Journal Description
Algorithms
Algorithms
is a peer-reviewed, open access journal which provides an advanced forum for studies related to algorithms and their applications. Algorithms is published monthly online by MDPI. The European Society for Fuzzy Logic and Technology (EUSFLAT) is affiliated with Algorithms and their members receive discounts on the article processing charges.
- Open Access — free for readers, with article processing charges (APC) paid by authors or their institutions.
- High Visibility: indexed within Scopus, ESCI (Web of Science), Ei Compendex, and other databases.
- Journal Rank: CiteScore - Q2 (Numerical Analysis)
- Rapid Publication: manuscripts are peer-reviewed and a first decision is provided to authors approximately 15 days after submission; acceptance to publication is undertaken in 2.9 days (median values for papers published in this journal in the second half of 2023).
- Testimonials: See what our editors and authors say about Algorithms.
- Recognition of Reviewers: reviewers who provide timely, thorough peer-review reports receive vouchers entitling them to a discount on the APC of their next publication in any MDPI journal, in appreciation of the work done.
Impact Factor:
2.3 (2022);
5-Year Impact Factor:
2.2 (2022)
Latest Articles
Anomaly Detection in Blockchain Networks Using Unsupervised Learning: A Survey
Algorithms 2024, 17(5), 201; https://doi.org/10.3390/a17050201 - 9 May 2024
Abstract
In decentralized systems, the quest for heightened security and integrity within blockchain networks becomes an issue. This survey investigates anomaly detection techniques in blockchain ecosystems through the lens of unsupervised learning, delving into the intricacies and going through the complex tapestry of abnormal
[...] Read more.
In decentralized systems, the quest for heightened security and integrity within blockchain networks becomes an issue. This survey investigates anomaly detection techniques in blockchain ecosystems through the lens of unsupervised learning, delving into the intricacies and going through the complex tapestry of abnormal behaviors by examining avant-garde algorithms to discern deviations from normal patterns. By seamlessly blending technological acumen with a discerning gaze, this survey offers a perspective on the symbiotic relationship between unsupervised learning and anomaly detection by reviewing this problem with a categorization of algorithms that are applied to a variety of problems in this field. We propose that the use of unsupervised algorithms in blockchain anomaly detection should be viewed not only as an implementation procedure but also as an integration procedure, where the merits of these algorithms can effectively be combined in ways determined by the problem at hand. In that sense, the main contribution of this paper is a thorough study of the interplay between various unsupervised learning algorithms and how this can be used in facing malicious activities and behaviors within public and private blockchain networks. The result is the definition of three categories, the characteristics of which are recognized in terms of the way the respective integration takes place. When implementing unsupervised learning, the structure of the data plays a pivotal role. Therefore, this paper also provides an in-depth presentation of the data structures commonly used in unsupervised learning-based blockchain anomaly detection. The above analysis is encircled by a presentation of the typical anomalies that have occurred so far along with a description of the general machine learning frameworks developed to deal with them. Finally, the paper spotlights challenges and directions that can serve as a comprehensive compendium for future research efforts.
Full article
(This article belongs to the Special Issue Deep Learning for Anomaly Detection)
Open AccessArticle
A Sim-Learnheuristic for the Team Orienteering Problem: Applications to Unmanned Aerial Vehicles
by
Mohammad Peyman, Xabier A. Martin, Javier Panadero and Angel A. Juan
Algorithms 2024, 17(5), 200; https://doi.org/10.3390/a17050200 - 8 May 2024
Abstract
In this paper, we introduce a novel sim-learnheuristic method designed to address the team orienteering problem (TOP) with a particular focus on its application in the context of unmanned aerial vehicles (UAVs). Unlike most prior research, which primarily focuses on the deterministic and
[...] Read more.
In this paper, we introduce a novel sim-learnheuristic method designed to address the team orienteering problem (TOP) with a particular focus on its application in the context of unmanned aerial vehicles (UAVs). Unlike most prior research, which primarily focuses on the deterministic and stochastic versions of the TOP, our approach considers a hybrid scenario, which combines deterministic, stochastic, and dynamic characteristics. The TOP involves visiting a set of customers using a team of vehicles to maximize the total collected reward. However, this hybrid version becomes notably complex due to the presence of uncertain travel times with dynamically changing factors. Some travel times are stochastic, while others are subject to dynamic factors such as weather conditions and traffic congestion. Our novel approach combines a savings-based heuristic algorithm, Monte Carlo simulations, and a multiple regression model. This integration incorporates the stochastic and dynamic nature of travel times, considering various dynamic conditions, and generates high-quality solutions in short computational times for the presented problem.
Full article
(This article belongs to the Special Issue Heuristic Optimization Algorithms for Logistics)
►▼
Show Figures

Figure 1
Open AccessArticle
MVACLNet: A Multimodal Virtual Augmentation Contrastive Learning Network for Rumor Detection
by
Xin Liu, Mingjiang Pang, Qiang Li, Jiehan Zhou, Haiwen Wang and Dawei Yang
Algorithms 2024, 17(5), 199; https://doi.org/10.3390/a17050199 - 8 May 2024
Abstract
In today’s digital era, rumors spreading on social media threaten societal stability and individuals’ daily lives, especially multimodal rumors. Hence, there is an urgent need for effective multimodal rumor detection methods. However, existing approaches often overlook the insufficient diversity of multimodal samples in
[...] Read more.
In today’s digital era, rumors spreading on social media threaten societal stability and individuals’ daily lives, especially multimodal rumors. Hence, there is an urgent need for effective multimodal rumor detection methods. However, existing approaches often overlook the insufficient diversity of multimodal samples in feature space and hidden similarities and differences among multimodal samples. To address such challenges, we propose MVACLNet, a Multimodal Virtual Augmentation Contrastive Learning Network. In MVACLNet, we first design a Hierarchical Textual Feature Extraction (HTFE) module to extract comprehensive textual features from multiple perspectives. Then, we fuse the textual and visual features using a modified cross-attention mechanism, which operates from different perspectives at the feature value level, to obtain authentic multimodal feature representations. Following this, we devise a Virtual Augmentation Contrastive Learning (VACL) module as an auxiliary training module. It leverages ground-truth labels and extra-generated virtual multimodal feature representations to enhance contrastive learning, thus helping capture more crucial similarities and differences among multimodal samples. Meanwhile, it performs a Kullback–Leibler (KL) divergence constraint between predicted probability distributions of the virtual multimodal feature representations and their corresponding virtual labels to help extract more content-invariant multimodal features. Finally, the authentic multimodal feature representations are input into a rumor classifier for detection. Experiments on two real-world datasets demonstrate the effectiveness and superiority of MVACLNet on multimodal rumor detection.
Full article
(This article belongs to the Special Issue Algorithms in Data Classification (2nd Edition))
►▼
Show Figures

Figure 1
Open AccessArticle
Three Cube Packing for All Dimensions
by
Peter Adamko
Algorithms 2024, 17(5), 198; https://doi.org/10.3390/a17050198 - 8 May 2024
Abstract
Let
Let
(This article belongs to the Special Issue Mathematical Modelling in Engineering and Human Behaviour (2nd Edition))
►▼
Show Figures

Figure 1
Open AccessArticle
Intelligent Ship Scheduling and Path Planning Method for Maritime Emergency Rescue
by
Wen Ying, Zhaohui Wang, Hui Li, Sheng Du and Man Zhao
Algorithms 2024, 17(5), 197; https://doi.org/10.3390/a17050197 - 8 May 2024
Abstract
Intelligent ship navigation scheduling and planning is of great significance for ensuring the safety of maritime production and life and promoting the development of the marine economy. In this paper, an intelligent ship scheduling and path planning method is proposed for a practical
[...] Read more.
Intelligent ship navigation scheduling and planning is of great significance for ensuring the safety of maritime production and life and promoting the development of the marine economy. In this paper, an intelligent ship scheduling and path planning method is proposed for a practical application scenario wherein the emergency rescue center receives rescue messages and dispatches emergency rescue ships to the incident area for rescue. Firstly, the large-scale sailing route of the task ship is pre-planned in the voyage planning stage by using the improved A* algorithm. Secondly, the full-coverage path planning algorithm is used to plan the ship’s search route in the regional search stage by updating the ship’s navigation route in real time. In order to verify the effectiveness of the proposed algorithm, comparative experiments were carried out with the conventional algorithm in the two operation stages of rushing to the incident sea area and regional search and rescue. The experimental results show that the proposed algorithm can adapt to emergency search and rescue tasks in the complex setting of the sea area and can effectively improve the efficiency of the operation, ensure the safety of the operation process, and provide a more intelligent and efficient solution for the planning of maritime emergency rescue tasks.
Full article
(This article belongs to the Special Issue Data-Driven Intelligent Modeling and Optimization Algorithms for Industrial Processes)
►▼
Show Figures
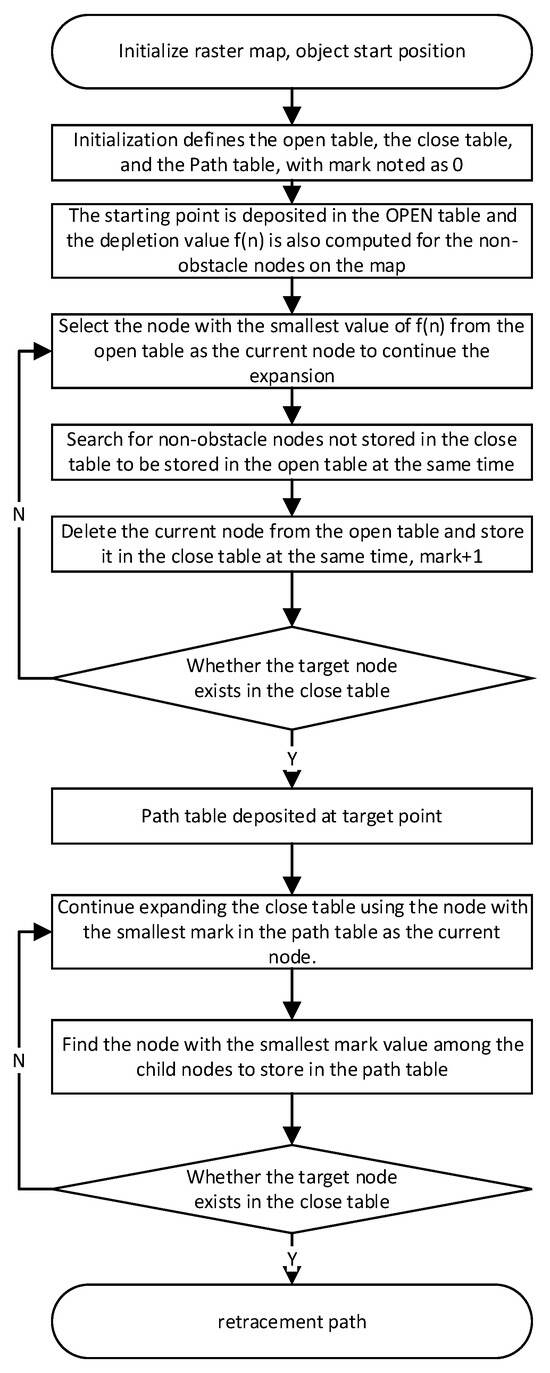
Figure 1
Open AccessArticle
Performance-Constraint Fault Tolerant Control to Aircraft in Presence of Actuator Deviation
by
Peng Tang, Chuangxin Zhao, Shizhe Liang and Yuehong Dai
Algorithms 2024, 17(5), 196; https://doi.org/10.3390/a17050196 - 7 May 2024
Abstract
►▼
Show Figures
Accuracy of electro-mechanical actuator in aircraft is susceptible to variable operation conditions such as electromagnetic interference, changeable temperature or loss of maintenance, leading in turn to flight performance degradation. This paper proposed an unified control paradigm that aims to keep aircraft’s velocity in
[...] Read more.
Accuracy of electro-mechanical actuator in aircraft is susceptible to variable operation conditions such as electromagnetic interference, changeable temperature or loss of maintenance, leading in turn to flight performance degradation. This paper proposed an unified control paradigm that aims to keep aircraft’s velocity in a safe boundary and shorten the system stabilizing time in presence of actuator deviation. The controller is derived following a practical finite-time-convergence (FTC) with extended dynamics, and an integrated state-constraint structure so as to restrict air vehicle’s attitude rate or translation velocity. It is proved that the system state converges to a sphere near the origin in a finite time, the state trajectory is always remain within the prescribed range, and all signals of the closed-loop system are uniformly ultimately bounded. Compared simulation with the quadratic Lyapunov-based FTC method and an asymptotic convergence controller are conducted on an unmanned helicopter prototype. Results show that the proposed controller enhances the dynamic and fault-tolerant performance of resisting actuator fluctuation.
Full article

Figure 1
Open AccessArticle
An Enhanced Particle Swarm Optimization (PSO) Algorithm Employing Quasi-Random Numbers
by
Shiva Kumar Kannan and Urmila Diwekar
Algorithms 2024, 17(5), 195; https://doi.org/10.3390/a17050195 - 6 May 2024
Abstract
This paper introduces an innovative Particle Swarm Optimization (PSO) Algorithm incorporating Sobol and Halton random number samplings. It evaluates the enhanced PSO’s performance against conventional PSO employing Monte Carlo random number samplings. The comparison involves assessing the algorithms across nine benchmark problems and
[...] Read more.
This paper introduces an innovative Particle Swarm Optimization (PSO) Algorithm incorporating Sobol and Halton random number samplings. It evaluates the enhanced PSO’s performance against conventional PSO employing Monte Carlo random number samplings. The comparison involves assessing the algorithms across nine benchmark problems and the renowned Travelling Salesman Problem (TSP). The results reveal consistent enhancements achieved by the enhanced PSO utilizing Sobol/Halton samplings across the benchmark problems. Particularly noteworthy are the Sobol-based PSO improvements in iterations and the computational times for the benchmark problems. These findings underscore the efficacy of employing Sobol and Halton random number generation methods to enhance algorithm efficiency.
Full article
(This article belongs to the Special Issue Metaheuristic Algorithms in Optimal Design of Engineering Problems)
►▼
Show Figures
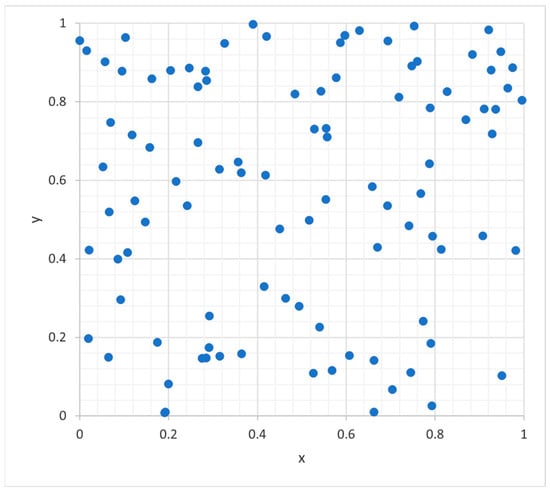
Figure 1
Open AccessArticle
The Weighted Least-Squares Approach to State Estimation in Linear State Space Models: The Case of Correlated Noise Terms
by
Andreas Galka
Algorithms 2024, 17(5), 194; https://doi.org/10.3390/a17050194 - 4 May 2024
Abstract
In this article, a particular approach to deriving recursive state estimators for linear state space models is generalised, namely the weighted least-squares approach introduced by Duncan and Horn in 1972, for the case of the two noise processes arising in such models being
[...] Read more.
In this article, a particular approach to deriving recursive state estimators for linear state space models is generalised, namely the weighted least-squares approach introduced by Duncan and Horn in 1972, for the case of the two noise processes arising in such models being cross-correlated; in this context, the fact that in the available literature two different non-equivalent recursive algorithms are presented for the task of state estimation in the aforementioned case is discussed. Although the origin of the difference between these two algorithms can easily be identified, the issue has only rarely been discussed so far. Then the situations in which each of the two algorithms apply are explored, and a generalised Kalman filter which represents a merger of the two original algorithms is proposed. While, strictly speaking, optimal state estimates can be obtained only through the non-recursive weighted least-squares approach, in examples of modelling simulated and real-world data, the recursive generalised Kalman filter shows almost as good performance as the optimal non-recursive filter.
Full article
(This article belongs to the Collection Feature Papers in Algorithms for Multidisciplinary Applications)
►▼
Show Figures
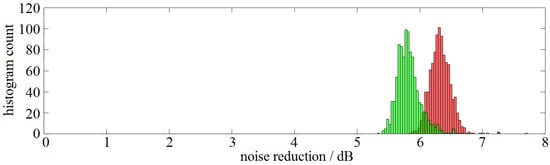
Figure 1
Open AccessArticle
The Algorithm of Gu and Eisenstat and D-Optimal Design of Experiments
by
Alistair Forbes
Algorithms 2024, 17(5), 193; https://doi.org/10.3390/a17050193 - 2 May 2024
Abstract
This paper addresses the following problem: given m potential observations to determine n parameters,
This paper addresses the following problem: given m potential observations to determine n parameters,
(This article belongs to the Special Issue Numerical Optimization and Algorithms: 2nd Edition)
Open AccessArticle
Encouraging Eco-Innovative Urban Development
by
Victor Alves, Florentino Fdez-Riverola, Jorge Ribeiro, José Neves and Henrique Vicente
Algorithms 2024, 17(5), 192; https://doi.org/10.3390/a17050192 - 1 May 2024
Abstract
This article explores the intertwining connections among artificial intelligence, machine learning, digital transformation, and computational sustainability, detailing how these elements jointly empower citizens within a smart city framework. As technological advancement accelerates, smart cities harness these innovations to improve residents’ quality of life.
[...] Read more.
This article explores the intertwining connections among artificial intelligence, machine learning, digital transformation, and computational sustainability, detailing how these elements jointly empower citizens within a smart city framework. As technological advancement accelerates, smart cities harness these innovations to improve residents’ quality of life. Artificial intelligence and machine learning act as data analysis powerhouses, making urban living more personalized, efficient, and automated, and are pivotal in managing complex urban infrastructures, anticipating societal requirements, and averting potential crises. Digital transformation transforms city operations by weaving digital technology into every facet of urban life, enhancing value delivery to citizens. Computational sustainability, a fundamental goal for smart cities, harnesses artificial intelligence, machine learning, and digital resources to forge more environmentally responsible cities, minimize ecological impact, and nurture sustainable development. The synergy of these technologies empowers residents to make well-informed choices, actively engage in their communities, and adopt sustainable lifestyles. This discussion illuminates the mechanisms and implications of these interconnections for future urban existence, ultimately focusing on empowering citizens in smart cities.
Full article
(This article belongs to the Special Issue Algorithms for Smart Cities)
►▼
Show Figures

Figure 1
Open AccessArticle
Mathematical Models for the Single-Channel and Multi-Channel PMU Allocation Problem and Their Solution Algorithms
by
Nikolaos P. Theodorakatos, Rohit Babu, Christos A. Theodoridis and Angelos P. Moschoudis
Algorithms 2024, 17(5), 191; https://doi.org/10.3390/a17050191 - 30 Apr 2024
Abstract
Phasor measurement units (PMUs) are deployed at power grid nodes around the transmission grid, determining precise power system monitoring conditions. In real life, it is not realistic to place a PMU at every power grid node; thus, the lowest PMU number is optimally
[...] Read more.
Phasor measurement units (PMUs) are deployed at power grid nodes around the transmission grid, determining precise power system monitoring conditions. In real life, it is not realistic to place a PMU at every power grid node; thus, the lowest PMU number is optimally selected for the full observation of the entire network. In this study, the PMU placement model is reconsidered, taking into account single- and multi-capacity placement models rather than the well-studied PMU placement model with an unrestricted number of channels. A restricted number of channels per monitoring device is used, instead of supposing that a PMU is able to observe all incident buses through the transmission connectivity lines. The optimization models are declared closely to the power dominating set and minimum edge cover problem in graph theory. These discrete optimization problems are directly related with the minimum set covering problem. Initially, the allocation model is declared as a constrained mixed-integer linear program implemented by mathematical and stochastic algorithms. Then, the
(This article belongs to the Special Issue Convex Optimization Methods and Metaheuristic Algorithms for Power Systems Planning, Operation and Control)
►▼
Show Figures
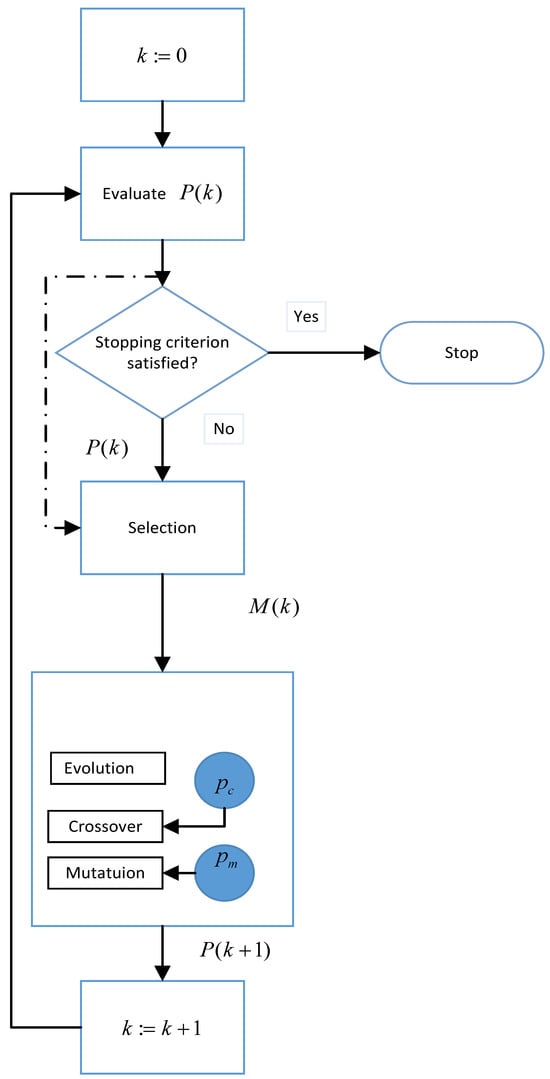
Figure 1
Open AccessArticle
Deep Q-Network Algorithm-Based Cyclic Air Braking Strategy for Heavy-Haul Trains
by
Changfan Zhang, Shuo Zhou, Jing He and Lin Jia
Algorithms 2024, 17(5), 190; https://doi.org/10.3390/a17050190 - 30 Apr 2024
Abstract
Cyclic air braking is a key element for ensuring safe train operation when running on a long and steep downhill railway section. In reality, the cyclic braking performance of a train is affected by its operating environment, speed and air-refilling time. Existing optimization
[...] Read more.
Cyclic air braking is a key element for ensuring safe train operation when running on a long and steep downhill railway section. In reality, the cyclic braking performance of a train is affected by its operating environment, speed and air-refilling time. Existing optimization algorithms have the problem of low learning efficiency. To solve this problem, an intelligent control method based on the deep Q-network (DQN) algorithm for heavy-haul trains running on long and steep downhill railway sections is proposed. Firstly, the environment of heavy-haul train operation is designed by considering the line characteristics, speed limits and constraints of the train pipe’s air-refilling time. Secondly, the control process of heavy-haul trains running on long and steep downhill sections is described as the reinforcement learning (RL) of a Markov decision process. By designing the critical elements of RL, a cyclic braking strategy for heavy-haul trains is established based on the reinforcement learning algorithm. Thirdly, the deep neural network and Q-learning are combined to design a neural network for approximating the action value function so that the algorithm can achieve the optimal action value function faster. Finally, simulation experiments are conducted on the actual track data pertaining to the Shuozhou–Huanghua line in China to compare the performance of the Q-learning algorithm against the DQN algorithm. Our findings revealed that the DQN-based intelligent control strategy decreased the air braking distance by 2.1% and enhanced the overall average speed by more than 7%. These experiments unequivocally demonstrate the efficacy and superiority of the DQN-based intelligent control strategy.
Full article
(This article belongs to the Special Issue Algorithms in Evolutionary Reinforcement Learning)
►▼
Show Figures

Figure 1
Open AccessReview
Insights into Image Understanding: Segmentation Methods for Object Recognition and Scene Classification
by
Sarfaraz Ahmed Mohammed and Anca L. Ralescu
Algorithms 2024, 17(5), 189; https://doi.org/10.3390/a17050189 - 30 Apr 2024
Abstract
Image understanding plays a pivotal role in various computer vision tasks, such as extraction of essential features from images, object detection, and segmentation. At a higher level of granularity, both semantic and instance segmentation are necessary for fully grasping a scene. In recent
[...] Read more.
Image understanding plays a pivotal role in various computer vision tasks, such as extraction of essential features from images, object detection, and segmentation. At a higher level of granularity, both semantic and instance segmentation are necessary for fully grasping a scene. In recent times, the concept of panoptic segmentation has emerged as a field of study that unifies semantic and instance segmentation. This article sheds light on the pivotal role of panoptic segmentation as a visualization tool for understanding scene components, including object detection, categorization, and precise localization of scene elements. Advancements in achieving panoptic segmentation and suggested improvements to the predicted outputs through a top-down approach are discussed. Furthermore, datasets relevant to both scene recognition and panoptic segmentation are explored to facilitate a comparative analysis. Finally, the article outlines certain promising directions in image recognition and analysis by underlining the ongoing evolution in image understanding methodologies.
Full article
(This article belongs to the Collection Traditional and Machine Learning Methods to Solve Imaging Problems)
►▼
Show Figures
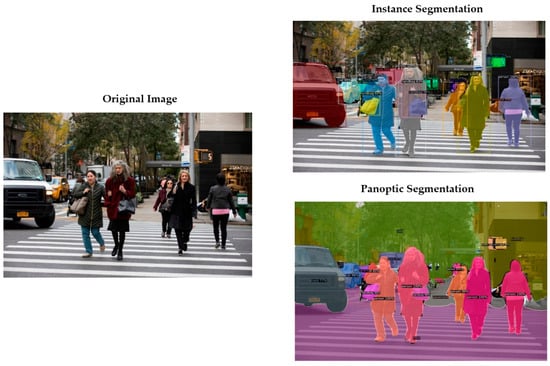
Figure 1
Open AccessArticle
A Data-Driven Approach to Discovering Process Choreography
by
Jaciel David Hernandez-Resendiz, Edgar Tello-Leal and Marcos Sepúlveda
Algorithms 2024, 17(5), 188; https://doi.org/10.3390/a17050188 - 29 Apr 2024
Abstract
Implementing approaches based on process mining in inter-organizational collaboration environments presents challenges related to the granularity of event logs, the privacy and autonomy of business processes, and the alignment of event data generated in inter-organizational business process (IOBP) execution. Therefore, this paper proposes
[...] Read more.
Implementing approaches based on process mining in inter-organizational collaboration environments presents challenges related to the granularity of event logs, the privacy and autonomy of business processes, and the alignment of event data generated in inter-organizational business process (IOBP) execution. Therefore, this paper proposes a complete and modular data-driven approach that implements natural language processing techniques, text similarity, and process mining techniques (discovery and conformance checking) through a set of methods and formal rules that enable analysis of the data contained in the event logs and the intra-organizational process models of the participants in the collaboration, to identify patterns that allow the discovery of the process choreography. The approach enables merging the event logs of the inter-organizational collaboration participants from the identified message interactions, enabling the automatic construction of an IOBP model. The proposed approach was evaluated using four real-life and two artificial event logs. In discovering the choreography process, average values of 0.86, 0.89, and 0.86 were obtained for relationship precision, relation recall, and relationship F-score metrics. In evaluating the quality of the built IOBP models, values of 0.95 and 1.00 were achieved for the precision and recall metrics, respectively. The performance obtained in the different scenarios is encouraging, demonstrating the ability of the approach to discover the process choreography and the construction of business process models in inter-organizational environments.
Full article
(This article belongs to the Special Issue Data-Driven Intelligent Modeling and Optimization Algorithms for Industrial Processes)
►▼
Show Figures
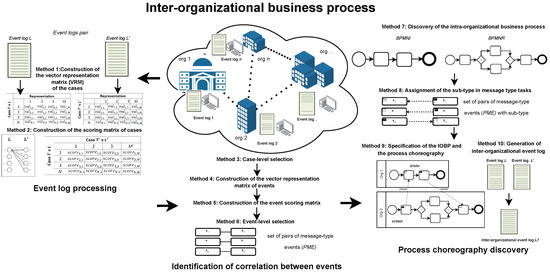
Figure 1
Open AccessArticle
MMD-MSD: A Multimodal Multisensory Dataset in Support of Research and Technology Development for Musculoskeletal Disorders
by
Valentina Markova, Todor Ganchev, Silvia Filkova and Miroslav Markov
Algorithms 2024, 17(5), 187; https://doi.org/10.3390/a17050187 - 29 Apr 2024
Abstract
Improper sitting positions are known as the primary reason for back pain and the emergence of musculoskeletal disorders (MSDs) among individuals who spend prolonged time working with computer screens, keyboards, and mice. At the same time, it is well understood that automated technological
[...] Read more.
Improper sitting positions are known as the primary reason for back pain and the emergence of musculoskeletal disorders (MSDs) among individuals who spend prolonged time working with computer screens, keyboards, and mice. At the same time, it is well understood that automated technological tools can play an important role in the process of unhealthy habit alteration, so plenty of research efforts are focused on research and technology development (RTD) activities that aim to provide support for the prevention of back pain or the development of MSDs. Here, we report on creating a new resource in support of RTD activities aiming at the automated detection of improper sitting positions. It consists of multimodal multisensory recordings of 100 persons, made with a video recorder, camera, and wrist-attached sensors that capture physiological signals (PPG, EDA, skin temperature), as well as motion sensors (three-axis accelerometer). Our multimodal multisensory dataset (MMD-MSD) opens new opportunities for modeling the body stance (sitting posture and movements), physiological state (stress level, attention, emotional arousal and valence), and performance (success rate on the Stroop test) of people working with a computer. Finally, we demonstrate two use cases: improper neck posture detection from pictures, and task-specific cognitive load detection from physiological signals.
Full article
(This article belongs to the Section Databases and Data Structures)
►▼
Show Figures
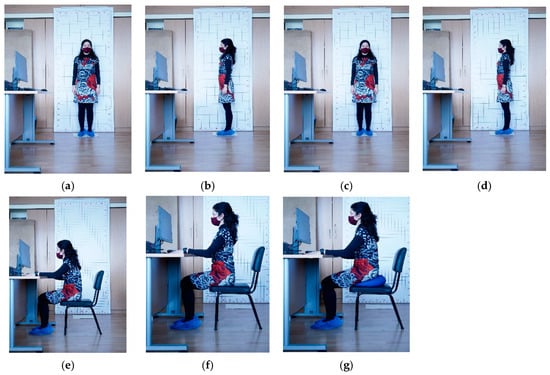
Figure 1
Open AccessArticle
Synesth: Comprehensive Syntenic Reconciliation with Unsampled Lineages
by
Mattéo Delabre and Nadia El-Mabrouk
Algorithms 2024, 17(5), 186; https://doi.org/10.3390/a17050186 - 29 Apr 2024
Abstract
We present Synesth, the most comprehensive and flexible tool for tree reconciliation that allows for events on syntenies (i.e., on sets of multiple genes), including duplications, transfers, fissions, and transient events going through unsampled species. This model allows for building histories that explicate
[...] Read more.
We present Synesth, the most comprehensive and flexible tool for tree reconciliation that allows for events on syntenies (i.e., on sets of multiple genes), including duplications, transfers, fissions, and transient events going through unsampled species. This model allows for building histories that explicate the inconsistencies between a synteny tree and its associated species tree. We examine the combinatorial properties of this extended reconciliation model and study various associated parsimony problems. First, the infinite set of explicatory histories is reduced to a finite but exponential set of Pareto-optimal histories (in terms of counts of each event type), then to a polynomial set of Pareto-optimal event count vectors, and this eventually ends with minimum event cost histories given an event cost function. An inductive characterization of the solution space using different algebras for each granularity leads to efficient dynamic programming algorithms, ultimately ending with an
(This article belongs to the Section Combinatorial Optimization, Graph, and Network Algorithms)
►▼
Show Figures
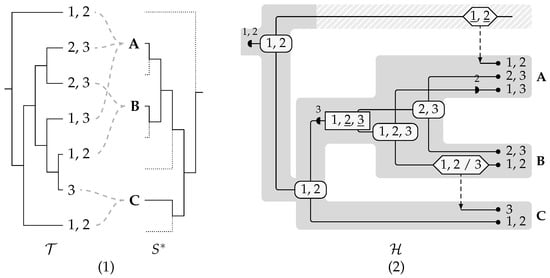
Figure 1
Open AccessArticle
A Linear Interpolation and Curvature-Controlled Gradient Optimization Strategy Based on Adam
by
Haijing Sun, Wen Zhou, Yichuan Shao, Jiaqi Cui, Lei Xing, Qian Zhao and Le Zhang
Algorithms 2024, 17(5), 185; https://doi.org/10.3390/a17050185 - 29 Apr 2024
Abstract
►▼
Show Figures
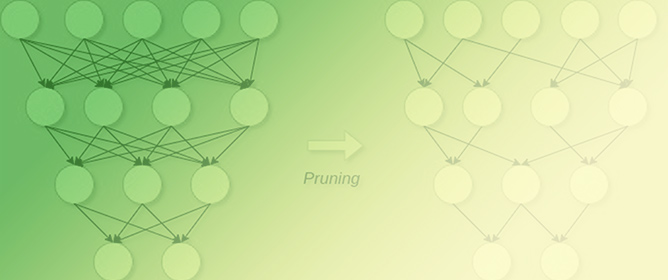
The Adam algorithm is a widely used optimizer for neural network training due to efficient convergence speed. The algorithm is prone to unstable learning rate and performance degradation on some models. To solve these problems, in this paper, an improved algorithm named Linear
[...] Read more.
The Adam algorithm is a widely used optimizer for neural network training due to efficient convergence speed. The algorithm is prone to unstable learning rate and performance degradation on some models. To solve these problems, in this paper, an improved algorithm named Linear Curvature Momentum Adam (LCMAdam) is proposed, which introduces curvature-controlled gradient and linear interpolation strategies. The curvature-controlled gradient can make the gradient update smoother, and the linear interpolation technique can adaptively adjust the size of the learning rate according to the characteristics of the curve during the training process so that it can find the exact value faster, which improves the efficiency and robustness of training. The experimental results show that the LCMAdam algorithm achieves 98.49% accuracy on the MNIST dataset, 75.20% on the CIFAR10 dataset, and 76.80% on the Stomach dataset, which is more difficult to recognize medical images. The LCMAdam optimizer achieves significant performance gains on a variety of neural network structures and tasks, proving its effectiveness and utility in the field of deep learning.
Full article
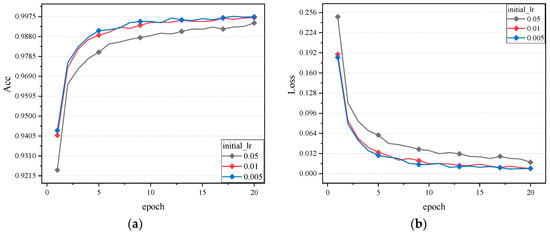
Figure 1
Open AccessArticle
Algorithm Based on Morphological Operators for Shortness Path Planning
by
Jorge L. Perez-Ramos, Selene Ramirez-Rosales, Daniel Canton-Enriquez, Luis A. Diaz-Jimenez, Gabriela Xicotencatl-Ramirez, Ana M. Herrera-Navarro and Hugo Jimenez-Hernandez
Algorithms 2024, 17(5), 184; https://doi.org/10.3390/a17050184 - 29 Apr 2024
Abstract
The problem of finding the best path trajectory in a graph is highly complex due to its combinatorial nature, making it difficult to solve. Standard search algorithms focus on selecting the best path trajectory by introducing constraints to estimate a suitable solution, but
[...] Read more.
The problem of finding the best path trajectory in a graph is highly complex due to its combinatorial nature, making it difficult to solve. Standard search algorithms focus on selecting the best path trajectory by introducing constraints to estimate a suitable solution, but this approach may overlook potentially better alternatives. Despite the number of restrictions and variables in path planning, no solution minimizes the computational resources used to reach the goal. To address this issue, a framework is proposed to compute the best trajectory in a graph by introducing the mathematical morphology concept. The framework builds a lattice over the graph space using mathematical morphology operators. The searching algorithm creates a metric space by applying the morphological covering operator to the graph and weighing the cost of traveling across the lattice. Ultimately, the cumulative traveling criterion creates the optimal path trajectory by selecting the minima/maxima cost. A test is introduced to validate the framework’s functionality, and a sample application is presented to validate its usefulness. The application uses the structure of the avenues as a graph. It proposes a computable approach to find the most suitable paths from a given start and destination reference. The results confirm that this is a generalized graph search framework based on morphological operators that can be compared to the Dijkstra approach.
Full article
(This article belongs to the Section Algorithms for Multidisciplinary Applications)
►▼
Show Figures
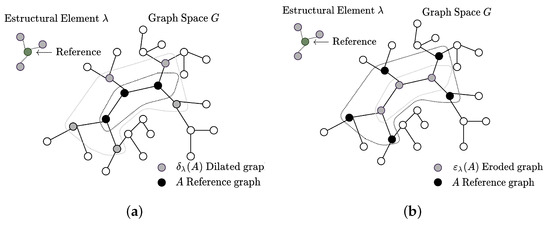
Figure 1
Open AccessArticle
Advancements in Data Analysis for the Work-Sampling Method
by
Borut Buchmeister and Natasa Vujica Herzog
Algorithms 2024, 17(5), 183; https://doi.org/10.3390/a17050183 - 29 Apr 2024
Abstract
The work-sampling method makes it possible to gain valuable insights into what is happening in production systems. Work sampling is a process used to estimate the proportion of shift time that workers (or machines) spend on different activities (within productive work or losses).
[...] Read more.
The work-sampling method makes it possible to gain valuable insights into what is happening in production systems. Work sampling is a process used to estimate the proportion of shift time that workers (or machines) spend on different activities (within productive work or losses). It is estimated based on enough random observations of activities over a selected period. When workplace operations do not have short cycle times or high repetition rates, the use of such a statistical technique is necessary because the labor sampling data can provide information that can be used to set standards. The work-sampling procedure is well standardized, but additional contributions are possible when evaluating the observations. In this paper, we present our contribution to improving the decision-making process based on work-sampling data. We introduce a correlation comparison of the measured hourly shares of all activities in pairs to check whether there are mutual connections or to uncover hidden connections between activities. The results allow for easier decision-making (conclusions) regarding the influence of the selected activities on the triggering of the others. With the additional calculation method, we can uncover behavioral patterns that would have been overlooked with the basic method. This leads to improved efficiency and productivity of the production system.
Full article
(This article belongs to the Special Issue Data-Driven Intelligent Modeling and Optimization Algorithms for Industrial Processes)
►▼
Show Figures
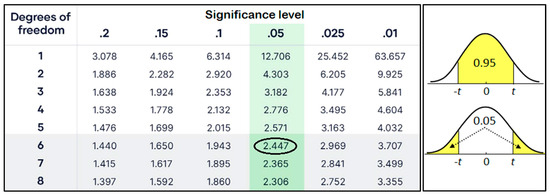
Figure 1
Open AccessArticle
Sub-Band Backdoor Attack in Remote Sensing Imagery
by
Kazi Aminul Islam, Hongyi Wu, Chunsheng Xin, Rui Ning, Liuwan Zhu and Jiang Li
Algorithms 2024, 17(5), 182; https://doi.org/10.3390/a17050182 - 28 Apr 2024
Abstract
Remote sensing datasets usually have a wide range of spatial and spectral resolutions. They provide unique advantages in surveillance systems, and many government organizations use remote sensing multispectral imagery to monitor security-critical infrastructures or targets. Artificial Intelligence (AI) has advanced rapidly in recent
[...] Read more.
Remote sensing datasets usually have a wide range of spatial and spectral resolutions. They provide unique advantages in surveillance systems, and many government organizations use remote sensing multispectral imagery to monitor security-critical infrastructures or targets. Artificial Intelligence (AI) has advanced rapidly in recent years and has been widely applied to remote image analysis, achieving state-of-the-art (SOTA) performance. However, AI models are vulnerable and can be easily deceived or poisoned. A malicious user may poison an AI model by creating a stealthy backdoor. A backdoored AI model performs well on clean data but behaves abnormally when a planted trigger appears in the data. Backdoor attacks have been extensively studied in machine learning-based computer vision applications with natural images. However, much less research has been conducted on remote sensing imagery, which typically consists of many more bands in addition to the red, green, and blue bands found in natural images. In this paper, we first extensively studied a popular backdoor attack, BadNets, applied to a remote sensing dataset, where the trigger was planted in all of the bands in the data. Our results showed that SOTA defense mechanisms, including Neural Cleanse, TABOR, Activation Clustering, Fine-Pruning, GangSweep, Strip, DeepInspect, and Pixel Backdoor, had difficulties detecting and mitigating the backdoor attack. We then proposed an explainable AI-guided backdoor attack specifically for remote sensing imagery by placing triggers in the image sub-bands. Our proposed attack model even poses stronger challenges to these SOTA defense mechanisms, and no method was able to defend it. These results send an alarming message about the catastrophic effects the backdoor attacks may have on satellite imagery.
Full article
(This article belongs to the Special Issue Machine Learning Models and Algorithms for Image Processing)
►▼
Show Figures
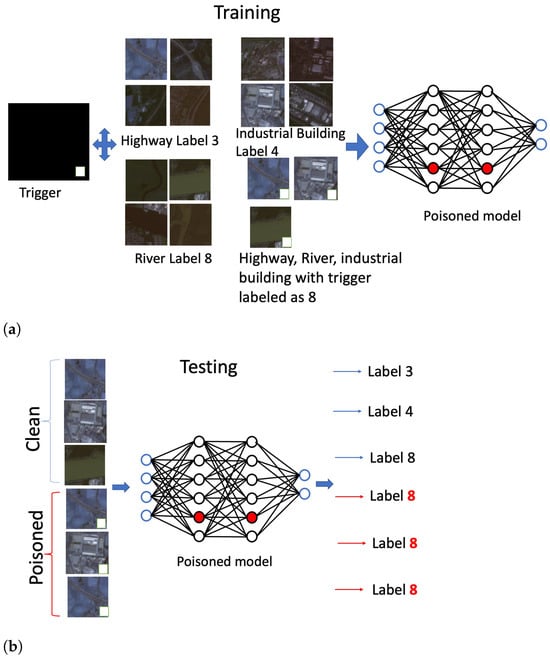
Figure 1

Journal Menu
► ▼ Journal Menu-
- Algorithms Home
- Aims & Scope
- Editorial Board
- Reviewer Board
- Topical Advisory Panel
- Instructions for Authors
- Special Issues
- Topics
- Sections & Collections
- Article Processing Charge
- Indexing & Archiving
- Editor’s Choice Articles
- Most Cited & Viewed
- Journal Statistics
- Journal History
- Journal Awards
- Society Collaborations
- Conferences
- Editorial Office
Journal Browser
► ▼ Journal BrowserHighly Accessed Articles
Latest Books
E-Mail Alert
News
Topics
Topic in
Algorithms, Computation, Entropy, Fractal Fract, MCA
Analytical and Numerical Methods for Stochastic Biological Systems
Topic Editors: Mehmet Yavuz, Necati Ozdemir, Mouhcine Tilioua, Yassine SabbarDeadline: 10 May 2024
Topic in
Algorithms, Diagnostics, Entropy, Information, J. Imaging
Application of Machine Learning in Molecular Imaging
Topic Editors: Allegra Conti, Nicola Toschi, Marianna Inglese, Andrea Duggento, Matthew Grech-Sollars, Serena Monti, Giancarlo Sportelli, Pietro CarraDeadline: 31 May 2024
Topic in
Algorithms, Axioms, Fractal Fract, Mathematics, Symmetry
Fractal and Design of Multipoint Iterative Methods for Nonlinear Problems
Topic Editors: Xiaofeng Wang, Fazlollah SoleymaniDeadline: 30 June 2024
Topic in
Algorithms, Computation, Information, Mathematics
Complex Networks and Social Networks
Topic Editors: Jie Meng, Xiaowei Huang, Minghui Qian, Zhixuan XuDeadline: 31 July 2024

Conferences
Special Issues
Special Issue in
Algorithms
Bio-Inspired Algorithms
Guest Editors: Sándor Szénási, Gábor KertészDeadline: 20 May 2024
Special Issue in
Algorithms
Algorithms for Smart Cities
Guest Editors: Gloria Cerasela Crisan, Elena NechitaDeadline: 31 May 2024
Special Issue in
Algorithms
Algorithms for Games AI
Guest Editors: Wenxin Li, Haifeng ZhangDeadline: 20 June 2024
Special Issue in
Algorithms
Recurrent Neural Networks: algorithms design and applications for safety critical systems
Guest Editor: Grazziela Patrocinio FigueredoDeadline: 30 June 2024
Topical Collections
Topical Collection in
Algorithms
Feature Papers in Algorithms for Multidisciplinary Applications
Collection Editor: Francesc Pozo
Topical Collection in
Algorithms
Feature Papers in Randomized, Online and Approximation Algorithms
Collection Editor: Frank Werner
Topical Collection in
Algorithms
Featured Reviews of Algorithms
Collection Editors: Arun Kumar Sangaiah, Xingjuan Cai