Design and Feasibility of a Safe Pill Bottle
Abstract
:1. Introduction and Background
2. Materials and Methods
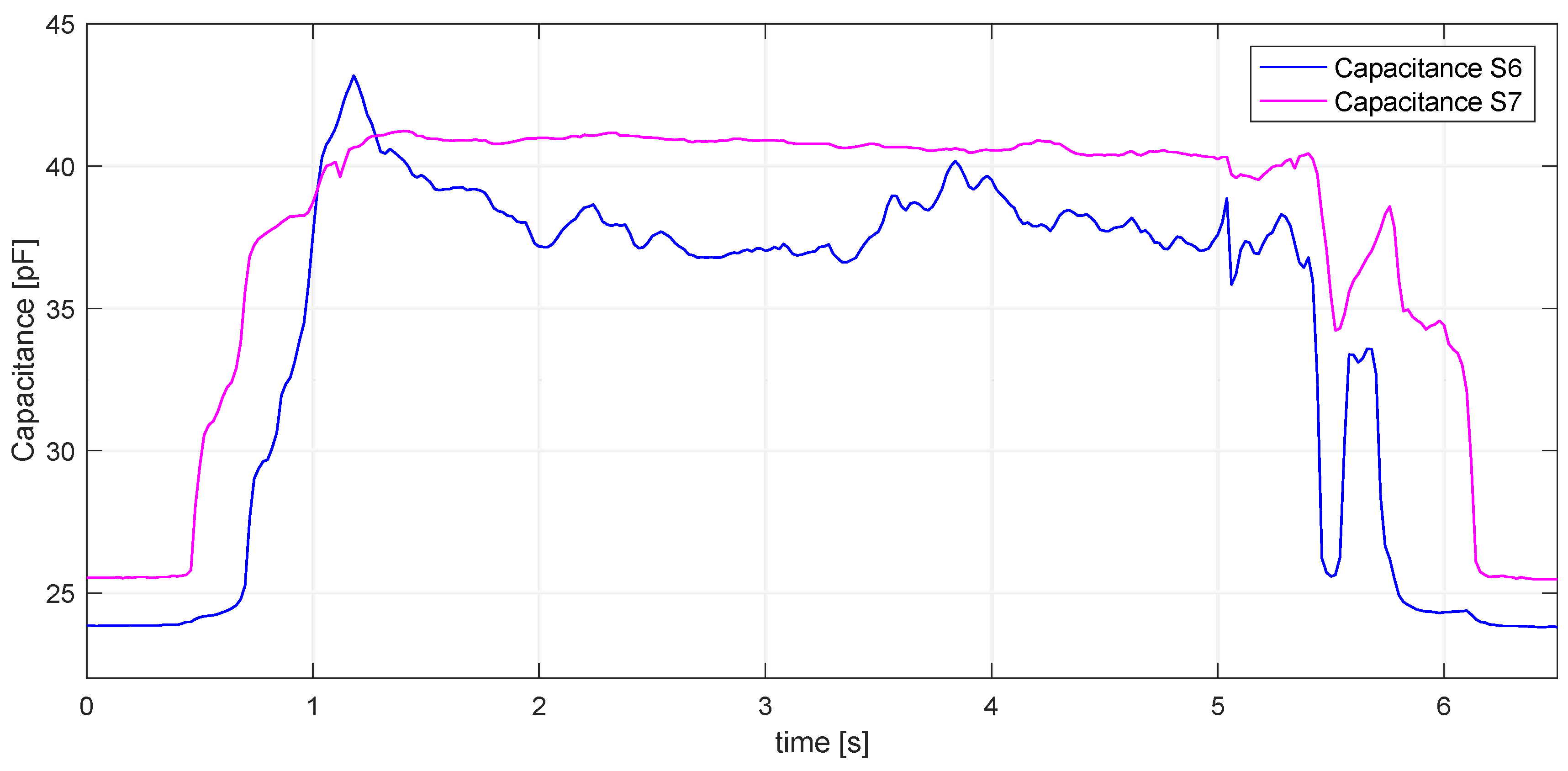
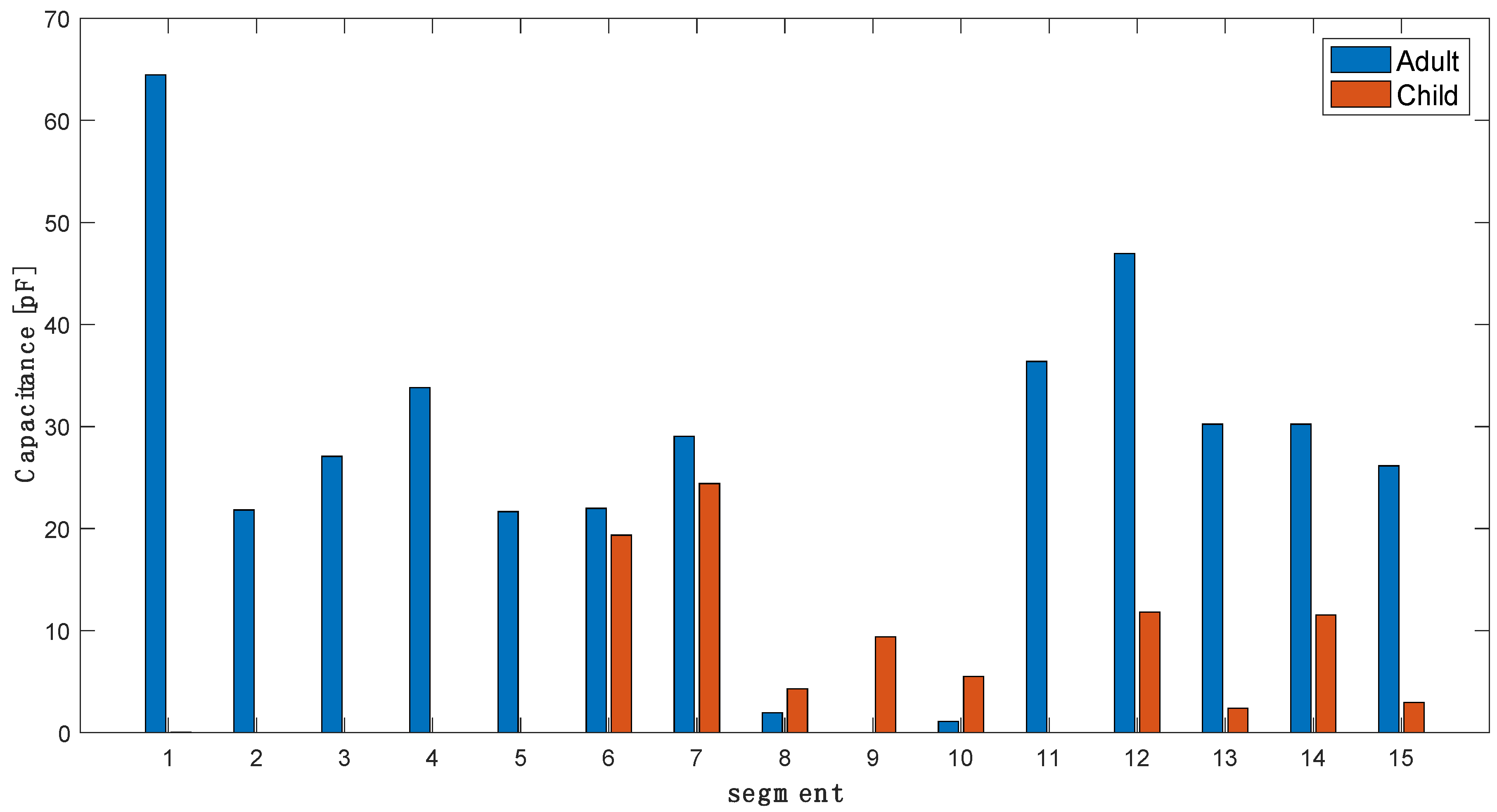
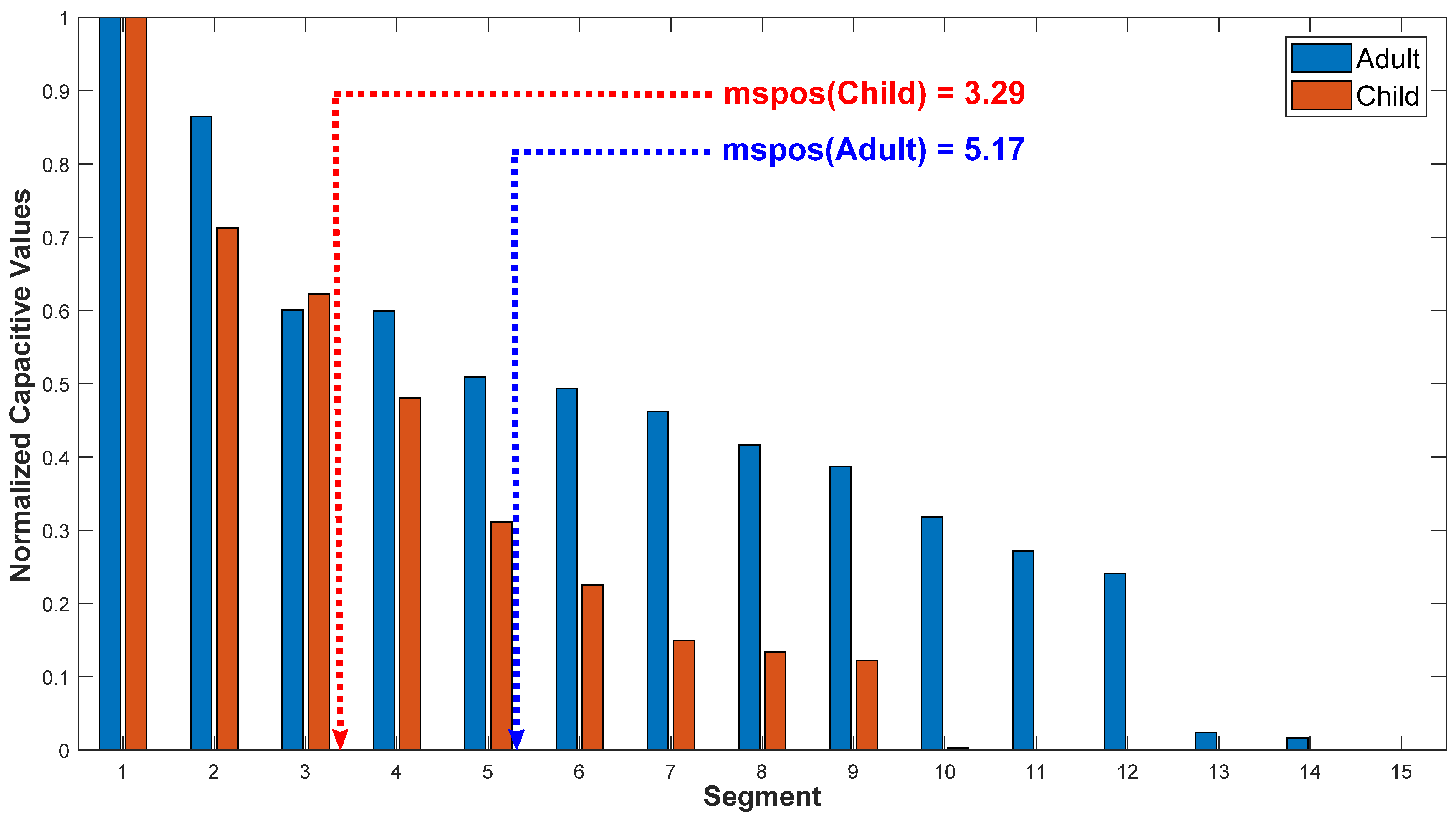
2.1. Signal Processing and Feature Selection
- tRCC—total relative change of capacitance as the sum of all relative changes CRi, i = 1…N
- CRmax = max(CRi), i = 1…N
- CRNi—normalized change of capacitance
- tRCCN—normalized total relative change of capacitance, calculated as sum of all normalized changes of capacitance according to Equation (3)
- mspos—mid-segment position, calculated as a center of gravity of the sorted set of relative capacitances CRsorti
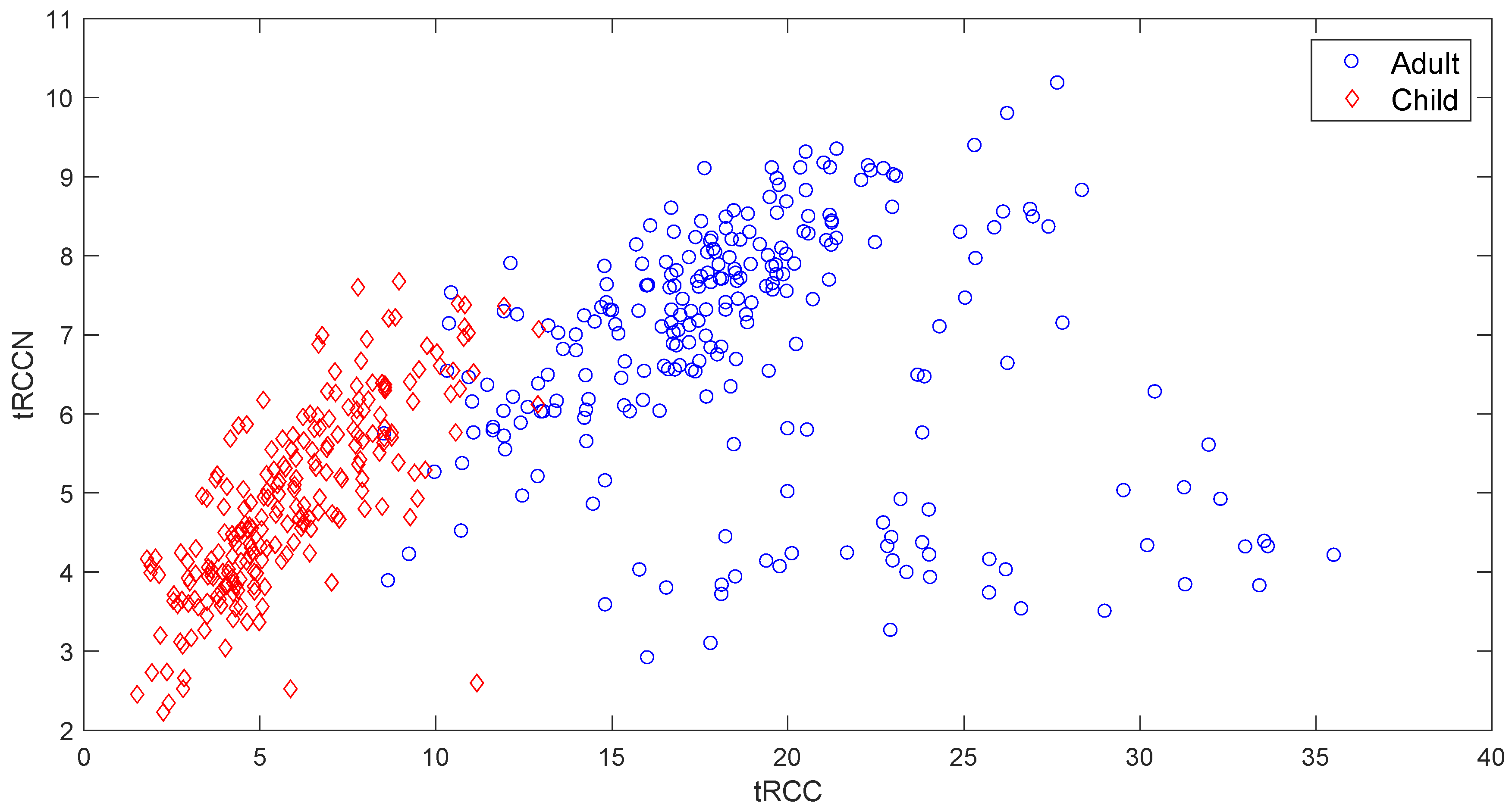
2.2. User Identification
- CCdiff—difference of total capacitance from average total capacitance for all children (CCmean):
- CAdiff—difference of total capacitance from average total capacitance for all adults (CAmean):
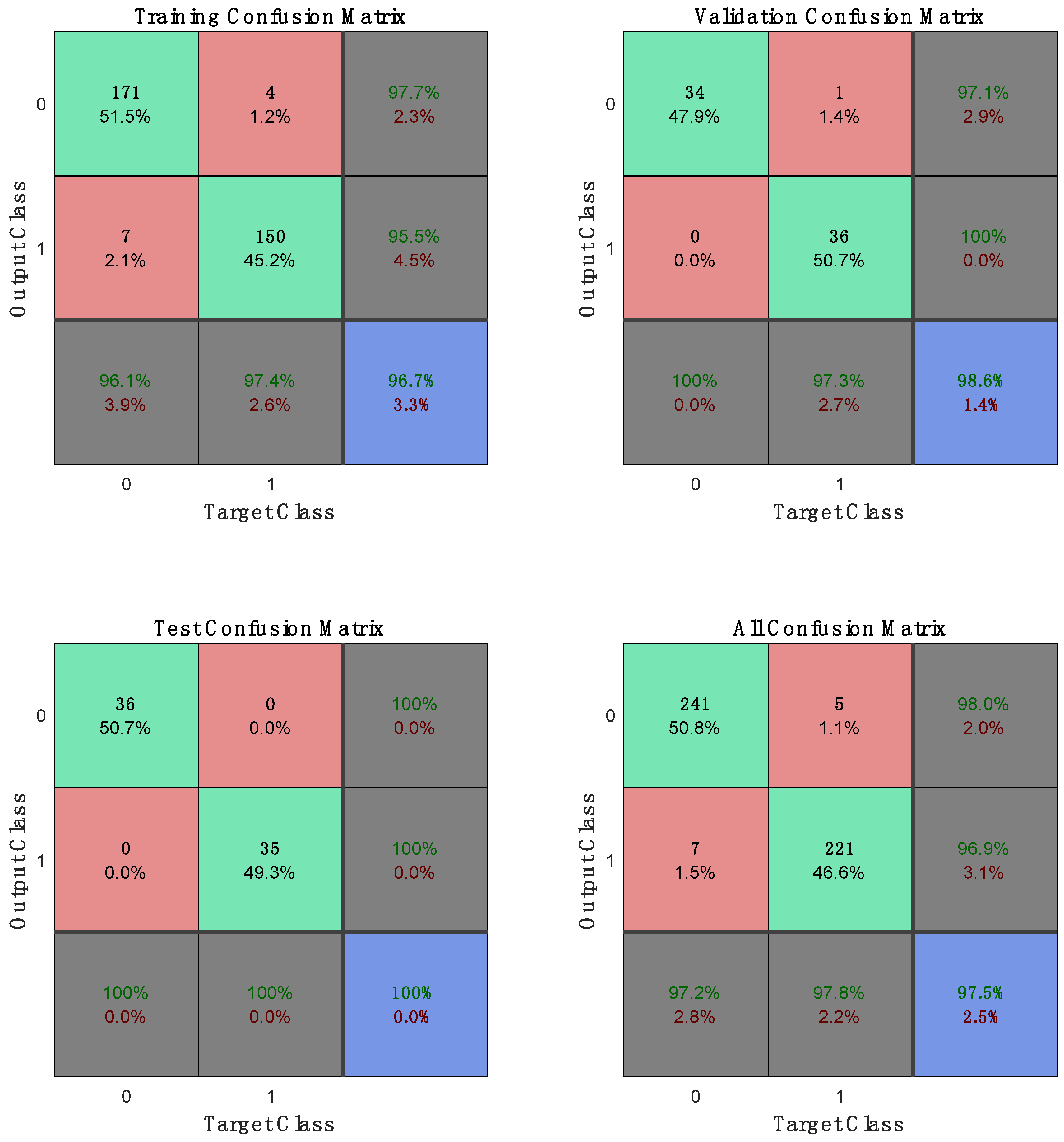
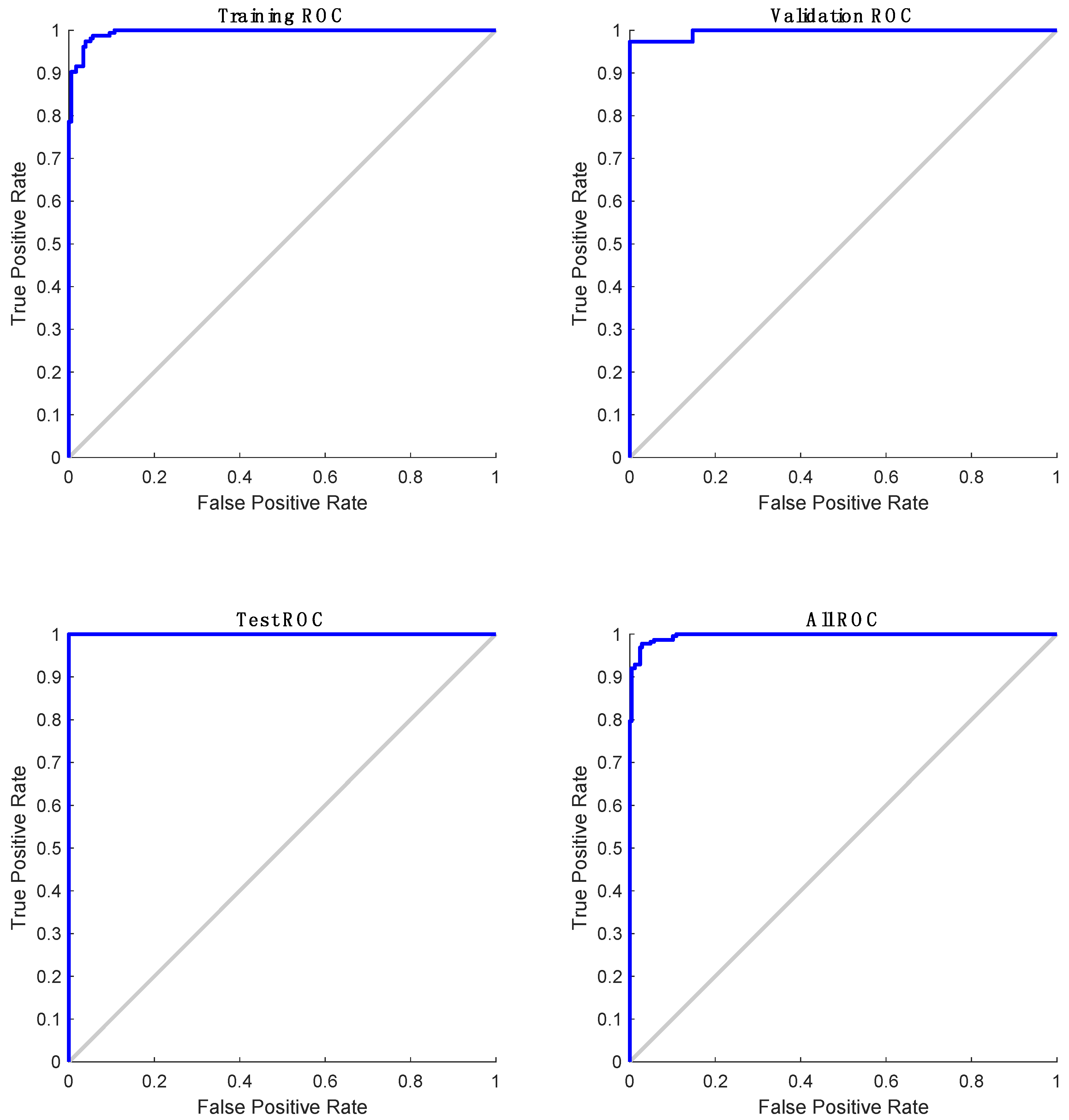
3. Results
4. Discussion
5. Conclusions
Author Contributions
Acknowledgments
Conflicts of Interest
References
- Schwebel, D.C.; Evans, W.D.; Hoeffler, S.E.; Marlenga, B.L.; Nguyen, S.P.; Jovanov, E.; Meltzer, D.O.; Sheares, B.J. Unintentional child poisoning risk: A review of causal factors and prevention studies. Child. Health Care 2017, 46, 109–130. [Google Scholar] [CrossRef]
- Mowry, J.B.; Spyker, D.A.; Cantilena, L.R., Jr.; McMillan, N.; Ford, M. 2013 Annual Report of the American Association of Poison Control Centers’ National Poison Data System (NPDS): 31st Annual Report. Clin. Toxicol. 2014, 52, 1032–1283. [Google Scholar] [CrossRef] [PubMed]
- Schwebel, D.C.; Wells, H.; Johnston, A. Children’s Recognition of Dangerous Household Products: Child Development and Poisoning Risk. J. Pediatr. Psychol. 2015, 40, 238–250. [Google Scholar] [CrossRef] [PubMed]
- Nierenbert, C. Medication Leading Cause of Child Poisoning in U.S. Available online: http://www.webmd.com/children/news/20120320/medication-leading-cause-child-poisoning-us#1 (accessed on 4 February 2018).
- Meng, W.; Wong, D.S.; Furnell, S.; Zhou, J. Surveying the Development of Biometric User Authentication on Mobile Phones. IEEE Commun. Surv. Tutor. 2015, 17, 1268–1293. [Google Scholar] [CrossRef]
- Sajedi, H.; Moghaddam, B.G. Personal Authentication by Palmprint Using Contourlet Transform and k-Nearest Neighbour Classifier. Int. J. Mach. Intell. Sens. Signal Process. 2016, 1, 287–303. [Google Scholar] [CrossRef]
- Fei, L.; Xu, Y.; Zhang, D. Half-orientation Extraction of Palmprint Features. Pattern Recognit. Lett. 2016, 69, 35–41. [Google Scholar] [CrossRef]
- Zhang, L.; Shen, Y.; Li, H.; Lu, J. 3D Palmprint Identification Using Block-Wise Features and Collaborative Representation. IEEE Trans. Pattern Anal. Mach. Intell. 2015, 37, 1730–1736. [Google Scholar] [CrossRef] [PubMed]
- Barel, A.O.; Clarys, P. Skin Capacitance. In Non Invasive Diagnostic Techniques in Clinical Dermatology; Springer: Berlin/Heidelberg, Germany, 2014; pp. 357–366. [Google Scholar]
- Whitmore, A.; Agarwal, A.; Xu, L.D. The Internet of Things—A survey of Topics and Trends. Inf. Syst. Front. 2015, 17, 261–274. [Google Scholar] [CrossRef]
- AdhereTech. Available online: https://adheretech.com/ (accessed on 3 May 2018).
- Talukder, B.B.M.S.; Jovanov, E.; Schwebel, D.; Evans, D.W. A New Method to Prevent Unintentional Child Poisoning. In Proceedings of the 40th International Conference of the IEEE EMBS Engineering in Medicine and Biology Society, Honolulu, HI, USA, 17–21 July 2018. [Google Scholar]
- Teensy LC (Low Cost). Available online: https://www.pjrc.com/teensy/teensyLC.html (accessed on 11 December 2017).
- Teensy 3.2, PJRC Store. Available online: https://www.pjrc.com/store/teensy32.html (accessed on 3 May 2018).
- Teensy 3.6. Available online: https://www.pjrc.com/store/teensy36.html (accessed on 11 December 2017).
- Adee, S. Guns That Fire Only for You. New Sci. 2015, 227, 25. [Google Scholar] [CrossRef]
- Jovanov, E.; Nallathimmareddygari, V.; Pryor, J. SmartStuff: A Case Study of a Smart Water Bottle. In Proceedings of the 38th Annual International Conference of the IEEE Engineering in Medicine and Biology Society, Orlando, FL, USA, 16–20 August 2016; pp. 6307–6310. [Google Scholar]

| Child | Adult | |
|---|---|---|
| tRCC | 5.92 ± 2.40 | 18.85 ± 5.07 |
| tRCCN | 4.90 ± 1.16 | 6.83 ± 1.58 |
| midpos | 3.79 ± 0.71 | 5.40 ± 0.56 |
| Adult | 118 (52.4%) | 2 (0.9%) | 98.3%/1.7% | |
| Output Class | Child | 6 (2.7%) | 99 (44%) | 94.3%/5.7% |
| Total | 95.2%/4.8% | 98%/2% | 96.4%/3.6% | |
| Adult | Child | Total | ||
| Target Class | ||||
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Jovanov, E.; Talukder, B.M.S.B.; Schwebel, D.C.; Evans, W.D. Design and Feasibility of a Safe Pill Bottle. Appl. Syst. Innov. 2018, 1, 13. https://doi.org/10.3390/asi1020013
Jovanov E, Talukder BMSB, Schwebel DC, Evans WD. Design and Feasibility of a Safe Pill Bottle. Applied System Innovation. 2018; 1(2):13. https://doi.org/10.3390/asi1020013
Chicago/Turabian StyleJovanov, Emil, B.M.S. Bahar Talukder, David C. Schwebel, and W. Douglas Evans. 2018. "Design and Feasibility of a Safe Pill Bottle" Applied System Innovation 1, no. 2: 13. https://doi.org/10.3390/asi1020013
APA StyleJovanov, E., Talukder, B. M. S. B., Schwebel, D. C., & Evans, W. D. (2018). Design and Feasibility of a Safe Pill Bottle. Applied System Innovation, 1(2), 13. https://doi.org/10.3390/asi1020013







