1. Introduction
Recent developments in microelectronics have produced low-power, low-cost, high-performance sensor nodes with sophisticated communication facilities. These devices can gather information about their surrounding environments once they have been deployed in small or large areas. These are generally referred to as Wireless Sensor Networks (WSN) [
1].
One of the most important constraints in sensor networks is energy capacity. Usually, a sensor node is deployed in a broad area with a small battery attached to it. Sometimes, the node can receive its power from the environment (such as solar power), but more often, nodes are energy-bound. In such conditions, a more energy efficient sensor network is required to effectively overcome the energy problem.
Also, as many nodes are deployed in a large area and many geographical or organic obstacles can be encountered in sensor network environments, flexibility and reliability become increasingly important [
2]. For instance, the weather can change frequently, and a new obstacle can affect the operating status of the node, or any other adverse condition, resulting in the connections between nodes to be on and off sometimes. Additionally, for dense networks where many sensor nodes are deployed to monitor a target more precisely, a faster and highly reliable data delivery mechanism is required. However, it is not easy to gain both energy efficient and reliable sensor networks simultaneously.
For saving the energy of the sensor network, we can use an energy efficient routing [
3], an energy efficient medium access control [
4], or both [
5]. Also, many versions of managing radio activity to conserve energy are introduced. In this paper, a medium access control and a wakeup scheduling scheme for sensor networks are introduced. This scheme is energy efficient because it effectively reduces the operational energy by controlling the activation schedule of the sensor node. In addition, the scheme provides a traffic distribution and backup route mechanism for efficient energy use in sensor nodes. This scheme is based on some of the previous sleep-based slot protocols for WSNs.
3. Time Tree Medium Access Control
The data paths in the network consist of multiple time trees that have different activation time schedules. Each node of the tree activates according to its depth on the tree and sends data to the BS (base station) node, the root of the tree. A sensor node that wants to send data to the BS node, activates at the predefined activation time and sends data to the parent node of the tree. The data sent in the direction of the parent node travels along the node of the tree activated by the time tree schedule and finally arrives at the BS node. Each branch of the tree activates at a different rate according to the schedule of the time tree that is configured to application traffic requirements.
The exchange of data frame is sequenced by the RTS-CTS-DATA-ACK procedure. Each node uses a back-off algorithm to reduce collision when accessing the wireless channel, reactivates at predefined times later, and retries data transmit when the node fails to send data successfully. This continues until the node successfully ends the data-sending sequence within a predefined retry number.
3.1. Time Tree Configuration Algorithm
A time tree is a tree or a group of trees rooted at a target base node. A tree is composed of one or more branches. Basically, the tree configuration is performed by all nodes that operate autonomously and distributedly. For the configuration of the tree, the root node broadcasts tree messages periodically. Each node performs the following operation for the configuration and extension of the tree after receiving the tree message.
| Node’s Basic Operation for the Configuration of the Tree |
|---|
Add the sender node of the tree message to the parents group. Select the best parent node from the parents group. Make a parent-child relationship with the selected parent. Broadcast a tree message to neighbor nodes.
|
The operation of the node for the configuration of the tree is based on the breadth-first search algorithm. At first, the nodes that can be reached from the root node are searched. These nodes become the first level nodes of the tree. These nodes make the root their parent, and extend the tree by sending a tree message and searching for their children. From this time, nodes will receive many tree messages from their neighbors already configured as a member of the tree. All nodes receiving the tree message select a message, a parent node that has the best condition for sending the data to the root node. After joining to the parent as a child member of the tree, the node broadcasts a tree message. This process continues periodically and finally all nodes in the network are included as members of the tree.
A child node selects its parent node. A child node sends a join message to the chosen parent to make a parent-child relationship for the tree. The most preferred metric when choosing a parent node is the tree level of the parent. The node that has the lowest level is selected as a parent. A tree level is a hop-count from the root node. This criteria eliminates the possibility that a loop may exist along the path to the root node.
The next important metric for selecting the parent is the traffic load. By choosing the light-loaded parent, the node can effectively send the data with the best opportunity to avoid collision and additional delay. This also distributes network traffic among nodes, so the network can reduce the dissipated energy and enlarge the lifetime of the network.
When we know the exact traffic load that the parent had, we can use the load as a metric for the tree configuration. If this metric is not allowed or cannot be used for some other reason, we can use other parameters that reflect this traffic metric. Some of these parameters include the number of children, the number of all descendants, and the number of parents of the same branch. Other parameters, such as the energy required to send data to the root node, the signal strength, or the distance to the parent node, can be useful parameters for the configuration of the tree.
When a parent node is down, the relationship between the parent and the child node is broken. Then, the child node searches another parent node from the parents group as the second procedure described in the node’s basic operation. It is same with the occurrence of an obstacle between nodes, or movement of a sensor node to another place.
3.2. Topology of the Tree and Data Sending Cycle
There are some optional parameters for representing the tree characteristics in a tree message. These include the tree identifier, the branch identifier, tree level, the number of parents in forming a time tree. The tree identifier is a unique identifier of the data sink. A time tree is created per sink node in WSN. The sink node will be a root of the tree that has an identifier and instance of the sink. The identifier of the branch is a number that is given to the node of the first level in a tree. This value is fixed when the first-level node established a relationship with the root node. The number of parents in forming a time tree defines the number of trees that rooted at the originator of the tree message. If this number is one, every node makes a parent-child relationship with only one parent to each tree identifier.
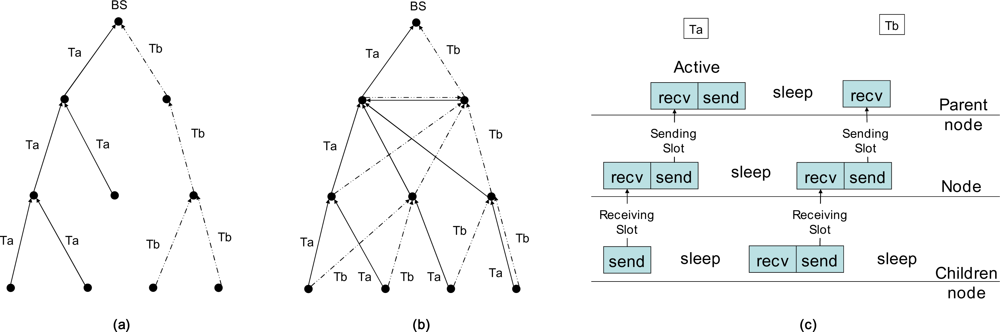
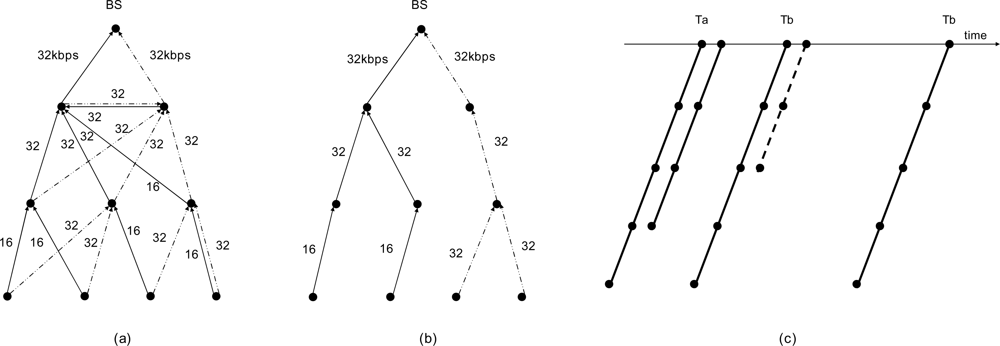
Figure 1a is such a case. If this number is two, every node makes two different parent-child relationships to each branch identifier of the same tree identifier.
Figure 2b is the result of this scheme. If this number is zero, every node of the network will make a parent-child relationship with each parent that sent a tree message with each different branch identifier of the same tree identifier.
In
Figure 1, there is a time tree that consists of two branches or trees,
Ta and
Tb, in the network with different branch identifiers of the same sink node (root). In
Figure 1a, each node makes one parent-child relationship for each tree identifier. In this scheme, a branch identifier is ignored. Each branch of this tree is separated from each other. Each branch is activated independently, so we can reduce the number of nodes activated at the same time. If we reduce the number of activated nodes, we can reduce the probability of collision and minimize the required energy to send the data to the root. If we can know the exact point of the node location, we can increase the distance between nodes that are activated at the same time. This helps the network lifetime and gains other performances more.
In
Figure 1b, the trees
Ta and
Tb are folded. The first child of the root node acts as a virtual root of the tree. Each node has a different parent as with different branch identifiers. Each node regards each tree of different branch identifiers as different trees. The advantage of this topology is a distribution of network traffic and provision of an alternate route to the same sink.
The data transmission of a node occurs from the sensor node to the root node sequentially along the tree like DMAC [
12]. A child node sends data to its parent node, and the parent node receives the data at the same slot time. Next, the parent node sends the data to its parent node at the next slot of time. This cycle continues to the root node along the tree as in
Figure 1c.
After sending data to its parent, the node sleeps until the next scheduled receiving time. The sleep time of a node is more than three times that of an active time [
23]. The active time is composed of a receiving and a sending slot time. The distance between nodes differs with a node’s position in the network. So, the safe sleep time to eliminate the interference coming from other node's activity is more than five times the active time [
23]. The ratio of an active time with a sleep time is an activation rate. Generally, an activation rate can be less than several percent.
The sending time of a node is determined by a scheduled activation scheme. Each node is activated by the level of the tree and the position of the branch it included. The child node of the root should send data at the receiving slot of the root, and the node should receive the data from its child at one slot before its sending slot.
In general, there is one receiving and one sending slot in one active time; however, the number of receiving or sending time slots can be more than one if required. If one slot is allowed in one active time, one sending slot is followed after one receiving slot. If two slots are allowed in an active time, two consecutive sending slots are followed after two receiving slots. The number of active slots in one frame can be configured differently in each branch or tree. In most cases, it would be a good choice for using one active slot; however, if heavy traffic exists in sensor networks, more consecutive active slot mechanisms would be more efficient, but more than one active slot system adds additional delay per node and thus increases end-to-end latency.
In the other case, you can set the active slot number differently as with the depth of the sensor node in the tree. The traffic gathers and goes to the near root side. It would be more effective if more slots are assigned at the root side of the tree than the far side of the tree. This scheme can lessen the energy of the edge node. Therefore, the edge node can use more energy in sensing and processing the event of its environment than sending or relaying the data.
One simple implementation method of this variable numbers of active slot is by varying the length of a slot. As the length of a slot increases, more than one frame can be sent to a parent node from several child nodes.
3.3. Time Tree Scheduling (TTS)
At first, the active slot for data receiving and sending is activated at a minimum rate, called a basic rate. One active slot is activated in a frame, a predefined unit time. As traffic increases, the activation rate is increased twofold. Accordingly, the time tree Ta is activated two times in a frame. If the traffic increases more, the activation rate is increased as twofold compared to the current rate. The frame length is not fixed value. It can be varied as with the application environment, from a few seconds to several hundreds of seconds.
The wakeup time
tw (
n,k) and the starting time of sending slot
ts (
n,k) of a node
n in the
i-th branch with the tree depth of
d is represented as follows:
Here, k has an integer sequence value of (–∞, +∞); τf is a frame length; τs is a slot length; θi is a time shift of the i-th branch from the starting time of the frame; r is a data rate index of the i-th branch, and its integer value is 1 when it is the basic rate and R when it is the maximum rate. θi can be represented as aτs, where a is an integer value from 0 to the total slot number of a frame, S.
Then, (1) and (2) can be rewritten like this:
If ts (m,k) and ts (n,k) are the same for some a, d, k and the node n is within reach from the node m, then the nodes m and n are in a same collision area. At this time, RTS and CTS work effectively to avoid collision.
3.4. Medium Access Control Operation
The proposed medium access mechanism conforms to the operation of the carrier senses collision-detection and collision-avoidance (CSMA/CA) protocol. The node that wants to send data sends an RTS frame after checking the wireless media and waits for receiving a CTS frame. After successfully receiving the CTS, the node sends a DATA frame and receives an ACK frame of the receiving node. The nodes that want to send data are children nodes, and the receiving nodes are parent nodes. There can be many nodes connected to a parent, so many nodes could be activated at the same time and attempting to simultaneously send data. Also, more than one parent node can be activated at the same time.
When child nodes attempt to send data to their parent, there can be a data collision at the wireless media. This collision causes data-sending failure at children nodes. When there is more than one parent activated together, many children nodes try to send data simultaneously. At this time, the RTS and CTS mechanism resolves the arbitration to seize wireless media. As a result, only one node can successfully send data and others defer to send their data at next activation time.
So, when nodes are densely deployed, many parent nodes will be activated at the same time. To avoid the arbitration of the wireless channel, each branch must activate at different times between nodes. For this reason, when a node selects its parent, choosing a parent that has different branch identifier is ideal. Then, the activation time will be different by the
equation (3). In
equation (3), a different offset value means a different branch identifier and thus a different activation time. For this, each node should know the branch identifier of its neighbors. This information can be known by the parameters included in a tree message. A tree message has a branch identifier and a depth level of the nodes.
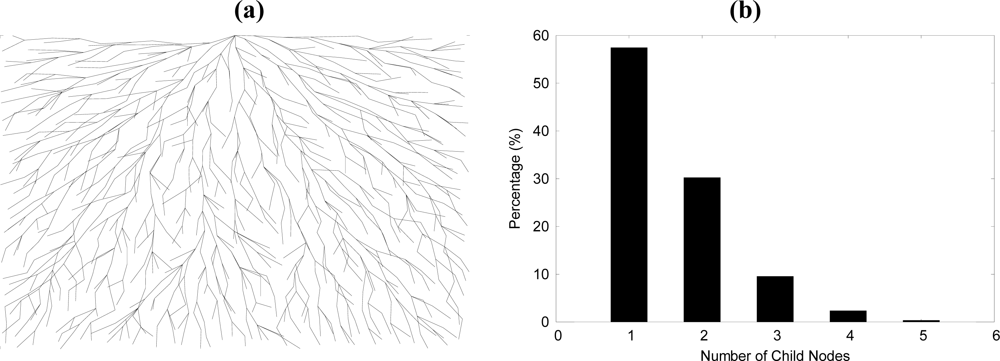
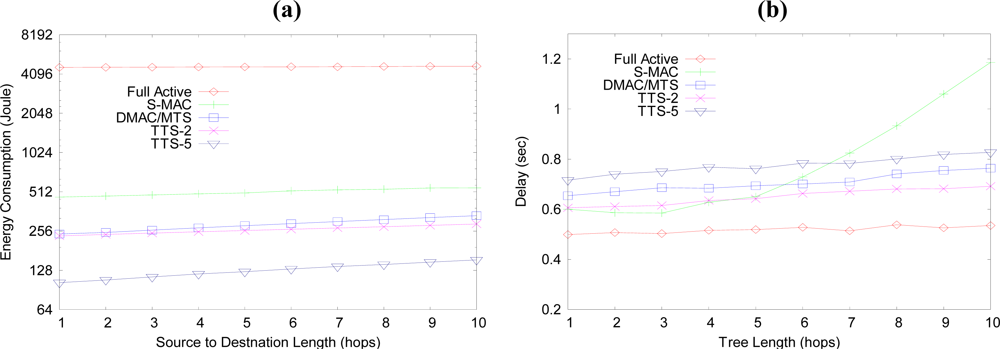
Figure 2 shows the result tree of the sensor network with 1,000 nodes.
Figure 2a is case of previous algorithm that choosing a parent with minimum node of same branch identifier.
Figure 2b is a percentage graph of number of child nodes at each node. The average number of child nodes of each node is 1.58 and more than 99.5% nodes have maximum 5 children.
A child node receiving a tree message completes the following operation after seeing the parameters of the message: if the node has no parent, the node sends a join request message to the sender of the tree message. If a parent node exists and the computed best parent is different with the current parent, the node sends a join request message to the newly searched best parent. After receiving a join accept message from the best parent, the node broadcasts a tree message. If the parent exists and the computed best parent is same, the node broadcasts a tree message to neighbor nodes.
A parent node receiving a join request message does the following operation: first, the node checks whether the parameter information in the request message is the same as the information it has. If it is the same, the parent node adds the node into a group of children node. Then, the node increases the child number of it and sends a join accept message to the child node. If it is not the same, the node sends a join deny message to the requested node with node parameters of it. The parameters in a join request, accept- and deny-message are same with the parameters in a tree message. It includes a tree and a branch identifier, tree level, parent number, children number and activation rate. After receiving a join deny message, each node does the following operations. First, the node updates the parent information using the information in the join deny message. Then, the node searches a new best parent and sends join request message.
3.5. Backoff Algorithms and Retransmission Scheme
Because the wireless channel is shared among all nodes, the node must seize the channel before sending data. The operation of this protocol is based on CSMA/CA. In CSMA/CA, every node checks the media before sending a data. Because there can be more than one node that tries to send data, each node must wait some random time to avoid data collision after the media is free. This waiting time is the backoff time, and it must be different from node to node. In IEEE 802.11 standard [
7], the lowest value of wait time is 32 and the highest value is 1024, but in this proposed scheme, there are not many nodes attempting to send data,
i.e., around ten or less. Therefore, in our scheme, the maximum value is set to 32 or 127.
At first, each node generates a random number between 0 and 32. Then, each waits the random number of slots before sending an RTS. If the backoff timer expires, the node senses the channel and if the medium is free, the node sends data to the wireless channel. If the medium is busy before the expiration of the backoff timer, the node pauses the backoff timer and resumes it later. At the next activation time, the initial value of the backoff timer is refreshed and restarted again. The node that wants to send data must send an RTS frame and waits for receiving a CTS. If the receiving node does not respond to this RTS, the CTS timer expires at the sending nodes. Then, the sending node retries again by sending an RTS after the expiration of the CTS Timeout.
A data exchange procedure is completed when the node sends a DATA and receives an ACK from the recipient node after seizing the channel by exchanging an RTS and a CTS frame. The failure of a data exchange occurs mainly for three reasons. One reason is a failure to seize the wireless channel. Before sending an RTS, other node can seize the channel by sending an RTS frame. The other reason is the collision of frames. The collision of RTS can lead to non-response of a CTS frame. Then the node sends an RTS again after the CTS timeout. If the CTS retry number goes over the maximum retry number, the node must retry the data sending procedure at next active time. Another reason for data sending failure is if the receiving node is unready to exchange data. The receiving node can be out of power or not wake up in time for some reason. At any rate, the sending node will try to send an RTS until the retry number has reached the maximum retry limit.
The sleep time of a node is long compared with the active time, which means that if a node retries at next scheduled wakeup time, the delay will be very long. So, without waiting for the next normal scheduled active time, the node can retry at some predefined times after the current active time. If a failed node retries directly after the current active time, it will interfere with the data exchange of its parent node. Therefore, the node should retry the data sending procedure after some cycles wait. This retry interval should, at a minimum, be greater than three active times. The suitable value for this could be five or more to avoid data interference.
Normally, each station will sleep until the next normal scheduled time. So, if a node wants to send data during a retry active time, it sends a DATA frame with one more data bit set to one in the Frame Control (FC) field. Then, the parent will know it and respond with an ACK frame with an additional data bit set. If there is no data to send, it sends an RTS with a duration value of zero in the duration field and one more data bit set in the FC field. We call it as a zero RTS or a zRTS frame. The value of the duration field at this zRTS frame reflects only the time value for the receiving of CTS frame. If there is more than one node that wants to get a retrial data exchange, a zRTS arbitration will occur. If a parent receives a zRTS well, it responds with a CTS and will wake up at the retry activation time. After this zRTS-CTS exchange procedure, the current active slot will end without the real data exchange. It is only a sign of demanding retry slot between the child and parent node. The value of zero duration of FC field at an RTS frame makes it possible for other zRTS-CTS procedures right after this exchange procedure.
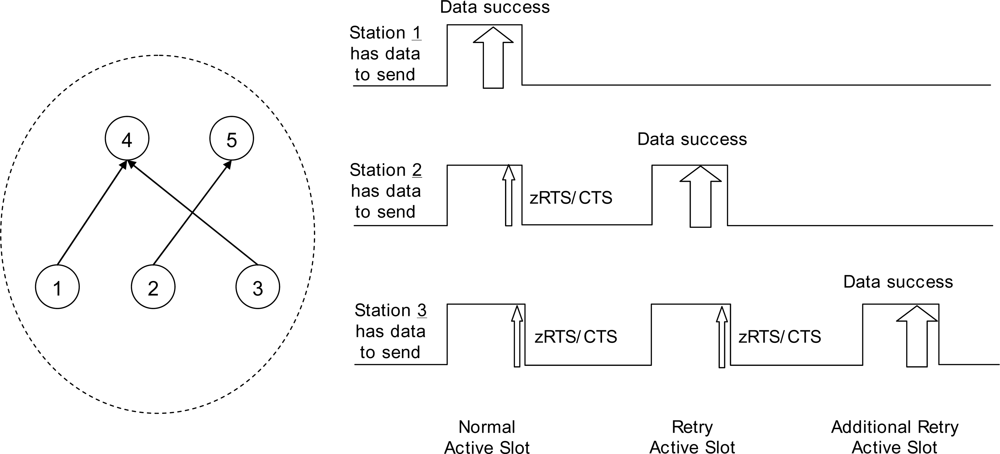
Figure 3 shows the operation of data sending at three nodes. They are all on the same level of the tree. Their parents may be the same or different. At the normal wakeup schedule time, station 1 seizes the channel and finishes the data exchange procedure successfully. Stations 2 and 3 send a zRTS frames after the data exchange. There will be an RTS arbitration, and nodes 2 and 3 successfully finish a zRTS-CTS exchange. Nodes 4 and 5 will wake up at the retry active time. At the first retry active slot, station 2 successfully finishes data exchange and station 3 sends a zRTS. Next, at the more retry active slot, station 3 successfully finishes data exchange with its parent.
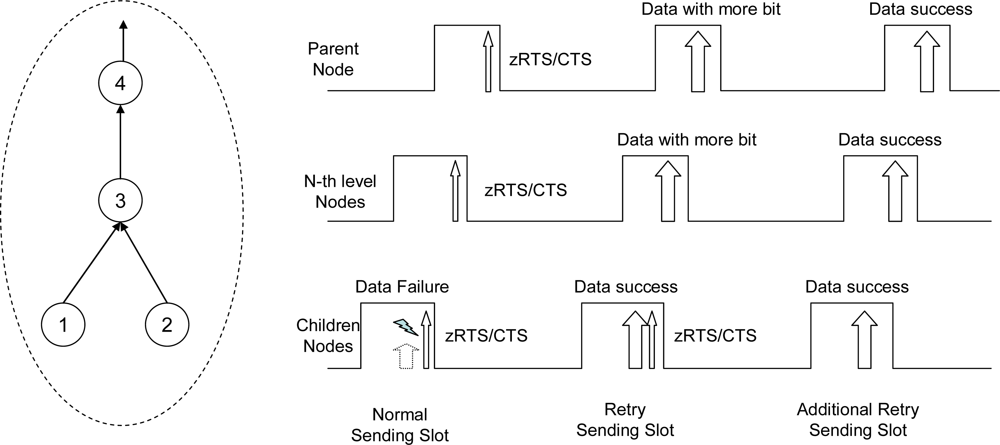
Figure 4 shows the operation of the data sending procedure along the tree to the root direction. Stations 1 and 2 have data to send, and at the normal sending slot, they fail the data exchange. When there is not enough time in the current sending slot, each node must stop the data sending procedure and start to send a zRTS for the reservation of retry active slot. Stations 1 and 2 exchange zRTS-CTS frames before ending the current slot. Station 3 sends a zRTS frame to its parent for sending data from the children node at the retry active slot. Station 4 relays this zRTS frame to its parent and this continues to the root along the tree. Station 1 finishes data sending at the retry sending slot after successfully seizing the wireless channel. Right afer this data exchange, node 2 sends a zRTS. After node 3 responds to node 2 with a CTS at receiving slot, it sends a DATA to its parent with a more data bit set for the reservation of additional retry slot. In the additional retry sending slot, node 2 sends data to node 3 with a cleared more data bit and the additional active slot ends.
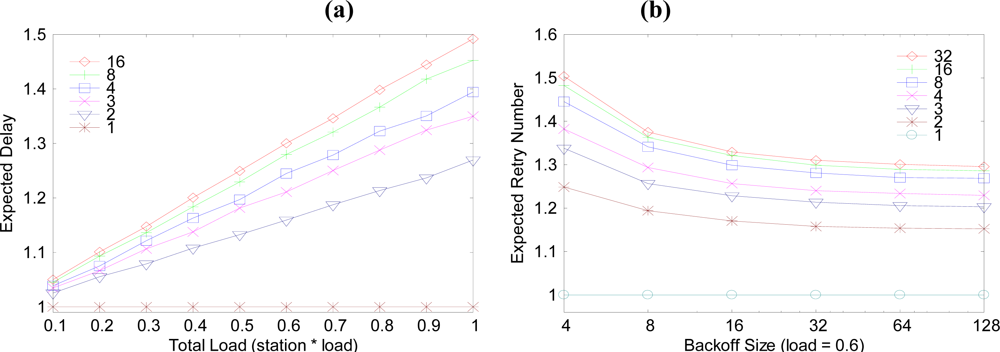
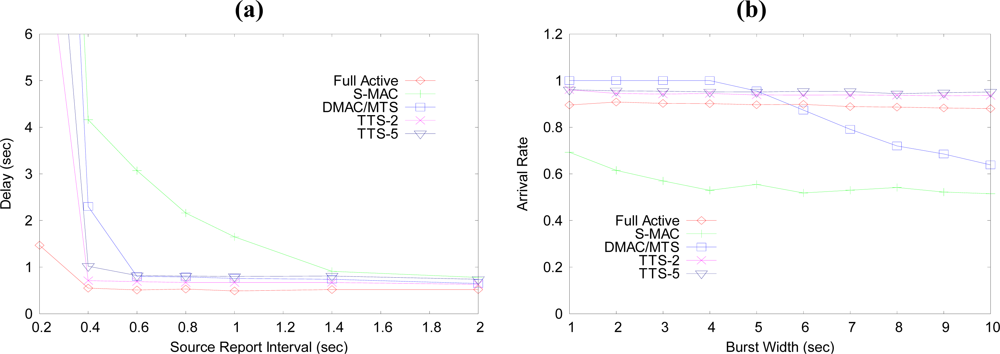
Figure 5a is a graph of the expected delay from the child node to parent node. In this graph, the child node number of one parent is varied from 1 to 16, and 32. When the child node is one, the expected delay is 1 slot time. As the child node number increases, so do the expected delay and the traffic load. The delay difference between the node numbers 1 and 2 case is bigger than the delay between 2 and 3. So, the one-to-one parent-child case is the best case.
Figure 5b explains the expected retry number of data sending procedures between a child and a parent. The difference between 32 and 127 is not much more than expected. It would be more efficient using 3 times retry with maximum 32 backoff slots than using one time retry with maximum 127 backoff slots.
3.6. Rate Adaptation to the Traffic Load
The bandwidth of a sensor network can be expressed by its activation rate. At first, every branch of the tree activates at a basic rate. If the traffic load increases, the overflow traffic can be transferred at retry active time. If the number of retries increases, it is more efficient data to send at an increased activation rate than the basic rate with every additional retry. Then, the activation rate is increased twofold. If the traffic increases more, the activation rate is increased twofold again.
By this procedure, the rate can be increased to the maximum rate. If the node has more than one tree to the same target node, the node can distribute traffic to each tree of the time tree. Then, the possible maximum data rate is the sum of data rate of each tree of the time tree.
If periodic reporting is required, the root node can reserve data bandwidth of some branch of the tree. The reservation of the bandwidth begins with root node (centralized) or sensor node (distributed). The root node defines the activation rate of each branch of the tree. If the overall bandwidth is increased, the node increases the activation rate of the branch. A sensor node can increase the bandwidth of the branch along the path from it to the root node. If a request of bandwidth increasing sent from a sensor node to the root direction, each parent increases the bandwidth of the branch by reserving retry active slot as required. If the current bandwidth is 16 kbps and a sensor node reserves 16 kbps more, then one additional retry active slot is scheduled automatically after a normal activation schedule. Certainly, the branch can be activated if more data should be sent after the reserved retry active slot. As a result of the reservation, the activation rate of the branch is different at each path of the branch. In near side of the root, the bandwidth of a branch can be larger than that of the branch of a leaf side.
Figure 6 shows the activation rate and the activation cycle. In
Figure 6a and
6b, each number represents the activation rate of the path at each branch. This rate is different at each branch and tree. Even in a same branch, the rate is different at the leaf side and the root side.
Figure 6c shows a stream of activation events from the leaf to the root side. The solid line represents a reserved cycle and the dotted line represents a retry activated cycle at each node. In
Figure 6c,
Ta and
Tb have same activation rate.
Ta has a basic rate and additional activation rate requested by a node in the branch.
Tb has a doubled activation rate than
Ta and a temporal retry activated cycle.
3.7. Time Synchronization and Routing Function
The RTS and CTS mechanism provide a time to prepare a node to be ready for data exchange. Generally, all nodes of a network must be timely synchronized for successful and correct data exchange. If a node wakes up early or late, the data exchange process can operate abnormally. At this time, the RTS and CTS mechanism provides timing adaptation to this situation.
A routing operation takes place at a source node and a node that detects a node failure of its neighbors. All routing data are destined for each root of the tree. At a source node, a time tree is selected as with the destination of the data. Then, the source node selects a suitable branch of the found tree and the node sends the data to its parent of the branch. Afterward, each data is relayed along the branch of the tree.
While passing along the branch, the next node of the data is found at the MAC layer of each node. All intermediate nodes of the branch operate like a bridge. Each node of the branch is activated at a specific time to send the data to its parent. A node has multiple parents, one for each destination. The activation time is different for each branch of the tree. Even if the activation time is the same, the node can know the parent node by the destination information of the data frame.
If there is a node or link problem in a branch, the node won’t send data to its parent. Instead, the node will send a message to the upper layer, and then the node should refer to the routing table to find a suitable other branch of the time tree targeting to the destination of the data. This operation can occur when there is a heavy congestion when it is impossible to send the data within a permissible delay tolerance. If data is distributed to two trees of the same destination, minimum data can be delivered to the destination even though one of its trees has a problem, and the other branch or tree of the time tree can be used as a backup route to the destination.