A Study of LoRa: Long Range & Low Power Networks for the Internet of Things
Abstract
:1. Introduction
1.1. Related Work
- Low power local area networks with a less than 1000-m range. This category includes IEEE 802.15.4, IEEE P802.1ah, Bluetooth/LE, etc., which are applicable directly in short-range personal area networks, in body area networks or, if organized in a mesh topology, also in larger areas.
- Low-power wide area networks, with a greater than 1000-m range, essentially low-power versions of cellular networks, with each “cell” covering thousands of end-devices. This category includes LoRaWAN, but also protocols, such as Sigfox, DASH7, etc.
1.1.1. IEEE802.15.4
1.1.2. Bluetooth/LE
1.1.3. IEEE 802.11 ah
1.1.4. Sigfox
1.1.5. DASH7
1.2. Statement of Purpose
2. LoRa Overview
2.1. LoRa Protocol Stack
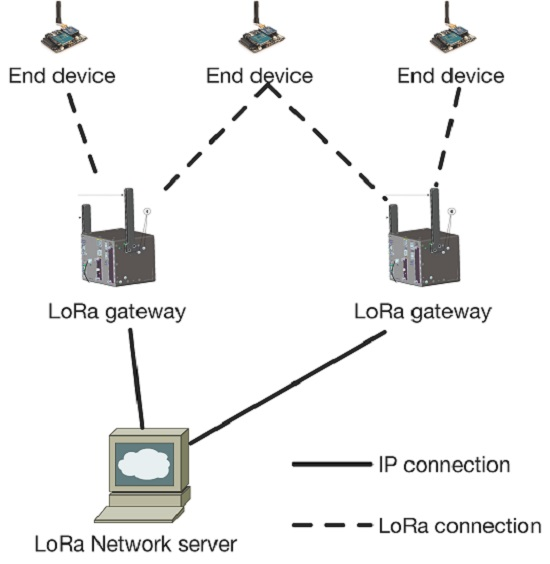
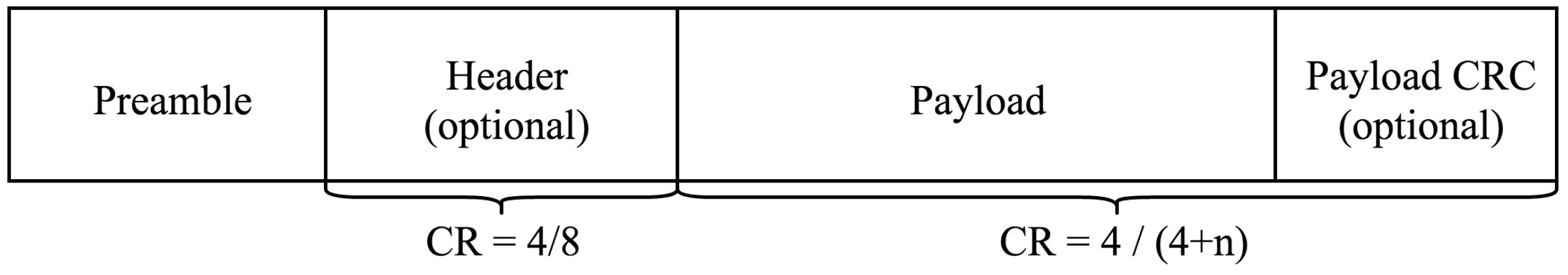
2.2. LoRa Network Architecture
3. The LoRa Physical Layer
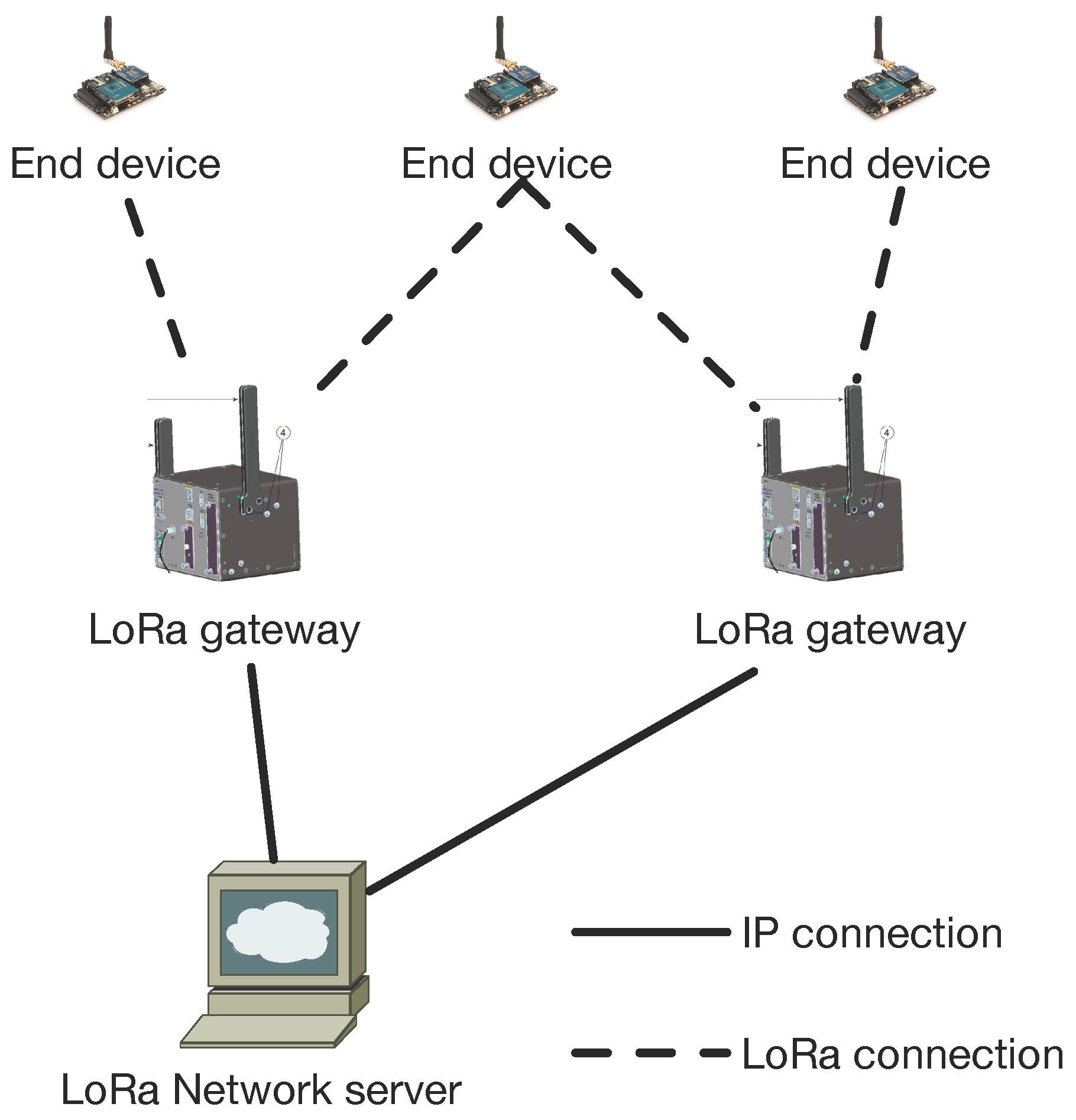
3.1. Overview of the Physical Layer
3.2. Parameters of the Physical Layer
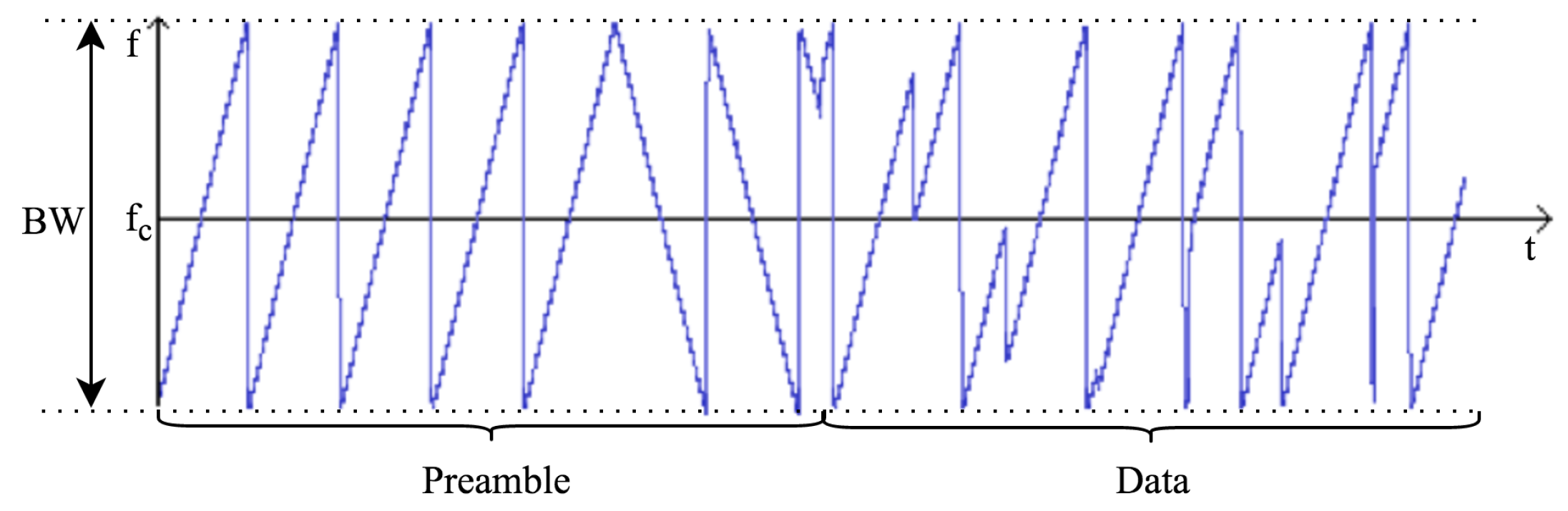
3.3. Physical Frame Format
3.4. Performance Evaluation
3.4.1. Receiver Sensitivity
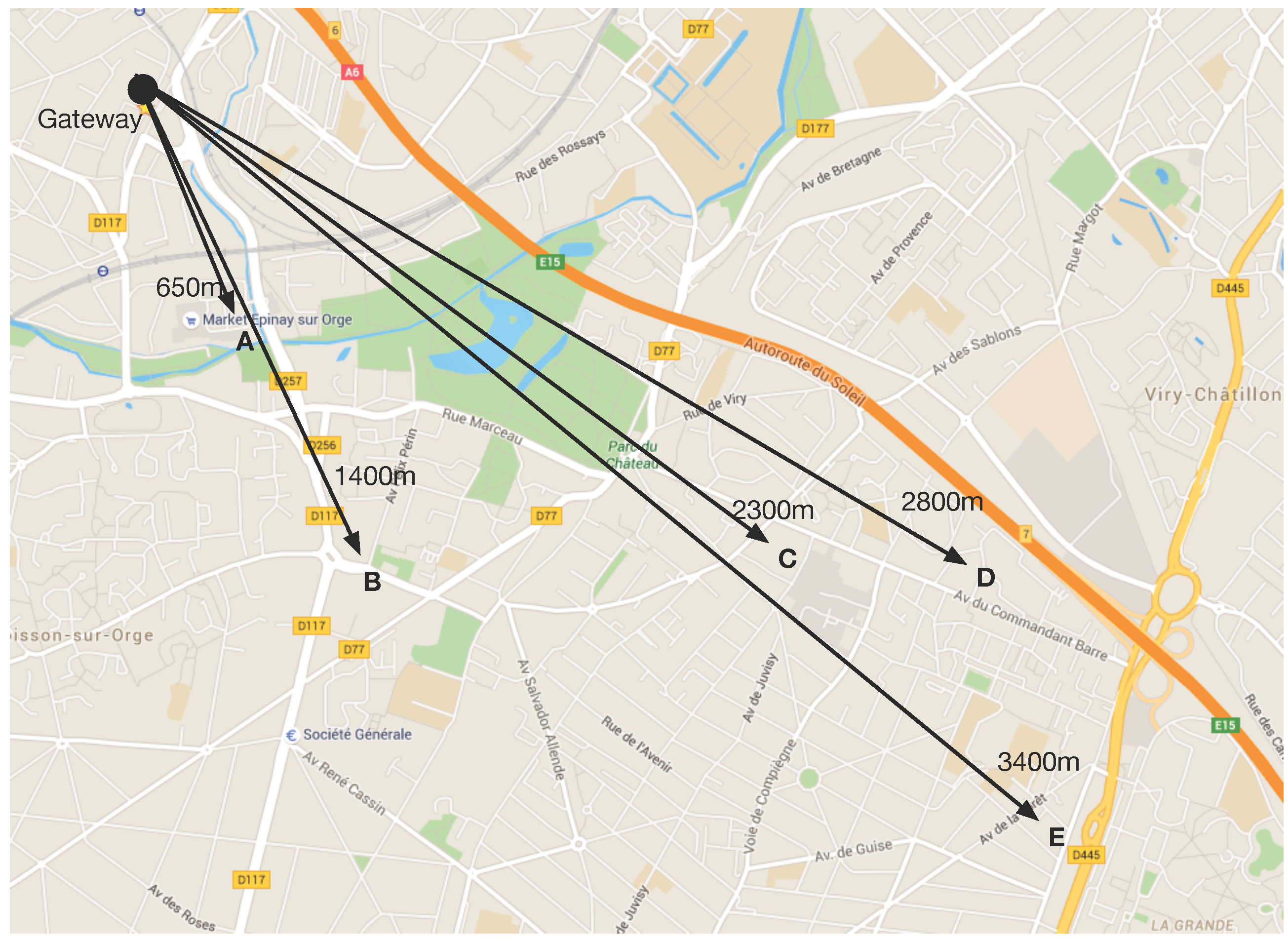
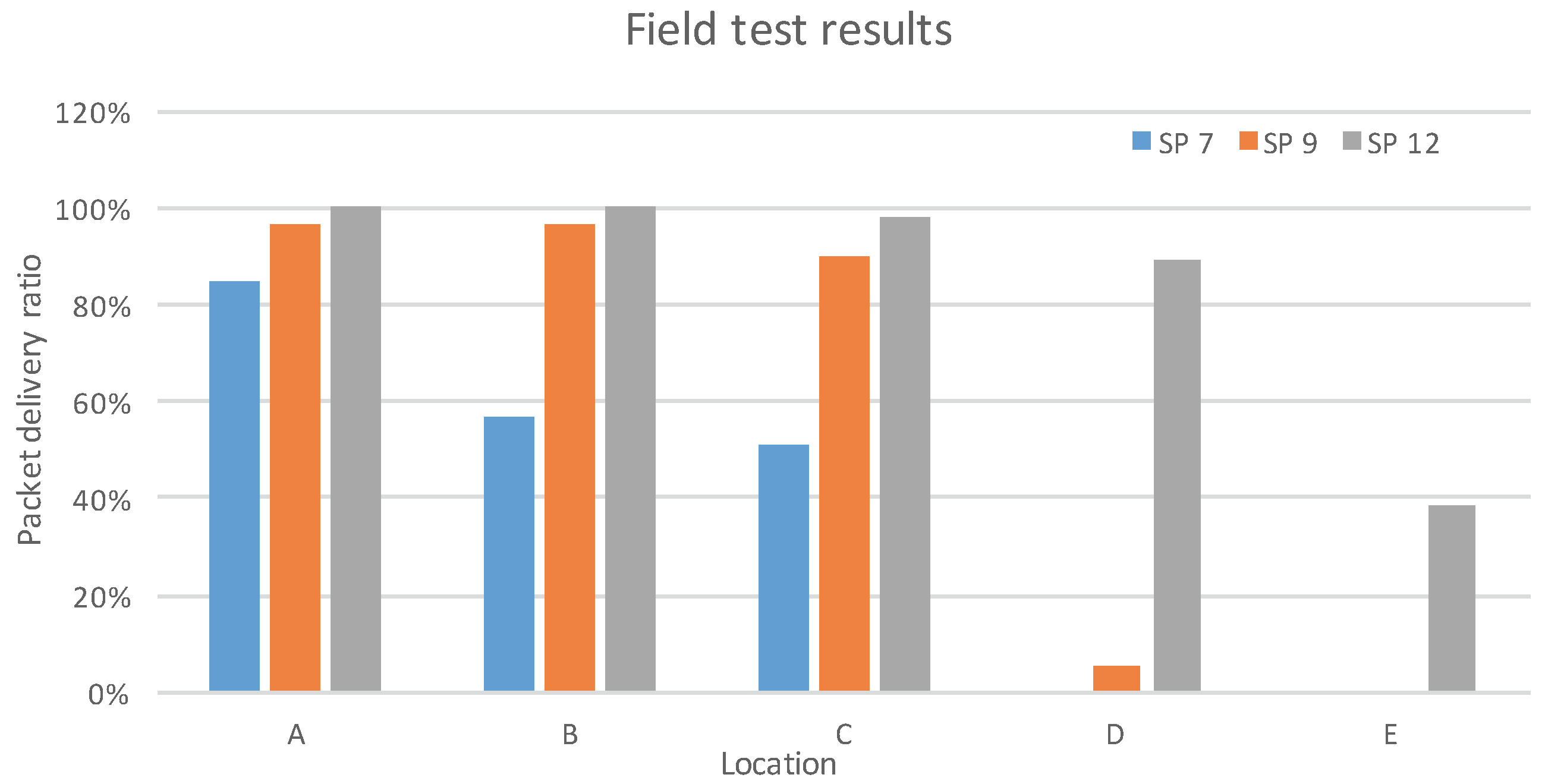
3.4.2. Network Coverage
4. The LoRaWAN Protocol
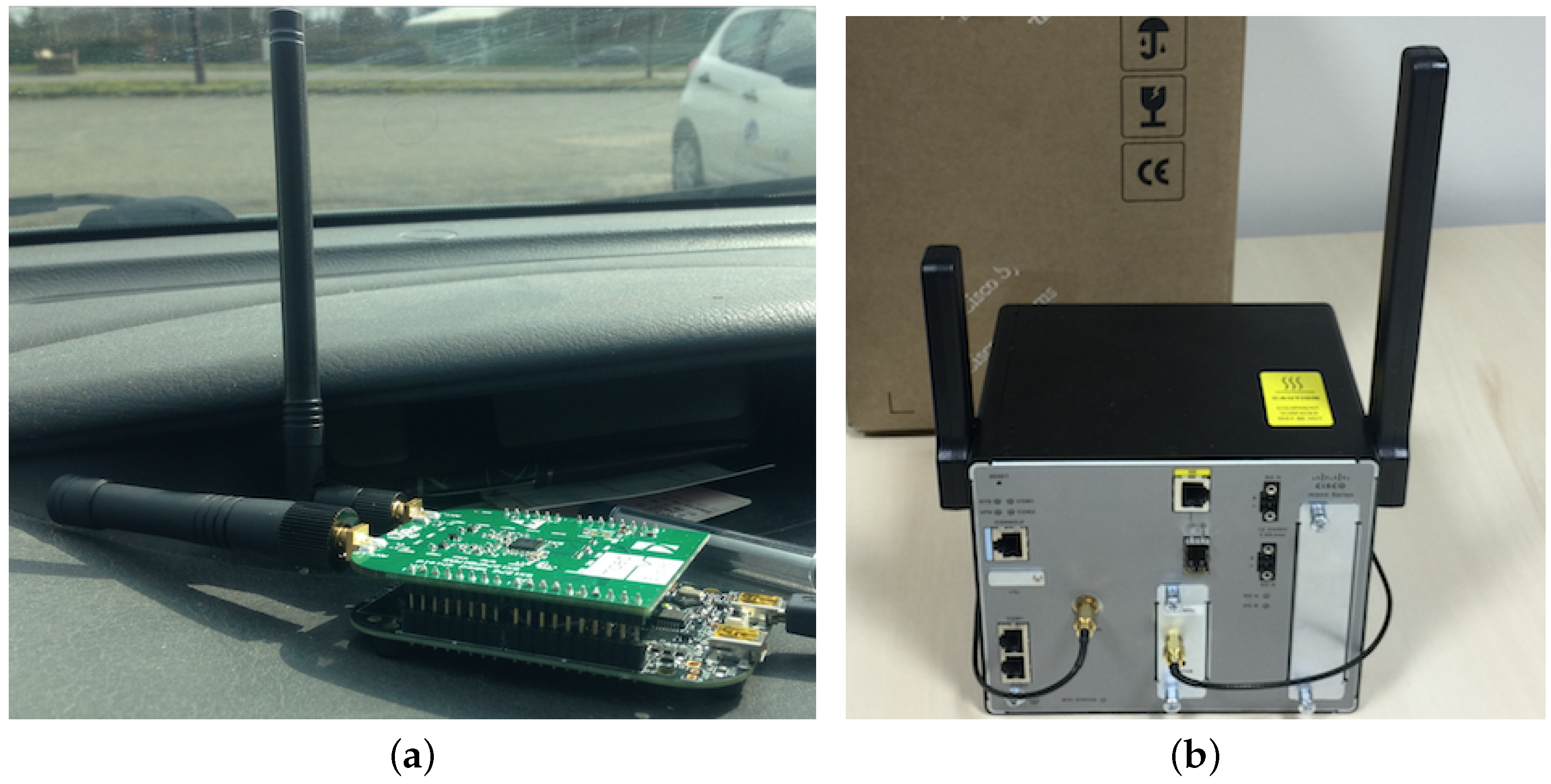
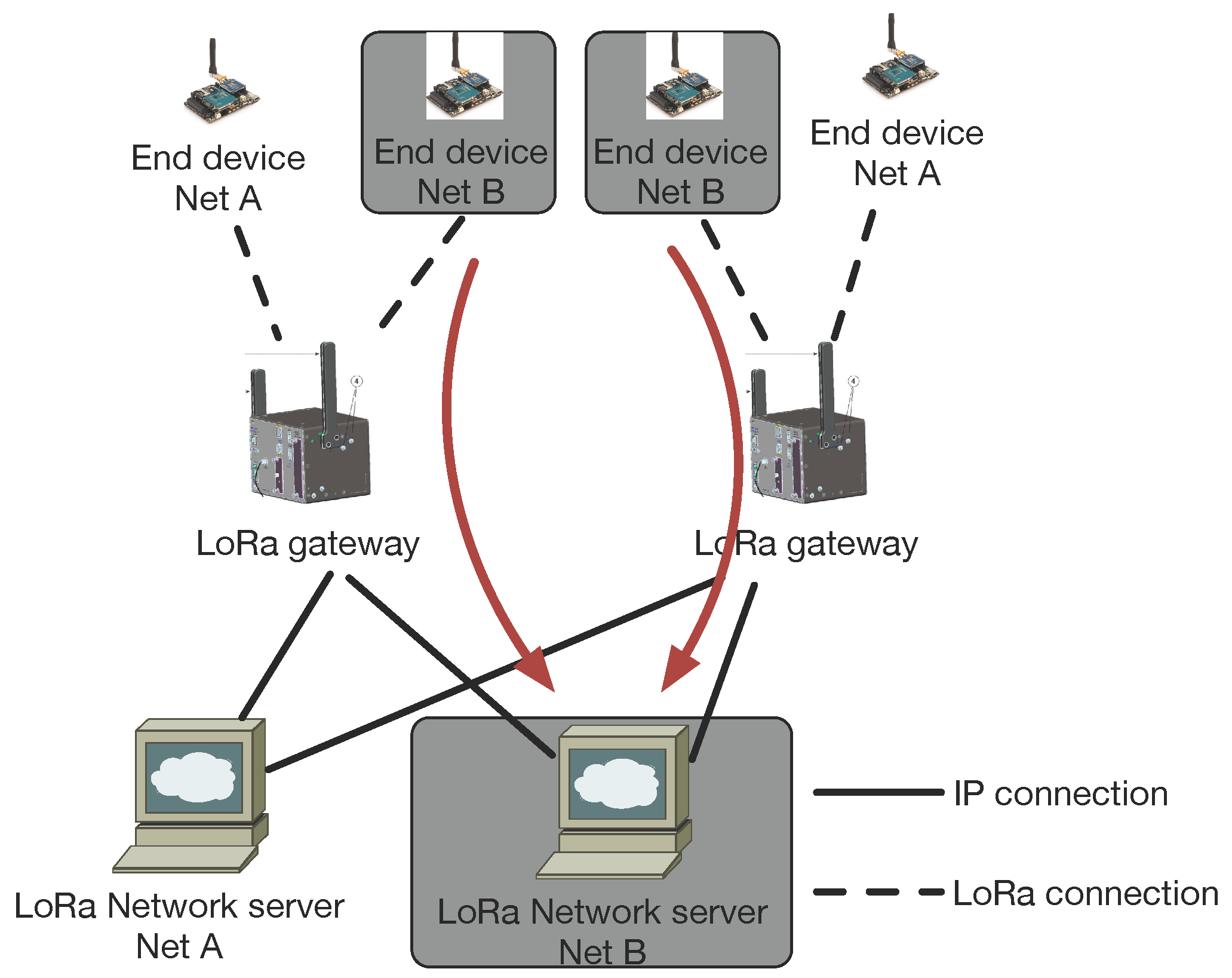
4.1. Components of a LoRaWAN Network
- End-device: the low-power consumption sensors that communicate with gateways using LoRa.
- Gateway: the intermediate devices that forward packets coming from end-devices to a network server over an IP backhaul interface allowing a bigger throughput, such as Ethernet or 3G. There can be multiple gateways in a LoRa deployment, and the same data packet can be received (and forwarded) by more than one gateway.
- Network server: responsible for de-duplicating and decoding the packets sent by the devices and generating the packets that should be sent back to the devices.
- Class A, bi-directional: Class A end-devices can schedule an uplink transmission based on their own needs, with a small jitter (random variation before transmission). This class of devices allows bi-directional communications, whereby each uplink transmission is followed by two short downlink receive windows. Downlink transmission from the server at any other time has to wait until the next uplink transmission occurs. Class A devices have the lowest power consumption, but also offer less flexibility on downlink transmissions.
- Class B, bi-directional with scheduled receive slots: Class B end-devices open extra receive windows at scheduled times. A synchronized beacon from the gateway is thus required, so that the network server is able to know when the end-device is listening.
- Class C, bi-directional with maximal receive slots: Class C end-devices have almost continuous receive windows. They thus have maximum power consumption.
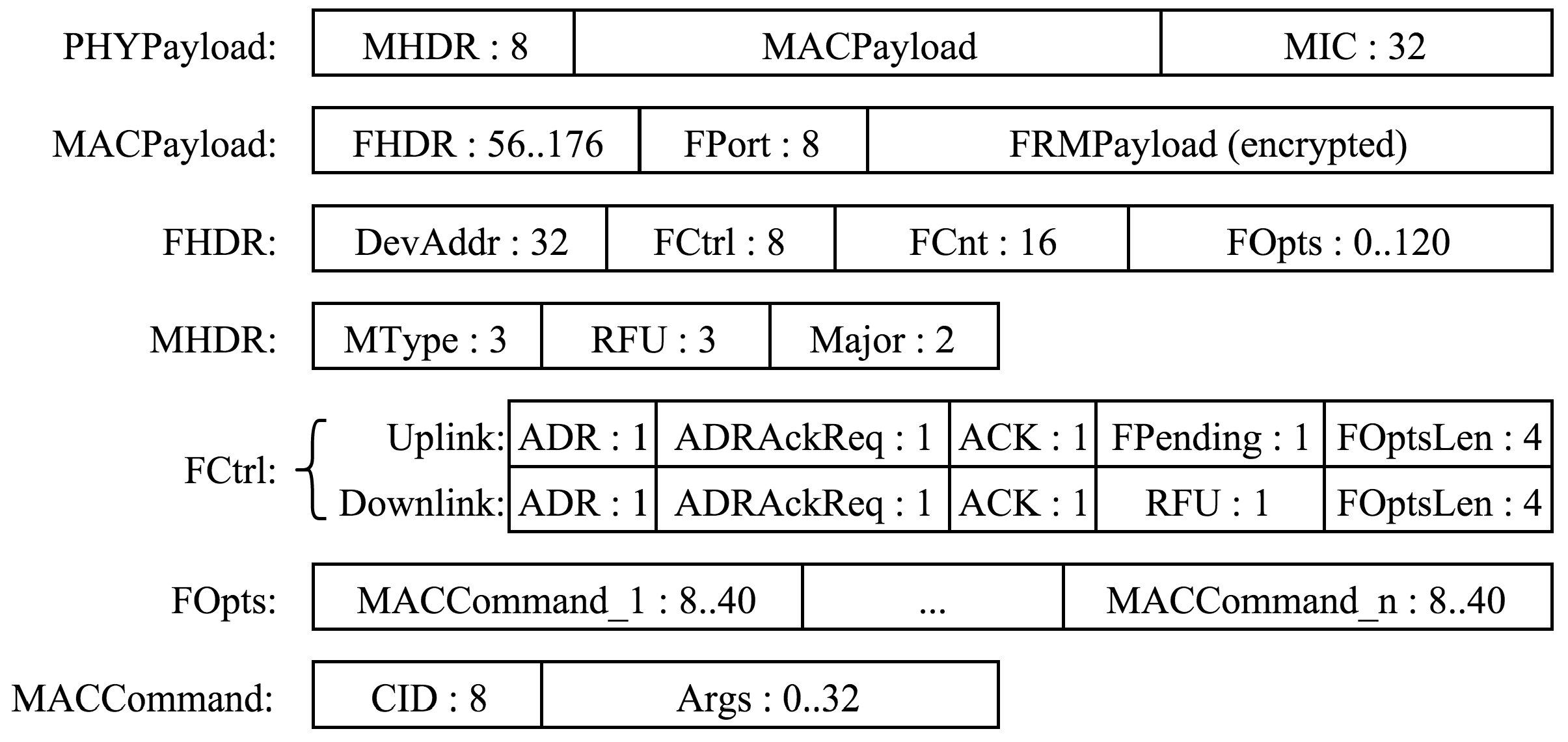
4.2. LoRaWAN Message Format
4.3. End-Device Setup
- End-device address (DevAddr): A 32-bit identifier of the end-device. Seven bits are used as the network identifier, and 25 bits are used as the network address of the end-device.
- Application identifier (AppEUI): A global application ID in the IEEE EUI64 address space that uniquely identifies the owner of the end-device.
- Network session key (NwkSKey): A key used by the network server and the end-device to calculate and verify the message integrity code of all data messages to ensure data integrity.
- Application session key (AppSKey): A key used by the network server and end-device to encrypt and decrypt the payload field of data messages.
4.4. LoRaWAN MAC Commands
5. LoRaWAN Analysis
5.1. Single Device Maximal throughput and MTU
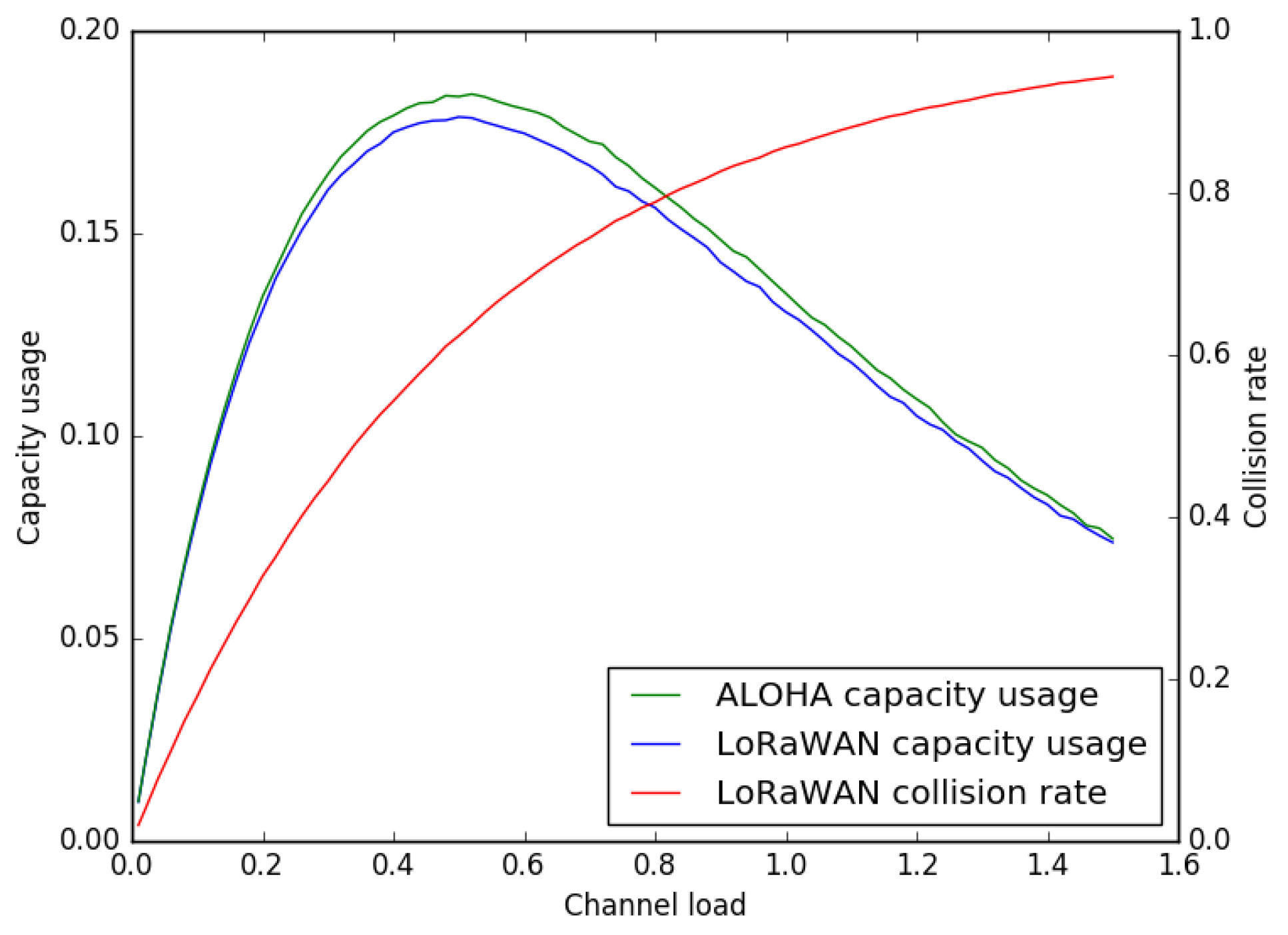
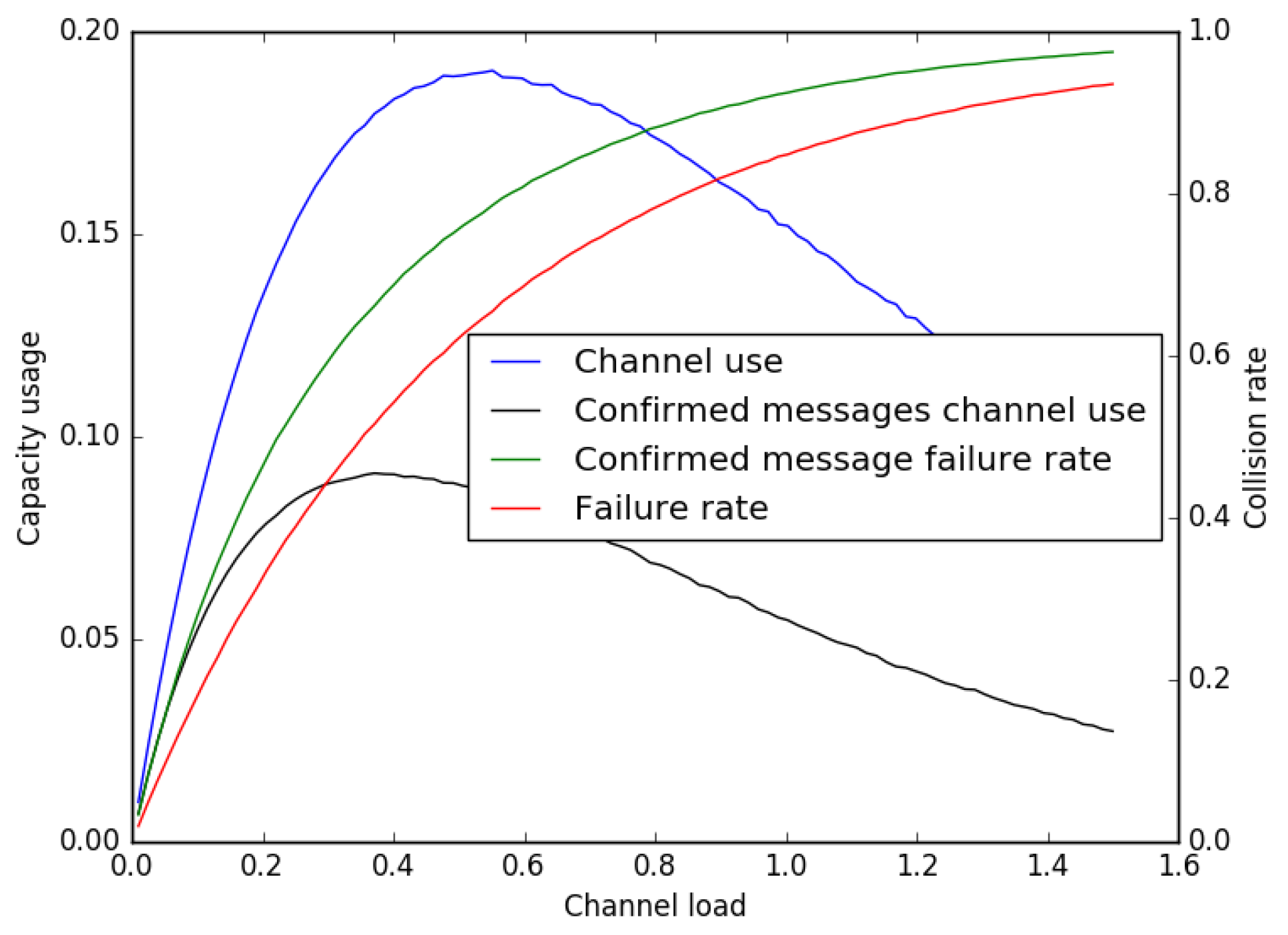
5.2. Total Capacity and Channel Load
5.3. Estimation of the Collision Rate
5.4. The Network Server Role
5.5. The Gateway Role
6. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Gubbi, J.; Buyya, R.; Marusic, S.; Palaniswamia, M. Internet of Things (IoT): A vision, architectural elements, and future directions. Future Gener. Comput. Syst. 2013, 29, 1645–1660. [Google Scholar] [CrossRef]
- Evans, D. The Internet of Things: How the Next Evolution of the Internet is Changing Everything; Cisco Internet Business Solutions Group: San Jose, CA, USA, 2011. [Google Scholar]
- LoRa Alliance. White Paper: A Technical Overview of Lora and Lorawan; The LoRa Alliance: San Ramon, CA, USA, 2015. [Google Scholar]
- IEEE 802 Working Group and Others. IEEE Standard for Local and Metropolitan Area Networks—Part 15.4: Low-Rate Wireless Personal Area Networks (LR-WPANs); IEEE Std 802.15.4-2011: New York, NY, USA, 2012. [Google Scholar]
- Baronti, P.; Pillai, P.; Chook, V.W.; Chessa, S.; Gotta, A.; Hu, Y.F. Wireless sensor networks: A survey on the state of the art and the 802.15. 4 and ZigBee standards. Comput. Commun. 2007, 30, 1655–1695. [Google Scholar] [CrossRef]
- Want, R.; Schilit, B.; Laskowski, D. Bluetooth le finds its niche. IEEE Pervasive Comput. 2013, 12, 12–16. [Google Scholar] [CrossRef]
- Khorov, E.; Lyakhov, A.; Krotov, A.; Guschin, A. A survey on ieee 802.11 ah: An enabling networking technology for smart cities. Comput. Commun. 2015, 58, 53–69. [Google Scholar] [CrossRef]
- Adame, T.; Bel, A.; Bellalta, B.; Barcelo, J.; Oliver, M. IEEE 802.11 ah: the wifi approach for M2M communications. IEEE Wirel. Commun. 2014, 21, 144–152. [Google Scholar] [CrossRef]
- Margelis, G.; Piechocki, R.; Kaleshi, D.; Thomas, P. Low throughput networks for the IoT: Lessons learned from industrial implementations. In Proceedings of the 2015 IEEE 2nd World Forum on Internet of Things (WF-IoT), Milan, Italy, 14–16 december 2015; pp. 181–186.
- Weyn, M.; Ergeerts, G.; Wante, L.; Vercauteren, C.; Hellinckx, P. Survey of the DASH7 alliance protocol for 433 MHz wireless sensor communication. Int. J. Distrib. Sens. Netw. 2013, 9, 870430. [Google Scholar] [CrossRef]
- ISO-IEC. ISO/IEC 18000-7:2014 Information Technology—Radio Frequency Identification for Item Management—Part 7: Parameters for Active Air Interface Communications at 433 MHz; ISO: Geneva, Switherland, 2014. [Google Scholar]
- Guibene, W.; Nolan, K.E.; Kelly, M.Y. Survey on clean slate cellular-iot standard proposals. In Proceedings of the 2015 IEEE International Conference on Computer and Information Technology; Ubiquitous Computing and Communications; Dependable, Autonomic and Secure Computing; Pervasive Intelligence and Computing (CIT/IUCC/DASC/PICOM), Liverpool, UK, 26–28 October 2015; pp. 1596–1599.
- Rathod, N.; Jain, P.; Subramanian, R.; Yawalkar, S.; Sunkenapally, M.; Amrutur, B.; Sundaresan, R. Performance analysis of wireless devices for a campus-wide iot network. In Proceedings of the 2015 13th International Symposium on Modeling and Optimization in Mobile, Ad Hoc, and Wireless Networks (WiOpt), Mumbai, India, 25–29 May 2015; pp. 84–89.
- Centenaro, M.; Vangelista, L.; Zanella, A.; Zorzi, M. Long-Range Communications in Unlicensed Bands: The Rising Stars in the IoT and Smart City Scenarios. 2015. Available online: http://arxiv.org/abs/1510.00620 (accessed on 2 August 2016).
- Petajajarvi, J.; Mikhaylov, K.; Roivainen, A.; Hanninen, T.; Pettissalo, M. On the coverage of lpwans: Range evaluation and channel attenuation model for lora technology. In Proceedings of the 2015 14th International Conference on ITS Telecommunications (ITST), Copenhagen, Denmark, 2–4 December 2015; pp. 55–59.
- Bor, M.; Vidler, J.E.; Roedig, U. Lora for the Internet of Things. In Proceedings of the 2016 International Conference on Embedded Wireless Systems and Networks (EWSN ’16), TU Graz, Austria, 15–17 February 2016; pp. 361–366.
- Berni, A.J.; Gregg, W.D. On the utility of chirp modulation for digital signaling. IEEE Trans. Commun. 1973, 21, 748–751. [Google Scholar] [CrossRef]
- Springer, A.; Gugler, W.; Huemer, M.; Reind, L.; Ruppel, C.; Weigel, R. Spread spectrum communications using chirp signals. In Proceedings of the IEEE/AFCEA Information Systems for Enhanced Public Safety and Security (EUROCOMM 2000), Munich, Germany, 19 May 2000; pp. 166–170.
- LoRa SX1276/77/78/79 Datasheet, Rev. 4. Semtech, 2015. Available online: http://www.semtech.com/images/datasheet/sx1276_77_78_79.pdf (accessed on 8 September 2016).
- LoRa SX1272/73 Datasheet. Semtech, March 2015. Available online: http://www.semtech.com/images/datasheet/sx1272.pdf (accessed on 8 September 2016).
- Sikken, B. Project DecodingLoRa. 2016. Available online: https://revspace.nl/DecodingLora (accessed on 1 August 2016).
- International Telecommunication Union. P-Series Recommendations Radiowave Progapatin. Available online: https://www.itu.int/rec/R-REC-P (accessed on 1 August 2016).
- LoRaWAN Specification V1.0. LoRa Alliance, 2015. Available online: https://www.lora-alliance.org/portals/0/specs/LoRaWAN%20Specification%201R0.pdf (accessed on 1 August 2016).
- Abramson, N. The Aloha System: Final Technical Report; Hawaii University: Honolulu, HI, USA, 1974. [Google Scholar]
- Oliver, M.; Escudero, A. Study of Different CSMA/CA IEEE 802.11-Based Implementations. Available online: http://www.eunice-forum.org/eunice99/027.pdf (accessed on 8 September 2016).


| SF | 7 | 8 | 9 | 10 | 11 | 12 | |
|---|---|---|---|---|---|---|---|
| BW | |||||||
| 125 kHz | −123 | −126 | −129 | −132 | −133 | −136 | |
| 250 kHz | −120 | −123 | −125 | −128 | −130 | −133 | |
| 500 kHz | −116 | −119 | −122 | −125 | −128 | −130 | |
© 2016 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC-BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Augustin, A.; Yi, J.; Clausen, T.; Townsley, W.M. A Study of LoRa: Long Range & Low Power Networks for the Internet of Things. Sensors 2016, 16, 1466. https://doi.org/10.3390/s16091466
Augustin A, Yi J, Clausen T, Townsley WM. A Study of LoRa: Long Range & Low Power Networks for the Internet of Things. Sensors. 2016; 16(9):1466. https://doi.org/10.3390/s16091466
Chicago/Turabian StyleAugustin, Aloÿs, Jiazi Yi, Thomas Clausen, and William Mark Townsley. 2016. "A Study of LoRa: Long Range & Low Power Networks for the Internet of Things" Sensors 16, no. 9: 1466. https://doi.org/10.3390/s16091466
APA StyleAugustin, A., Yi, J., Clausen, T., & Townsley, W. M. (2016). A Study of LoRa: Long Range & Low Power Networks for the Internet of Things. Sensors, 16(9), 1466. https://doi.org/10.3390/s16091466