Broadcast Authentication for Wireless Sensor Networks Using Nested Hashing and the Chinese Remainder Theorem
Abstract
:1. Introduction
2. Related Work
2.1. Lamport’s Scheme
2.2. Bicakci et al.’s Scheme
2.3. Chinese Remainder Theorem (CRT)
2.4. TESLA Family Broadcast Authentication
2.5. CRTBA Broadcast Authentication
3. Required Attributes
3.1. Data Integrity
3.2. Data Origin Authentication
3.3. Freshness
3.4. Delay Tolerance
3.5. Confidentiality
3.6. Denial-of-Service Attack
3.7. Small Challenge Attack
3.8. Limitation for an N times Authentications
4. Our Approach
4.1. Key Pre-loading Phase
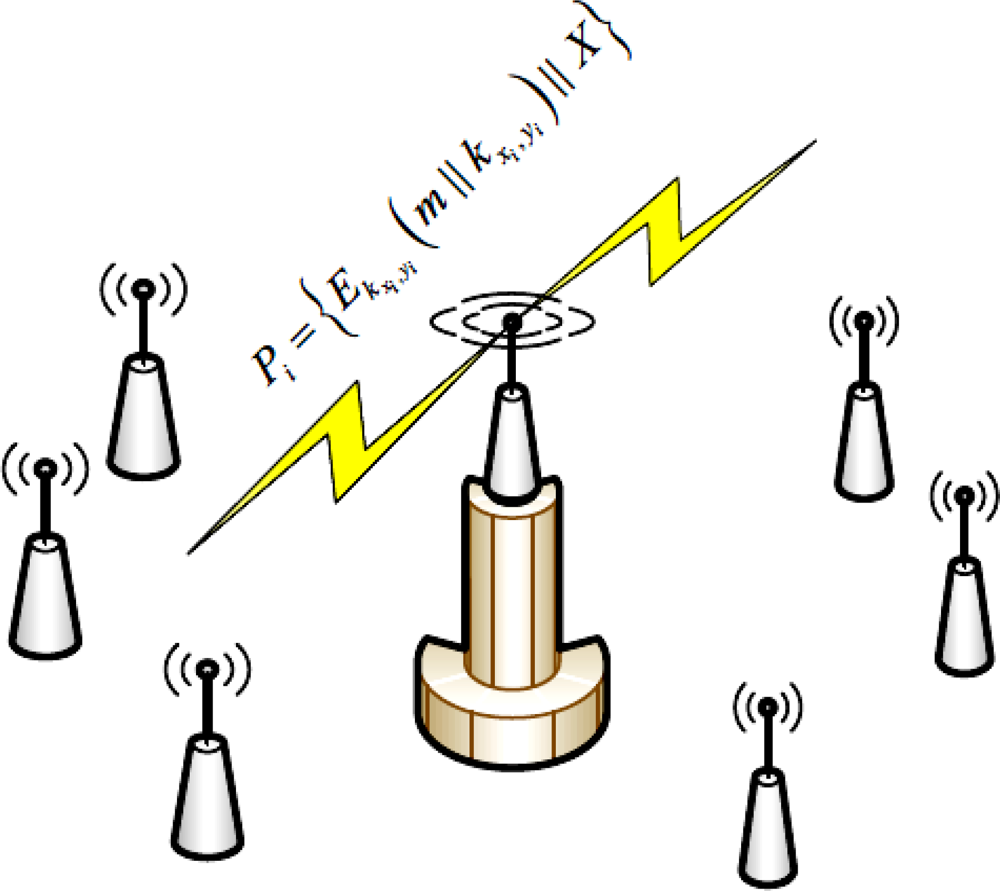
4.2. Message Authentication
- Calculate the session key for the i-th authentication.
- Encrypt the broadcasted message m concatenated with the session key kxi, yi with the session key to get U = Ekxi,yi (m‖kxi,yi)
- Calculate the broadcasted chain indexes, X, for the all N nodes considering the CRT
4.3. Authentication Verification
- Each sensor node will extract X to perform the module operation to obtain the chain indexes, e.g., n1 will get and .
- After getting the chain indexes, they will perform the key generation according to these indexes by using the two different hash functions to get this .
- By decrypting Dkxi,yi (U), sensors will be able to get the message m and the session key kxi,yi.
- Then the sensor nodes need to compare the two sessions they have established and received, if the comparison is positive, then sensor nodes will recover the message. Otherwise the received broadcast message has been altered. The message integrity also checked implicitly through the authentication verification, that way tampering with U in a way of message modification will sequentially affect the received session key.
- After the completion of one session, sensor nodes and BS have to update the current seed to the next one:
5. Performance Analysis
5.1. Storage Analysis
5.2. Computation Analysis
6. Security Analysis
6.1. Data Integrity
6.2. Data Origin Authentication
6.3. Freshness
6.4. Delay Tolerance
6.5. Confidentiality
6.6. Denial of Service Attacks
6.7. Limitation for an N times Authentications
6.8. Small Challenge Attack
6.9. Brute Force Attack
7. Conclusions
References
- Fan, Y; Chen, IR; Eltoweissy, M. On Optimal Key Disclosure Interval for μTESLA: Analysis of Authentication Delay Versus Network Cost. Proceedings of International Conference on Wireless Networks, Communications and Mobile Computing, Hawaii, HI, USA, 13–16 June 2005; 13, pp. 304–309.
- Shi, E; Perrig, A. Designing Secure Sensor Networks. IEEE Wirel. Commun 2004, 11, 38–43. [Google Scholar]
- Perrig, A; Canetti, R; Tygar, J; Song, D. The TESLA Broadcast Authentication Protocol. CrytoBytes 2002, 5, 2–13. [Google Scholar]
- Liu, D; Ning, P. Efficient Distribution Key Chain Commitments for Broadcast Authentication in Distributed Sensor Networks. Proceedings of the 10th Annual Network and Distributed System Security Symposium, San Diego, CA, USA, 6–7 February 2003; 2, pp. 263–276.
- Liu, D; Ning, P. Multi-level μTESLA: Broadcast Authentication for Distributed Sensor Networks. ACM Trans. Embed. Comput. Syst 2004, 3, 800–836. [Google Scholar]
- Liu, D; Ning, P; Zhu, S; Jajodia, S. Practical broadcast authentication in sensor networks. Proceedings of Annual International Conference on Mobile and Ubiquitous Systems: Networking and Services, San Diego, CA, USA, 17–21 July 2005; pp. 118–129.
- Hu, Y; Perrig, A; Honson, D. Packet Leashes. A Defense against Wormhole Attacks in Wireless Ad hoc Networks. Proceedings of INFOCOM, San Francisco, CA, USA, 30 March–3 April 2003.
- Lamport, L. Password Authentication with Insecure Communication. Comm. ACM 1981, 24, 770–772. [Google Scholar]
- Chefranov, A. One-Time Password Authentication with Infinite Hash Chains. In Novel Algorithms and Techniques in Tele-communications, Automation and Industrial Electronics; Springer: New York, NY, USA, 2008; pp. 283–286. [Google Scholar]
- Bicakci, K; Baykal, N. Infinite Length Hash Chains and Their Applications. Proceedings of 11th IEEE International Workshops on Enabling Technologies: Infrastructure for Collaborating Enterprises, Pittsburgh, PA, USA, 10–12 June 2002; pp. 57–61.
- Rivest, R; Shamir, A; Adleman, L. A Method for Obtaining Digital Signatures and Public-Key Cryptosystems. Comm. ACM 1978, 21, 120–126. [Google Scholar]
- Khan, MK; Alghathbar, K. Cryptanalysis and Security Improvements of “Two-Factor User Authentication in Wireless Sensor Networks”. Sensors 2010, 10, 2450–2459. [Google Scholar]
- Zhang, J; Yu, W; Liu, X. CRTBA: Chinese Remainder Theorem-Based Broadcast Authentication in Wireless Sensor Networks. Proceedings of Computer Network and Multimedia Technology, Wuhan, China, 18–20 January 2009.
- Eldefrawy, M; Khan, MK; Alghathbar, K. A Key Agreement Algorithm with Rekeying for Wireless Sensor Networks Using Public Key Cryptography. Proceedings of International Conference on Anti-counterfeiting, Security, and Identification (ASID), Chengdu, China, 18–20 July 2010.
- Venugopalan, R; Ganesan, P; Peddabachagari, P; Dean, A; Mueller, F; Sichitiu, M. Encryption Overhead in Embedded Systems and Sensor Network Nodes: Modeling and Analysis. Proceedings of International Conference on Compilers, Architecture and Synthesis for Embedded Systems, San Jose, CA, USA, 30 October–1 November 2003.
- Khan, MK; Zhang, J. Improving the Security of “A Flexible Biometrics Remote User Authentication Scheme”. In Computer Standards and Interfaces; Elsevier Science: North Holland, The Netherlands, 2007; Volume 29, pp. 84–87. [Google Scholar]
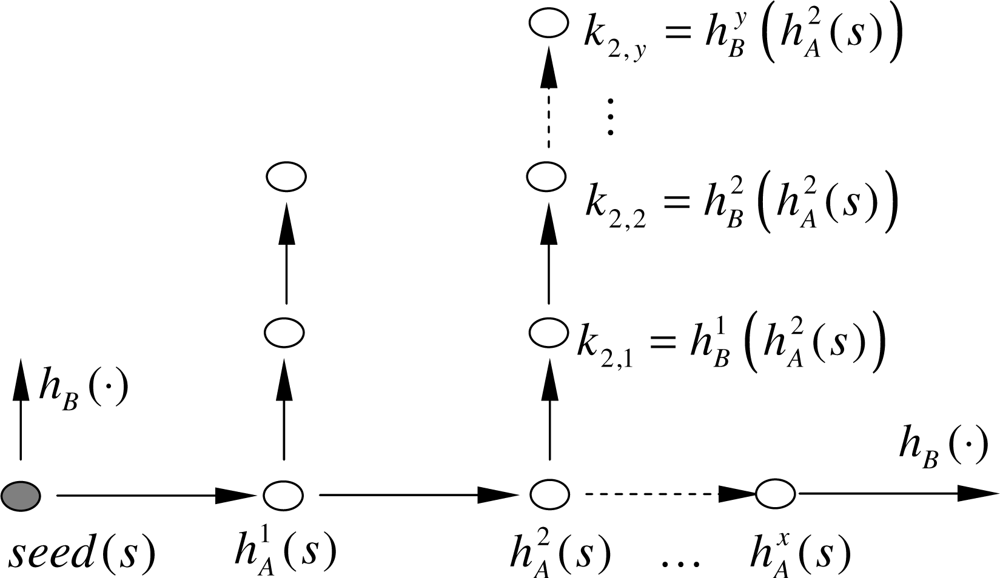
| Notation | Description |
|---|---|
| hA (·) | Represents the first hash function |
| hB (·) | Represents the second hash function |
| (xi, yi) | The nested hashing progress values for i-th authentication |
| Hashing the seed by hA (·) for xi times followed by hB (·) hashing for yi times for the i-th session | |
| kxi, yi | Session key for the i-th authentication |
| U | The encryption of the concatenated message with the session by the session key |
| Pi | The podcasted packet for the i-th authentication |
| X | The broadcasted chain indexes, calculated by the CRT |
| Scrt | The current seed |
| Snxt | The next seed |
| Algorithm | Size | Atmega103 | Atmega128 | M16C/10 | StrongARM | Xscale(400) | Xscale(200) | Sparc(440) |
|---|---|---|---|---|---|---|---|---|
| MD5 | 0 | 5,863 | 1,466 | 1,083 | 46 | 26 | 53 | 23 |
| 1:26 | 5,890 | 1,473 | 1,075 | 46 | 26 | 53 | 23 | |
| 62:80 | 10,888 | 2,722 | 2,011 | 74 | 45 | 90 | 39 | |
| SHA-1 | 1 | 15,249 | 3,812 | 2,651 | 69 | 51 | 102 | 27 |
| 3 | 15,781 | 3,945 | 5,303 | 69 | 50 | 103 | 27 | |
| 65 | 14543 | 3636 | 7955 | 133 | 102 | 205 | 55 | |
| 64 | 31,107 | 7,777 | 10,907 | 145 | 103 | 207 | 56 |
© 2010 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution license (http://creativecommons.org/licenses/by/3.0/).
Share and Cite
Eldefrawy, M.H.; Khan, M.K.; Alghathbar, K.; Cho, E.-S. Broadcast Authentication for Wireless Sensor Networks Using Nested Hashing and the Chinese Remainder Theorem. Sensors 2010, 10, 8683-8695. https://doi.org/10.3390/s100908683
Eldefrawy MH, Khan MK, Alghathbar K, Cho E-S. Broadcast Authentication for Wireless Sensor Networks Using Nested Hashing and the Chinese Remainder Theorem. Sensors. 2010; 10(9):8683-8695. https://doi.org/10.3390/s100908683
Chicago/Turabian StyleEldefrawy, Mohamed Hamdy, Muhammad Khurram Khan, Khaled Alghathbar, and Eun-Suk Cho. 2010. "Broadcast Authentication for Wireless Sensor Networks Using Nested Hashing and the Chinese Remainder Theorem" Sensors 10, no. 9: 8683-8695. https://doi.org/10.3390/s100908683
APA StyleEldefrawy, M. H., Khan, M. K., Alghathbar, K., & Cho, E.-S. (2010). Broadcast Authentication for Wireless Sensor Networks Using Nested Hashing and the Chinese Remainder Theorem. Sensors, 10(9), 8683-8695. https://doi.org/10.3390/s100908683




