1. Introduction
Guaranteeing energy-efficient reliable data transmission is a fundamental routing issue in wireless sensor networks. Many studies have assumed an ideal link model that guarantees successful transmission within the radio range [
1,
2]. However, recent studies have shown that under realistic circumstances links are highly unreliable due to various factors, such as interference, attenuation, and fading [
3,
4]. Particularly, wireless sensor networks have a higher packet loss ratio than other wireless network environments. Even though a retransmission mechanism is commonly used to recover from corrupted packets, this basic mechanism may considerably increase the number of retransmissions [
5]. Therefore, it is crucial to consider having an energy-efficient reliable data transmission scheme.
Several routing schemes have been proposed to provide reliable data transmission for unreliable wireless links. Reliable Multi-Segment Transport for directed diffusion (RMST) [
6] uses NACK model to guarantee both reliability and the order of fragment arrivals in Directed Diffusion [
7]. Woo
et al. [
8] select reliable routes based on statistical link connectivity obtained from an EMWA estimator. Couto
et al. [
9] propose expected transmission count metric (ETX) to select routes to guarantee high data transmission rate and throughput. PRR×Distance greedy forwarding provides high energy-efficiency and reliability by a tradeoff between packet reception rate (PRR) and distance improvement to destination [
10,
11]. The authors of [
12] propose Dynamic Switch-based Forwarding (DSF) that considers PRR and the low duty cycle networks when it selects the route to reduce sleep latency.
Basically, it is not encouraged to propose a new routing scheme for reliable data transmission in the circumstance where there are various routing schemes already implemented in sensor network applications. The reason is that it is practically not feasible to replace every routing scheme with the new one. Instead, it is more effective to adopt a pluggable modular approach that can be easily applied to an existing routing scheme. However, several issues should be considered for the modular approach to become a generalized solution to provide the reliability of all existing routing schemes. First, only a small amount of additional cost should be incurred in extending the existing routing schemes due to resource constraints such as energy, memory, and computing power. Second, the modular approach should not participate in path selection. This is performed in the network layer and reliability should be offered independently in a lower layer. Third, the modular approach should effectively reduce the number of retransmissions to achieve high energy-efficiency in data transmission.
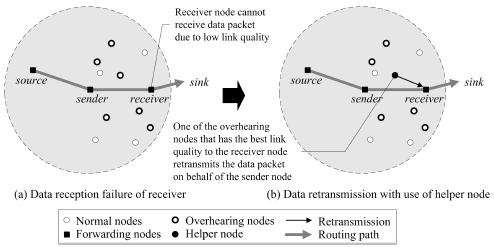
In this paper, we propose a
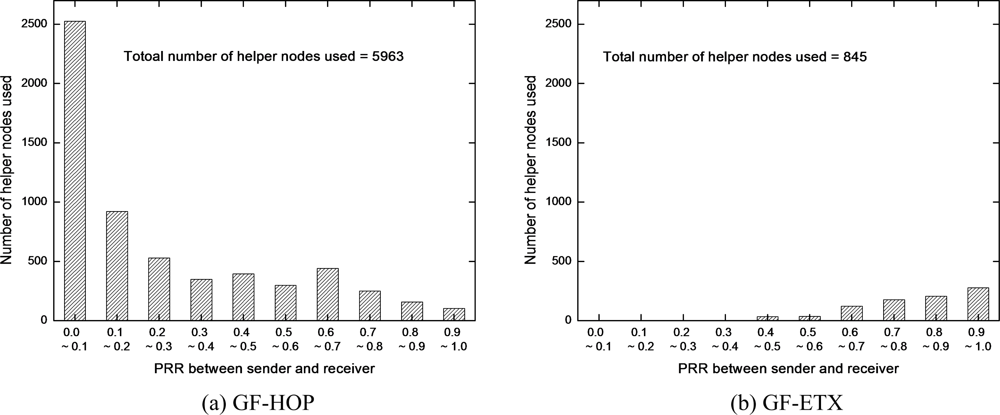
Distributed and Reliable Data Transmission (DRDT) scheme with a goal to efficiently provide reliable data transmission based on the modular approach. DRDT determines whether or not a neighbor node overhearing data packets transmitted to a receiver node will perform retransmission task on behalf of a transmitting node. This node is called a
helper node. If a receiver node is located in an unreliable transmission region from the sender and fails to receive a data packet, the selected helper node retransmits the data packet. This enhances reliability of data transmission. In this case, the link quality of the helper node to the receiver node is superior to that of the sender node to the receiver node. Therefore, DRDT is able to reduce the number of retransmissions and guarantee energy-efficient data transmission. Our contributions are as follows:
DRDT can be applied to all types of existing routing schemes since it operates as a pluggable extension layer under the network layer.
DRDT effectively reduces the number of retransmissions by using helper nodes. The helper node selection is based on the link quality to the receiver node so that the retransmission of the helper node outperforms that of the sender node when the link quality between the sender and the receiver nodes is low.
The helper node selection performs in a distributed manner. The sensor nodes which overhear the data packet decide whether to become helper nodes by themselves without exchanging any information with the neighbor nodes.
DRDT guarantees high energy-efficiency and effectively reduces end-to-end transmission delay.
The remainder of this paper is organized as follows. In Section 2, we explain several schemes that provide reliable data transmission. We describe the proposed scheme in Section 3. The simulation results are presented in Section 4. Finally, Section 5 concludes this paper.
3. Proposed Scheme
3.1. Link Loss Model
Analyzing and simulating a reliable data transmission scheme requires a realistic link loss model. In this paper, we use the PRR as the link quality between two nodes. The PRR ranges from 0 to 1 and is calculated using the following link loss model [
20,
21]:
where,
d is the distance between two nodes,
γ(
d) is a
signal to noise ratio (SNR) for
d,
f is the length of a frame, and
l is the length of a preamble. This model considers various radio parameters, such as a
path-loss exponent (
η) and a
log-normal shadowing variable (
σ). In the simulated environment,
η and
σ are 3.0 and 3.8, respectively.
Equation (1) reflects MICA2 motes that use the NCFSK modulation method and Manchester Encoding. Other detailed information follows the MICA2 specifications [
22].
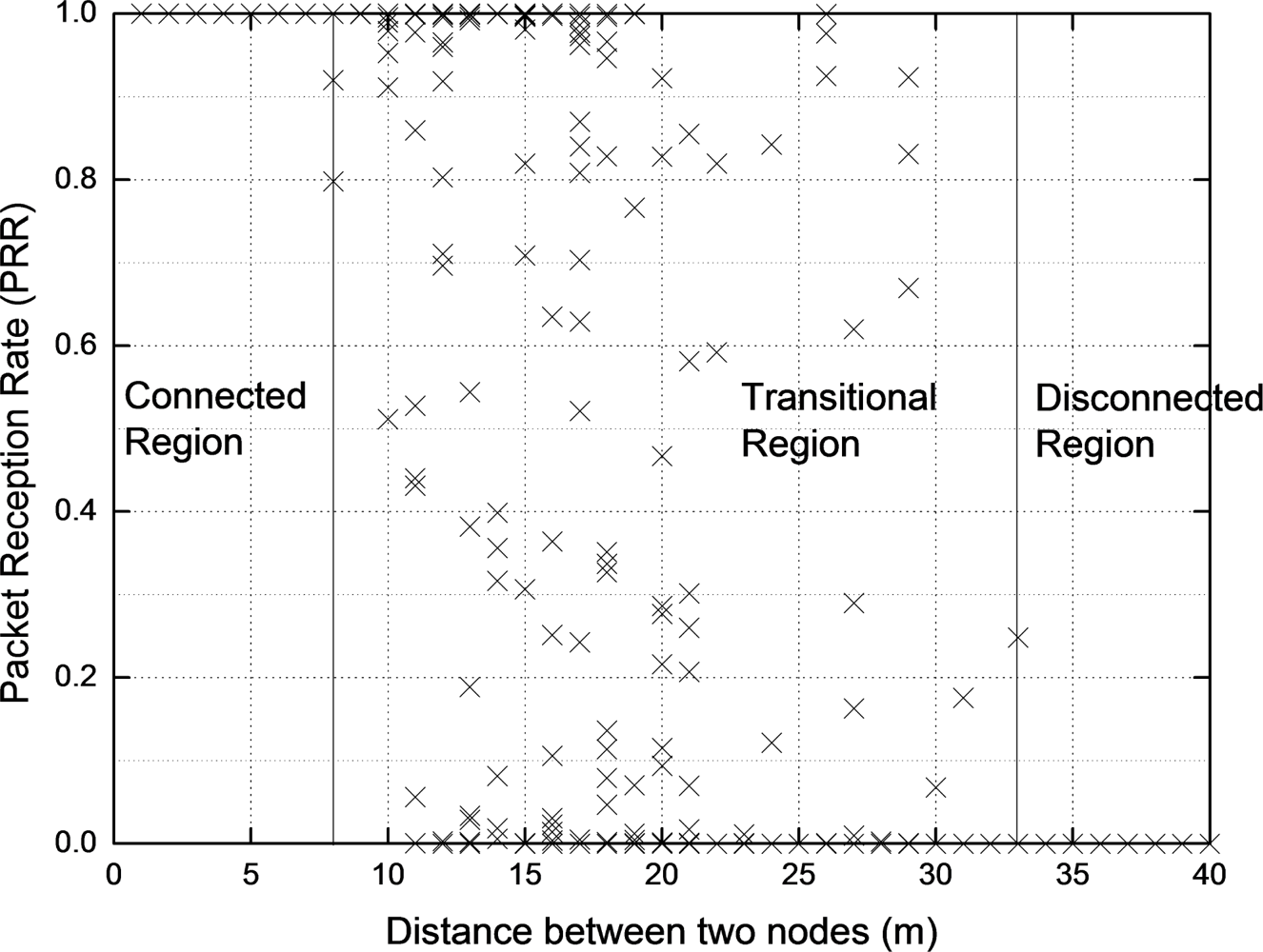
Recent researches [
3,
4,
8,
20,
21] have shown three distinct data reception regions: connected, transitional, and disconnected. In the connected region, nodes can transmit packets reliably in the absence of congestion since PRR is always 1. In the transitional region, some links have high PRR, while others have the opposite. Therefore, when we design a routing scheme, we should consider this region. In the disconnection region, no links or very weak links exist.
Figure 1 depicts the link layer model, where the observed connected region is from 0 to 8
m, the transition region is from 8 to 33
m, and the disconnected region is from 33
m.
3.2. Scheme Overview and Assumptions
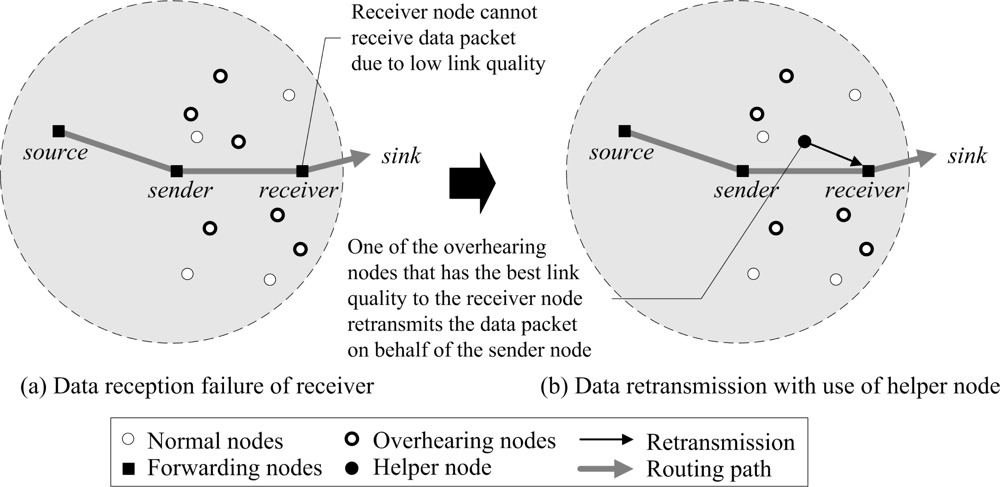
The proposed DRDT scheme guarantees reliable energy-efficient data transmission
via the extension layer that operates under the network layer. The basic idea behind the proposed scheme is the cooperative retransmission of neighbor nodes that overhear the data packet transmitted to the receiver node, so as to increase the data transmission success rate and reduce the number of retransmissions. In
Figure 2, every neighbor node of a receiver that overheard the data packet becomes a candidate helper node. Each decides if it should promote itself as a helper node using waiting time in a distributed manner. At this point, the helper node is selected by considering PRR to the receiver node, so that the number of retransmissions can be reduced. The selected helper node retransmits the data packet on behalf of the sender node when the receiver node failed to receive the data packet due to low PRR (
Figure 2b). The helper node can effectively reduce the number of retransmissions since it uses a better PRR link than the sender node.
DRDT functions based on the following basic and general wireless sensor network environments.
The network has relatively low congestion.
Fixed sensor nodes with constant radio ranges are randomly distributed.
Each sensor node knows itself and its geographical location information via GPS or the distribution-based localization algorithm.
Each node knows the location information of the neighbor nodes and the PRR value between itself and the neighbor nodes by transmitting a ”hello” packet at regular intervals.
The network uses a timeout-based ACK model to offer reliability.
It is assumed that insignificant computing power is required for mathematical operations.
3.3. Distributed and Reliable Data Transmission: DRDT
The proposed scheme DRDT consists of two major phases: helper node selection phase using helper value and transmission phase. Performing the two phases repetitively, DRDT increases the reliability of the data transmission in an energy-efficient way. We first propose the helper value, followed by the helper node selection phase using the helper value.
Helper Value (H)
A helper node, which can retransmit data packet with low cost, should be selected among neighbor nodes that overhear the data packet sent to the receiver node in order for DRDT to provide reliability in an energy-efficient way. The expected cost is defined as the total transmitted bits until the receiver node obtains the data packet [
19]. We first explain the procedure how the helper node retransmits the data packet when the receiver node fails to receive the data packet to calculate the expected cost (
Figure 3).
For the receiver node to obtain the data packet successfully, the expected number of data packet transmissions is
, where
h is the helper and
r is the receiver in these two steps. Similarly, the expected number of control packet transmissions is
, where
s is the sender. We assume that the data packet size ratio of a control packet to a data packet is
λ to calculate the expected cost. Therefore, the expected cost to perform retransmission using a helper node can be written as follows.
As we can see in
Equation (2), minimizing the cost required to use a helper node on behalf of the sender node demands the maximization of the PRR between a helper node and the sender node, as well as the PRR between the helper node and the receiver node. That is, in an attempt to maximize the energy-efficient retransmission using a helper node, a node with a high PRR to both the receiver and the sender nodes is selected as a helper node.
The
helper value (
H) is the criterion to calculate the condition of such a helper node. The helper value is defined as follows:
where
c denotes a current node that is considered as a helper node.
w1 and
w2 are the weighting values. Generally, the data packet size is larger than the control packet size, and therefore, a larger weighting value is applied to the PRR of the receiver node than to that of the sender node.
HPRR(
a,
b) refers to the PRR between nodes
a and
b. It is defined as follows:
In
HPRR (
a,
b), logarithm function rapidly decreases the selected probability when PRR approaches low. In [
10] and [
11], when the number of retransmissions exceeds 10, the transmission is assumed to have failed. Therefore, if the PRR is below 0.1, the helper node cannot retransmit the data packet. Thus, this paper assumes the base of the log to be 10; this value can be changed.
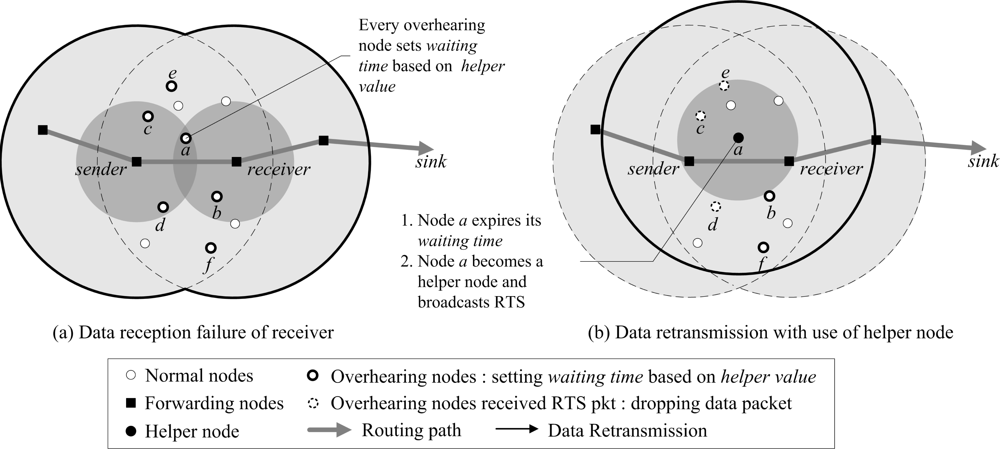
Helper Node Selection Phase
DRDT causes low overhead because every node can decide to be a helper node in a distributed manner. A
waiting time (
W) is used to determine whether or not a node performs retransmission as a helper node. Each node that overhears the data packet transmitted to the receiver node first checks the packet header to determine if the destination is one of its neighbor nodes. If it is, the node waits for the waiting time with respect to its helper value. The waiting time is calculated as follows [
23].
where
δ is the predefined maximum waiting time. According to
Equation (5), the waiting time is obtained shorter, as the helper value increases higher. That is, the closer the helper value is to 1, the higher the probability the node will be selected as a helper node. Once the waiting time expires, a node selects itself as a helper node and broadcasts a request to send (RTS) packet to retransmit the data packet to the receiver node. If the other nodes receive the RTS packet from another node or overhear the data packet being transmitted to the receiver node while the waiting time has not expired, the nodes stop waiting (because they believe that another helper node with a better condition has been selected) and are removed from the helper node selection phase, and the data packets are dropped.
Figure 4 depicts the helper node selection phase based on a helper value. The nodes
a,
b,
c,
d,
e, and
f that overhear the data packet transmitted to the receiver node first calculate the helper values. They set the waiting time with respect to their helper values. In
Figure 4a, the helper value of node
a is 1 since it is located in the connected region where both the sender and receiver nodes overlap. While other nodes
b,
c,
d,
e, and
f can all have helper values of 1 or lower, it is assumed for now that they all have helper values below 1. Therefore, node
a sets the shortest waiting time by using
Equation (5). Having set up the waiting time, node
a selects itself as a helper node and makes other nodes know this by broadcasting an RTS packet. Here, the nodes that receive the RTS packet before their waiting time to be expired completely discard the data packet, as in nodes
c,
d, and
e of
Figure 4b.
If more than one helper nodes are selected in the helper node selection phase, duplicated retransmission is performed. There are two possible scenarios. First, nodes may not receive the RTS packet from selected helper node due to low link quality, as in nodes
b and
f of
Figure 4b. In this case, they keep listening to the channel and still wait for their waiting time. Eventually, several helper nodes can be selected. This problem is easily solved by the transmission phase in the next subsection. The second scenario is that if a current node overhears the data packet transmitted from the helper node, it possibly starts the helper node selection phase again for the same data packet. This causes selecting unnecessary helper nodes over and over. To solve this, the helper node adds a
flag bit set to 1 in the data packet before retransmission to differentiate the data packet from the sender node. By doing so, nodes do not start the helper node selection phase for the data packet from the helper node.
Table 1 shows the pseudo-code of the helper node selection phase.
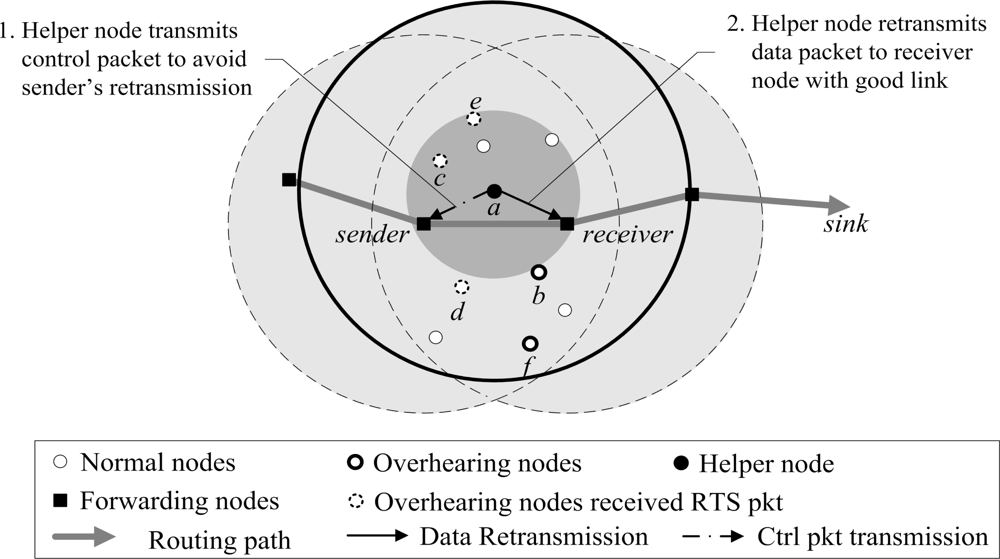
Transmission Phase
A helper node selected transmits an RTS packet once to determine if the receiver node needs retransmissions of the data packet and prevent other nodes from selecting themselves as helper nodes. If the receiver node that has not received the data packet, receives the RTS packet of the helper node, it transmits the clear to send (CTS) packet to the helper node. After receiving the CTS packet, the helper node begins its transmission phase. When it receives several RTS packets, the receiver node only executes the transmission phase for the first RTS packet, and ignores the others, in order to solve the duplicated retransmission problem by several helper nodes. The transmission phase is generally divided into two steps: the control packet transmission step which prevents the retransmission of the sender node and the data packet retransmission step which retransmits the data packet to the receiver node. In the control packet transmission step, the helper node sends out the control packet to the sender node to prevent data packet duplication due to retransmissions of the sender node. The helper node considers the PRR of the sender node, and the number of control packet retransmissions is effectively reduced. This step should be started before the data packet retransmission step since the sender node possibly retransmits the data packet during retransmission of the helper node. In the data packet retransmission step, the helper node on behalf of the sender node that has a low PRR value, retransmits the data packet to the receiver node. At this time the flag bit set to 1 is added in the data packet. Consequently, the helper node reduces the number of retransmissions by delegating the retransmission task from the sender node.
Figure 5 shows the data packet retransmission and the control packet transmission by helper node
a. First, after receiving the CTS packet from the receiver node, helper node
a retransmits the data packet to the receiver node. Helper node
a also transmits the control packet to the sender node and the sender node transmits an ACK packet to the helper node, after receiving the control packet. In the process of transmitting the control packet, if the sender node overhears the data packet transmitted from the helper node, the sender node can transmit an ACK packet in advance, before receiving the control packet. This can prevent unnecessary energy consumption due to the control packet transmission.
Table 2 shows the pseudo-code of the transmission phase.
5. Conclusions
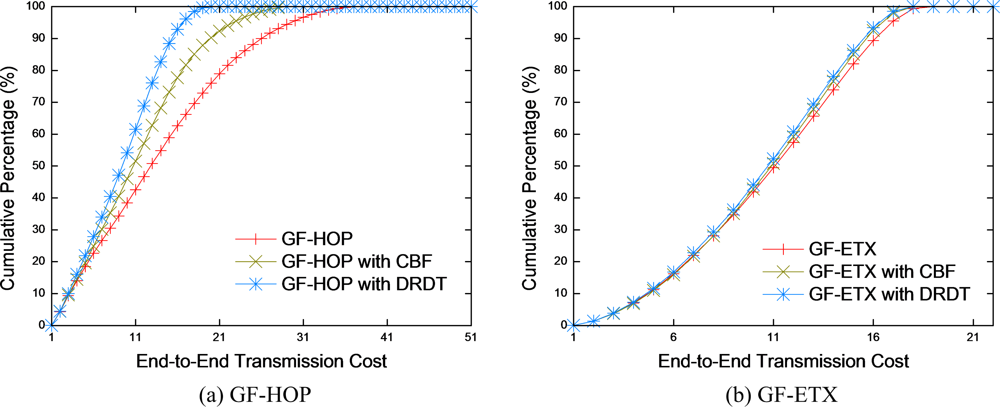
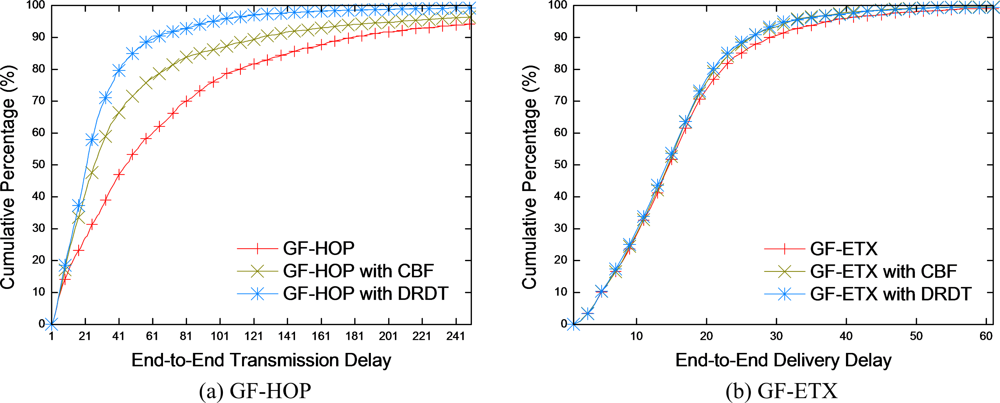
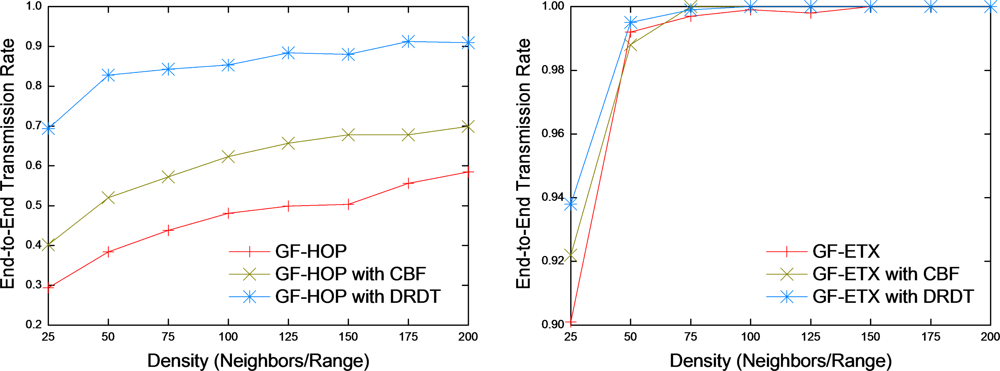
Energy-efficient reliable transmission is a fundamental routing issue in lossy wireless sensor networks. We have presented detail study about existing routing schemes to guarantee reliability in an efficient way. However, these reliable routing schemes only work well for specific applications which means that they cannot be used as a general solution to provide reliability. To solve the problem, we have proposed a DRDT scheme. DRDT enhances reliability in transmission by cooperative retransmission task of helper nodes. Furthermore, DRDT is extendable, as well as adaptable to existing routing schemes since DRDT operates as an extension layer under the network layer. Therefore, we believe that DRDT based on a pluggable modular approach can be a general solution in providing reliability to the existing routing schemes. Simulation results, in which GF-HOP is implanted as a basic routing scheme, indicate that poor performance of GH-HOP can be improved by applying DRDT. DRDT enhances end-to-end transmission cost and reduces its delay as a result of high transmission rate. In case of GF-ETX after applying DRDT, slight improvement is observed over these performance metrics. This means that DRDT performs retransmission task with very low overhead. Furthermore, DRDT demonstrates superiority in data retransmission compared to CBF.
In our upcoming research, we plan to study the scheduling of sensor motes to extend DRDT as a more practical scheme. We expect that consideration of low duty cycle networks helps to prolong operational time. However, end-to-end transmission cannot afford to maintain an always-awake transmission which leads a decrease the number of overhearing nodes. The performance metrics such as end-to-end transmission cost and delay can be reduced since improvements of DRDT depend on the number of overhearing nodes. Therefore, we also plan to analyze the interaction between low duty cycle networks and the number of overhearing nodes. The interesting overhearing phenomenon is expected according to duty-cycle networks.
Acknowledgments
This research was supported in part by MKE and MEST, Korean government, under ITRC NIPA-2010-(C1090-1021-0008) and WCU NRF (No. R31-2008-000-10062-0), respectively.
References
- Al-Karaki, J.; Kamal, A. Routing Techniques in Wireless Sensor Networks: A Survey. IEEE Wirel. Commun 2004, 11, 6–28. [Google Scholar]
- Ingelrest, F.; Simplot-Ryl, D.; Stojmenovic, I. Optimal Transmission Radius for Energy Efficient Broadcasting Protocols in Ad Hoc and Sensor Networks. IEEE Trans. Parallel Distrib. Syst 2006, 17, 536–547. [Google Scholar]
- Ganesan, D.; Krishnamachari, B.; Woo, A.; Culler, D.; Estrin, D.; Wicker, S. Complex Behavior at Scale: An Experimental Study of Low-Power Wireless Sensor Networks; Technical report; CS TR 02-0013; UCLA: Los Angeles, CA, USA, 2002. [Google Scholar]
- Zhao, J.; Govindan, R. Understanding Packet Delivery Performance in Dense Wireless Sensor Networks. Proceedings of ACM International Conference on Embedded Networked Sensor Systems, Los Angeles, CA, USA, November, 2003; pp. 1–13.
- Reason, J.M.; Rabaey, J.M. A Study of Energy Consumption and Reliability in a Multi-hop Sensor Network. SIGMOBILE Mob. Comput. Commun. Rev 2004, 8, 84–97. [Google Scholar]
- Stann, F.; Heidemann, J. RMST: Reliable Data Transport in Sensor Networks. Proceedings of IEEE International Workshop on Sensor Network Protocols and Applications, Anchorage, AK, USA, May, 2003; pp. 102–112.
- Intanagonwiwat, C.; Govindan, R.; Estrin, D.; Heidemann, J.; Silva, F. Directed Diffusion for Wireless Sensor Networking. IEEE/ACM Trans. Netw 2003, 11, 2–16. [Google Scholar]
- Woo, A.; Tong, T.; Culler, D. Taming the Underlying Challenges of Reliable Multihop Routing in Sensor Networks. Proceedings of ACM International Conference on Embedded Networked Sensor Systems, Los Angeles, CA, USA, November, 2003; pp. 14–27.
- Couto, D.S.J.D.; Aguayo, D.; Bicket, J.C.; Morris, R. A High-throughput Path Metric for Multi-hop Wireless Routing. Wirel. Netw 2005, 11, 419–434. [Google Scholar]
- Seada, K.; Zuniga, M.; Helmy, A.; Krishnamachari, B. Energy Efficient Forwarding Strategies for Geographic Routing in Wireless Sensor Networks. Proceedings of ACM International Conference on Embedded Networked Sensor Systems, Baltimore, MD, USA, November, 2004; pp. 108–121.
- Zamalloa, M.Z.; Seada, K.; Krishnamachari, B.; Helmy, A. Efficient Geographic Routing over Lossy Links in Wireless Sensor Networks. ACM Trans. Sens. Netw 2008, 4, 1–33. [Google Scholar]
- Gu, Y.; He, T. Data Forwarding in Extremely Low Duty-cycle Sensor Networks with Unreliable Communication Links. Proceedings of ACM International Conference on Embedded Networked Sensor Systems, Sydney, Australia, November, 2007; pp. 321–334.
- Karp, B.; Kung, H.T. GPSR: Greedy Perimeter Stateless Routing for Wireless Networks. Proceedings of ACM International Conference on Mobile Computing and Networking, Boston, MA, USA, August, 2000; pp. 243–254.
- Ferrara, D.; Galluccio, L.; Leonardi, A.; Morabito, G.; Palazzo, S. MACRO: An Integrated MAC/Routing Protocol for Geographic Forwarding in Wireless Sensor Networks. Proceedings of IEEE International Conference on Computer Communications, Miami, FL, USA, March, 2005; pp. 1770–1781.
- Kotz, D.; Newport, C.; Elliott, C. The Mistaken Axioms of Wireless-Network Research; Technical report; Dartmouth College: Hanover, NH, USA, 2003. [Google Scholar]
- Cerpa, A.; Busek, N.; Estrin, D. SCALE: A tool for Simple Connectivity. Technical report,. 2003. [Google Scholar]
- Cerpa, A.; Wong, J.L.; Kuang, L.; Potkonjak, M.; Estrin, D. Statistical Model of Lossy Links in Wireless Sensor Networks. Proceedings of ACM/IEEE International Symposium on Information Processing in Sensor Networks, Los Angeles, CA, USA, April, 2005; pp. 81–88.
- Draves, R.; Padhye, J.; Zill, B. Comparison of Routing Metrics for Static Multi-hop Wireless Networks. Proceedings of ACM International Conference of the Special Interest Group on Data Communication, Portland, OR, USA, August, 2004; pp. 133–144.
- Cao, Q.; Abdelzaher, T.F.; He, T.; Kravets, R. Cluster-Based Forwarding for Reliable End-to-End Delivery in Wireless Sensor Networks. Proceedings of IEEE International Conference on Computer Communications, Anchorage, AK, USA, May, 2007; pp. 1928–1936.
- Zuniga, M.; Krishnamachari, B. Analyzing the Transitional Region in Low Power Wireless Links. Proceedings of IEEE International Conference on Sensors and Ad Hoc Communications and Networks, Santa Clara, CA, USA, October, 2004; pp. 517–526.
- Zamalloa, M.Z.; Krishnamachari, B. An Analysis of Unreliability and Asymmetry in Low-power Wireless Links. ACM Trans. Sens. Netw 2007, 3, 7. [Google Scholar]
- CC1000 Data Sheet. Texas Instruments Incorporated: Dallas, TX, USA, 2007.
- Kim, M.; Mutka, M.W.; Cho, S.H.; Choo, H. A Dissemination Protocol to Guarantee Data Accessibility within N-Hops for Wireless Sensor Networks. Proceedings of IEEE Hawaii International Conference on Systems Science, Waikoloa, HI, USA, January, 2009; pp. 1–8.
- Cao, Q.; He, T.; Fang, L.; Abdelzaher, T.F.; Stankovic, J.A.; Son, S.H. Efficiency Centric Communication Model for Wireless Sensor Networks. Proceedings of IEEE International Conference on Computer Communications, Miami, FL, USA, May, 2006; pp. 1–12.
- Leong, B.; Mitra, S.; Liskov, B. Path Vector Face Routing: Geographic Routing with Local Face Information. Proceedings of IEEE International Conference on Network Protocols, Boston, MA, USA, November, 2005; pp. 147–158.
- Frey, H.; Stojmenovic, I. On Delivery Guarantees of Face and Combined Greedy-face Routing in Ad Hoc and Sensor Networks. Proceedings of ACM International Conference on Mobile Computing and Networking, Los Angeles, CA, USA, September, 2006; pp. 390–401.
© 2010 by the authors; licensee Molecular Diversity Preservation International, Basel, Switzerland. This article is an open-access article distributed under the terms and conditions of the Creative Commons Attribution license ( http://creativecommons.org/licenses/by/3.0/).