D.; Sharman, L.; John, W.M. Fostering information security culture in small and medium size enterprises: An interpretive study in australia. In Proceedings of the Fifteenth European Conference on Information Systems, University of St. Gallen, St. Gallen, Switzerland, 7–9 June 2007.
- ABS. 1321.0—Small Business in Australia; Australian Bureau of Statistics: Canberra, Australia, 2001. [Google Scholar]
- Gupta, A.; Hammond, R. Information systems security issues and decisions for small businesses. Inform. Manag. Comput. Secur. 2005, 13, 297–310. [Google Scholar] [CrossRef]
- O’Halloran, J. ICT business management for SMEs. Comput. Weekly. Available online: http://www.computerweekly.com/feature/ICT-business-management-for-SMEs (accessed on 4 June 2016).
- Dhillon, G. Violation of safeguards by trusted personnel and understanding related information security concerns. Comput. Secur. 2001, 20, 165–172. [Google Scholar] [CrossRef]
- Sánchez, L.E.; Santos-Olmo, A.; Fernández-Medina, E.; Piattini, M. ISMS building for SMEs through the reuse of knowledge. In Small and Medium Enterprises: Concepts, Methodologies, Tools, and Applications; IGI Global: Hershey, PA, USA, 2013; p. 394. [Google Scholar]
- Sánchez, L.E.; Santos-Olmo, A.; Rosado, D.G.; Piattini, M. Managing security and its maturity in small and medium-sized enterprises. J. UCS 2009, 15, 3038–3058. [Google Scholar]
- Santos-Olmo, A.; Sánchez, L.E.; Fernández-Medina, E.; Piattini, M. Desirable characteristics for an ISMS oriented to SMEs. In Proceedings of the 8th International Workshop on Security in Information Systems (WOSIS11), Beijing, China, 2–5 June 2011; pp. 151–158.
- Santos-Olmo, A.; Sánchez, L.E.; Fernández-Medina, E.; Piattini, M. A Systematic Review of Methodologies and Models for the Analysis and Management of Associative and Hierarchical Risk in SMEs. In Proceedings of the 9th International Workshop on Security in Information Systems (WOSIS12), Wroclaw, Poland, 28 June–1 July 2012; pp. 117–124.
- ISO/IEC27001. ISO/IEC 27001:2013, Information Technology—Security Techniques Information Security Management Systemys—Requirements; International Organization for Standardization: Geneva, Switzerland, 2013. [Google Scholar]
- ISO/IEC27002. ISO/IEC 27002:2013, the International Standard Code of Practice for Information Security Management (en Desarrollo); International Organization for Standardization: Geneva, Switzerland, 2013. [Google Scholar]
- Sánchez, L.E.; Santos-Olmo, A.; Fernández-Medina, E.; Piattini, M. Building ISMS through the Reuse of Knowledge. In Proceedings of the 7th International Conference on Trust, Privacy & Security in Digital Business (TRUSTBUS’10), Bilbao, Spain, 30–31 August 2010; Springer: Bilbao, Spain; pp. 190–201.
- Sánchez, L.E.; Santos-Olmo, A.; Fernández-Medina, E.; Piattini, M. Security culture in small and medium-size enterprise. In ENTERprise Information Systems; Springer: Berlin, Germany; Heidelberg, Germany, 2010; pp. 315–324. [Google Scholar]




| Models | Application Framework | Human Aspect | Other Aspects | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Models Analized | Normalization | Certification | Measurement | Cultures | Progressive Adaptation | Theoretical Approach | Practical Approach | Critical Aspect | Psychological Aspects | Oriented to SMEs | Low Cost | Center of the ISMS | Dynamic Knowledge Base |
| Siponen | Yes | Yes | Yes | One | No | Yes | Si | No | No | No | No | No | No |
| Von Solms | No | No | No | One | Yes | No | Yes | No | No | No | No | No | No |
| Vroom | No | No | No | One | Yes | No | Yes | No | No | No | No | No | No |
| Dhillon | No | No | No | One | No | No | Yes | No | No | No | No | No | No |
| Eloff | No | No | No | One | No | Yes | No | No | No | No | No | No | No |
| Chia | No | No | Si | One | Yes | Yes | Yes | Yes | No | No | No | No | No |
| Helokunnas | No | No | No | One | No | No | Yes | Yes | No | No | No | No | No |
| Straub | No | No | No | Various | No | Yes | No | No | No | Yes | No | No | No |
| Kuusisto | No | No | No | One | No | Yes | Yes | No | No | No | No | No | No |
| Detert | Yes | No | No | One | No | Yes | No | No | No | Yes | No | No | No |
| Dojkovski | Yes | No | No | One | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes |
| Sneza | Yes | No | No | Various | No | Yes | Yes | Yes | No | Yes | Yes | No | No |
| MARISMA | Yes | Yes | Yes | Various | Yes | Yes | Yes | Yes | Yes | Yes | Yes | No | Yes |
| Test to Obtain a Security Culture Certificate | |||||
|---|---|---|---|---|---|
| User: | José Antonio Parra | Date: | August 12, 2014 | ||
| Part 1: Answer the question with T/F. Is it obligatory to comply with the following regulations as regards the ISMS at your company? | |||||
| Code | Regulation | Description | User’s Response | Correct Response | Mark |
| N/AS-03 | Access control | All access to security perimeters must be supervised… | F | T | 0 |
| N/AS-06 | Physical access registry | All visitors to the organization should be registered… | T | T | 1 |
| N/SE-09 | Maintenance registry | It is necessary to maintain a register of all faults… | T | F | 0 |
| N/CS-01 | Security copies | The information system security copies… | T | T | 1 |
| N/CS-03 | Premises for storage SC | The security copies should all be kept in one place… | T | T | 1 |
| N/ISI-08 | Independent review SP | The security policy should be reviewed periodically… | T | T | 1 |
| N/AT-01 | Type of access | When a third part has to access the installations… | F | T | 0 |
| N/OE-03 | Service contract clauses | All of the service contracts associated with the… | T | F | 0 |
| N/ISFI-05 | Types of security incidents | All employees or people who are contracted must… | T | T | 1 |
| N/ISFI-15 | Non-fulfillment of policies | The organization will apply disciplinary measures… | T | T | 1 |
| N/CI-03 | Inventory of assets | It is necessary to carry out an annual review… | T | T | 1 |
| N/CI-04 | Classification of Inf. assets | All information should be considered confidential… | T | T | 1 |
| N/DPT-07 | Security clause | Contracted employees should sign clauses regarding confidentiality, property… | F | T | 0 |
| N/DPT-08 | Dismissal | When an employee is dismissed, it is necessary… | T | T | 1 |
| N/AS-02 | Critical areas | The only people permitted to access critical areas… | F | T | 0 |
| Part 2: Answer the questions with T/F. Does the procedure form part of your company’s ISMS? | |||||
| Code | Procedure | User’s Response | Correct Response | Mark | |
| OS/SI-PR01 | Periodical security policy review and evaluation procedure. | T | T | 1 | |
| OS/ISI-PR02 | Procedure used to authorize access to the information system from personal installations. | F | F | 1 | |
| SP/DPT-PR01 | Pre-contracting procedure | F | T | 0 | |
| SF/AS-PR01 | Physical access control. | T | T | 1 | |
| CO/GR-PR01 | Periodical network control review procedure. | F | F | 1 | |
| The user ‘José Antonio Parra’ obtained 6.5 points (13/20) in the test taken on the [August 12, 2014], and will therefore be issued with a security culture certificate which will permit access to the company’s information system. This certificate is valid until [August 12, 2015], unless it is withdrawn prior to that date for reasons of security violations. |
| Regulation | Associated Controls | Change in Level |
| N/AS-03 | 8.3.3, 9.1.2 | −0.1 |
| N/AS-06 | 8.3.3, 9.1.2 | +0.1 |
| N/SE-09 | 9.2.4 | −0.1 |
| N/CS-01 | 10.5.1 | +0.1 |
| N/CS-03 | 10.5.1 | +0.1 |
| N/ISI-08 | 6.1.8 | +0.1 |
| N/AT-01 | 6.2.1 | −0.1 |
| N/OE-03 | 6.2.2, 10.2.2 | −0.1 |
| N/ISFI-05 | 13.1.1, 13.1.2, 13.2.1 | +0.1 |
| N/ISFI-15 | 8.2.3 | +0.1 |
| N/CI-03 | 7.1.1, 7.1.2 | +0.1 |
| N/CI-04 | 7.2.1 | +0.1 |
| N/DPT-07 | 6.1.5 | −0.1 |
| N/DPT-08 | 8.1.3, 8.3.1, 8.3.2 | +0.1 |
| N/AS-02 | 8.3.3, 9.1.2 | −0.1 |
| Regulation | Associated Controls | Change in Level |
| OS/SI-PR01 | 5.1.2 | +0.1 |
| OS/ISI-PR02 | 6.1.4 | +0.1 |
| SP/DPT-PR01 | 6.1.5, 8.1.1 | −0.1 |
| SF/AS-PR01 | 8.3.3, 9.1.1, 9.1.2, 9.1.3, 9.1.4, 9.1.5 | +0.1 |
| CO/GR-PR01 | 10.6.1, 10.6.2, 11.4.4, 11.4.6, 11.4.7, 12.5.4 | +0.1 |
© 2016 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC-BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Santos-Olmo, A.; Sánchez, L.E.; Caballero, I.; Camacho, S.; Fernandez-Medina, E. The Importance of the Security Culture in SMEs as Regards the Correct Management of the Security of Their Assets. Future Internet 2016, 8, 30. https://doi.org/10.3390/fi8030030
Santos-Olmo A, Sánchez LE, Caballero I, Camacho S, Fernandez-Medina E. The Importance of the Security Culture in SMEs as Regards the Correct Management of the Security of Their Assets. Future Internet. 2016; 8(3):30. https://doi.org/10.3390/fi8030030
Chicago/Turabian StyleSantos-Olmo, Antonio, Luis Enrique Sánchez, Ismael Caballero, Sara Camacho, and Eduardo Fernandez-Medina. 2016. "The Importance of the Security Culture in SMEs as Regards the Correct Management of the Security of Their Assets" Future Internet 8, no. 3: 30. https://doi.org/10.3390/fi8030030
APA StyleSantos-Olmo, A., Sánchez, L. E., Caballero, I., Camacho, S., & Fernandez-Medina, E. (2016). The Importance of the Security Culture in SMEs as Regards the Correct Management of the Security of Their Assets. Future Internet, 8(3), 30. https://doi.org/10.3390/fi8030030